Researchers have claimed that Facebook’s inbuilt security systems are “not effective enough” at stopping automated identity theft, after running a large-scale infiltration of the network using Socialbots.
In their paper, “The Socialbot Network: When Bots Socialise for Fame and Money”, researchers from the University of British Columbia describe how they managed to collect private data from thousands of complete strangers on Facebook, and infiltrate their friend networks, using “socialbots”.
The researchers – Yazan Boshmaf, Ildar Muslukhov, Konstantin, Beznosov and Matei Ripeanu – explain that a socialbot is automated software that can control a social networking account, and can perform basic functions such as posting messages and friend requests.
Importantly, socialbots attempt to pass themselves off as being a real, living human being rather than computer code.
 Although Facebook puts steps in place to try to avoid the automated creation of accounts, the researchers relate how it would be possible to use online services to break CAPTCHAs, and populated their bogus accounts’ profile images with attractive photos from HotOrNot.
Although Facebook puts steps in place to try to avoid the automated creation of accounts, the researchers relate how it would be possible to use online services to break CAPTCHAs, and populated their bogus accounts’ profile images with attractive photos from HotOrNot.
Fake Facebook status updates were also easy to generate, using an API provided by iheartquotes.com for random sayings.
The researchers warn that socialbots can infiltrate friend networks by connecting to users, and could even be used to spread misinformation and propaganda to influence others.
Furthermore, a socialbot can be used to harvest personal information such as email addresses and phone numbers.
Bring many socialbots together and you have a Socialbot Network (SbN), under the control of one person.

The researchers built an Socialbot Network consisting of 102 Socialbots and a single botmaster, and ran the operation for eight weeks. During that time the SbN made 8,570 friend requests and recorded all of the profile information it was able to access from its newly found “friends”.
And it wasn’t just people who accepted the bogus friend requests who leaked personal information – the private data of other users who had not been infiltrated was also exposed.
In all, the researchers’ socialbots made Facebook friends with 3,055 people and grew its extended network to a total of 1,085,785 profiles.
Interestingly, one of the researchers’ findings was that the more friends someone has on Facebook, the more likely they are to accept a friend request from a socialbot.
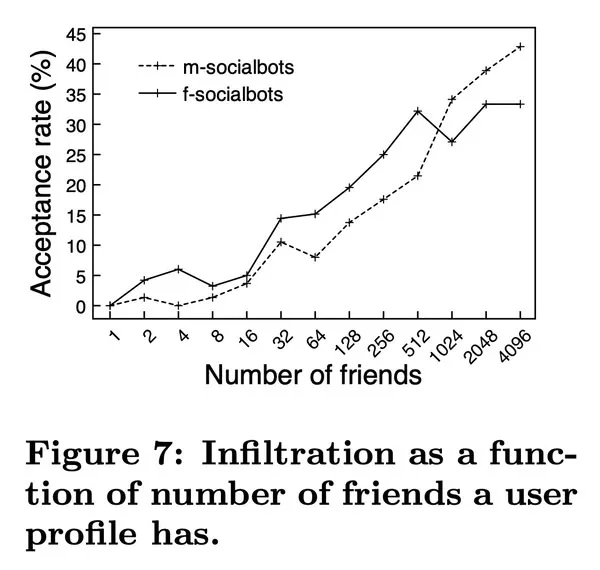
Once the socialbots had befriended one person, they would then attempt to become Facebook friends with their friend’s friends, and so on.. As they became more embedded within friend networks, the acceptance rate of friend request reached 60%.
With their automated data-slurping network the researchers were able to gather 35% of all the personally identifiable information found on their direct networks, and 24% from extended networks. These bots also managed to gather 46,500 email addresses and 14,500 home addresses.
On average, each socialbot collected 175 new “chunks” of publicly-unaccesible users’ data per day.
Clearly there’s a lesson for Facebook users to learn there about the need to carefully vet who you allow to become your Facebook friend, and what information you choose to share online.
The researchers also felt that Facebook’s inbuilt security systems, known as the Facebook Immune System (FIS) should be improved. They found that FIS only blocked 20% of the accounts used by the socialbots – and this was only because of feedback from suspicious users who flagged the account as spam.
Curiously, all of the blocked accounts were posing as female users.
In the researchers’ opinion, Facebook’s security team isn’t taking the threat of automated accounts seriously enough:
“In reaction, we asked ourselves: what assumptions are made by the FIS that might be problematic? The answer came directly from the authors of the FIS: they state that ‘fake accounts have limited virality because they are not central nodes in the graph and lack trusted connections. They also have no unique data or history’.
“Hence, we conjecture that the FIS does not consider fake accounts as a real threat. Fake accounts, however, are one of the main [online social network] vulnerabilities that allow a botherder to run a large-scale infitration campaign. Detecting and blocking such accounts – as early as possible – is the main challenge that [online social network] security defenses like the FIS have to overcome in order to win the battle against an SbN.”
By the end of the eighth week, the researchers voluntarily dismantled their Socialbot network – not because it had caught the attention of Facebook’s security team, but because of the amount of internet traffic it was generating.
“In total, the SbN generated approximately 250GB inbound and 3GB outbound traffic.”
 Facebook’s security team is unlikely to look kindly on people who conduct experiments such as that done by the university researchers, and users are reminded that under Facebook’s terms of service you are not allowed to create fake profiles, should use your real name, and should only collect information from other users with their consent.
Facebook’s security team is unlikely to look kindly on people who conduct experiments such as that done by the university researchers, and users are reminded that under Facebook’s terms of service you are not allowed to create fake profiles, should use your real name, and should only collect information from other users with their consent.
The topic of whether the researchers’ Socialbot Network experiment was right or not, is a topic for another day. But whatever its right or wrongs, it certainly presents an interesting illustration of just how easy it would be to automate identity theft on Facebook.