Never let it be said that malware authors don’t continue to find innovative ways to prevent their creations from being detected.
A new strain of the Snatch ransomware reboots PCs it has just infected into Safe Mode.
As many Windows users will be aware, Safe Mode is a method of booting up a Windows system deployed when attempting to diagnose a problem and resolve software conflicts.
So why would the Snatch ransomware want a PC to boot up in Safe Mode?
Because Safe Mode turns off all those pesky programs which might be interfering with your Windows computer’s operation – such as, for instance, anti-virus software which might have detected a rogue process behaving in a suspicious fashion by encrypting all the documents on your hard drive.
Sophos’s team of researchers produced a video showing the ransomware in operation:
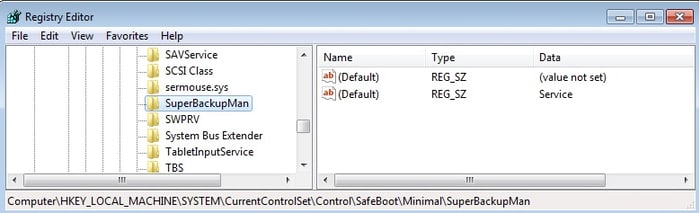
The ransomware installs itself as a Windows service called SuperBackupMan. The service description text, “This service make backup copy every day,” might help camouflage this entry in the Services list, but there’s no time to look. This registry key is set immediately before the machine starts rebooting itself.
The SuperBackupMan service has properties that prevent it from being stopped or paused by the user while it’s running.
The malware then adds this key to the Windows registry so it will start up during a Safe Mode boot.
Sophos’s researchers say that they have found evidence of several related attacks around the world against organisations, all of which “were later discovered to have one or more computers with RDP exposed to the internet.”
Worryingly, Sophos reports that the Snatch gang are different from other criminals spreading ransomware insomuch as they are not primarily focused on just extorting money – but also stealing data with the intention of later holding it for ransom or leaking it online.
Their recommendation beyond patching and running up-to-date anti-virus software if you want to reduce the chances of being hit?
“Sophos recommends that organizations of any size refrain from exposing the Remote Desktop interface to the unprotected internet. Organizations that wish to permit remote access to machines should put them behind a VPN on their network, so they cannot be reached by anyone who does not have VPN credentials.”
Sounds sensible to me.



I wonder if you do notice the pc going into safe mode unintentionally, if you then immediately turn the power off and then boot with a windows Pe to try and find and remove the infection, you might just have minimal files lost. This way your not starting up your infected system but booting off a media / USB or CD image.
Yep, I had the same thoughts Chris. I imagine you would have a good chance of cleaning it that way. Or at least moving your files to a safe place and then just re-formatting the machine before the malware has a chance to run.