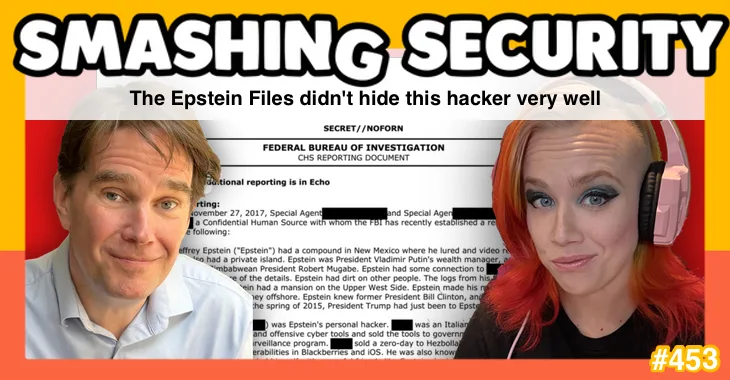
Supposedly redacted Jeffrey Epstein files can still reveal exactly who they’re talking about – especially when AI, LinkedIn, and a few biographical breadcrumbs do the heavy lifting.
Sloppy redaction leads to explosive claims, and difficult reputational consequences for cybersecurity vendors, and we learn how trust – once cracked – can be almost impossible to fully restore.
Elsewhere, the spotlight turns to insider threat in the age of AI, after a senior US cybersecurity official uploads sensitive government material into the public version of ChatGPT. Oops.
All this, and much more, in episode 453 of Smashing Security with cybersecurity veteran and keynote speaker Graham Cluley and special guest Tricia Howard.
Listen on Apple Podcasts | Spotify | Pocket Casts | Other... | RSS
More episodes...
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
We created the internet and told people to click on things, and then we created security and said, don't click on things. What? Obviously people are going to click on things. So, it's... Anyway.
Smashing Security. Episode 453. The Epstein files didn't hide this hacker very well. with Graham Cluley and special guest, Tricia Howard. Hello, hello, and welcome to Smashing Security, episode 453. My name's Graham Cluley. And I'm Tricia Howard. Tricia, welcome back to the show. Lovely to have you here once again.
Oh my gosh, thanks for having me again. Are you kidding me? This is great.
Now, since we last spoke, you have changed jobs. You've moved from one cybersecurity firm and you're helping set up a brand new one, aren't you?
I am. Yes, I just joined as head of marketing at a startup focused on insider threat.
Oh, okay. Sounds interesting. Well, more to come, no doubt, when you unveil yourselves to the world. Yes. And just to remind people, you're head of marketing now, but what's your background in cybersecurity? Where's your expertise been, Tricia?
So I started back as a theater major who ended up accidentally in sales and moved all the way through marketing and tried some security research. And I've kind of dabbled in everywhere. So where my heart lies is in the technical malware analysis, your zero day stuff, the really fun. And I try and make those stories sound very interesting and creative and musical most of the time.
It is so fascinating how people can come from a wide variety of backgrounds and end up in this ridiculous world of cybersecurity. And people can bring so many capabilities and unique talents because of that. It's good that we're not getting everyone from the same pool, isn't it?
100%. 100%. Well, and who's more equipped than an actor to deal with something whenever something goes wrong? Listen, let me tell you, there is no stress like hopping on stage when you have a critical prop that is missing somehow. And now you have to make it out in front of hundreds of people who are expecting you to be perfect, by the way. We are made for this. We deal with failure all the time. We are made for cybersecurity.
Well, before we kick off, let's thank this week's wonderful sponsors, Mita, Passwork and Banta. We'll be hearing more about them later on in the podcast. This week on Smashing Security. We're not going to be talking about how Notepad++ was hijacked by state-sponsored hackers for months, pushing targeted users to malicious updates. You'll hear no discussion of... How an app designed to help you quit watching porn was found to be leaking intimate details about users' sexual urges. And we won't even mention... How cybersecurity firm Microworld Technologies, the makers of eScan antivirus, was hacked to push out malware to its customers. So, Tricia, what are you going to be talking about this week?
I'm going to be talking about learning the difference between public and private chat GPT the hard way. And I'm going to be hearing accusations that Jeffrey Epstein hired a hacker and what that might mean for the rest of us. All this and much more coming up on this episode of Smashing Security. I'd hope so. Yeah, they're doing it, presumably, because there's information they don't want to share. There's something which they want to keep secret, which can be unlikely for governments. I know our natural inclination is to think they're keeping this secret for malicious or malevolent purposes. It can be for legitimate, justifiable reasons that they don't want certain information getting out into the public domain. I have seen it in headline. I haven't looked at anything yet, but man, when will it stop? Well, yeah, exactly. I mean, and they're saying, of course, that there's a lot of information which hasn't been released still. And if you go to the DOJ's website, it's kind of complicated to use because you've got to go through each individual link and try and piece it together. Wow. What a weird cosplay.
Isn't it just? Gmail.world. Anyway, that's one way in which you can begin to peruse all this stuff if you are so interested. But like I said, we're talking millions of pages. And one of the documents in there has caused some ripples in recent days in the cybersecurity industry, because buried in the Epstein files is a document from 2017, when an unnamed FBI informant made a claim. They claimed that Epstein had his own personal hacker. Now, I don't know whether to be surprised by that or not, because I think a lot of people with a lot of money may well have a legitimate reason for hiring a hacker.
Yeah, for sure.
I mean, it may be for the benefit of their own operational security. They may want to hire a hacker just to say, you know, am I protected? Is my information secure? Can I prevent myself from being hacked? Maybe Jeffrey Epstein was acquainting himself with people who might have the methods for hacking into his organisation and reading his emails. And he may be slightly nervous about that. You can easily understand.
Couldn't imagine why. I mean, it was all above board.
Yeah. Anyway, the thing is, this document came to light. It has been dug out. But, of course, it's been redacted. And the name of the alleged hacker, as well as the informant, has been blacked out. It's hidden from view. But the document goes on to tell us various pieces of information about this alleged hacker who it claimed was in contact with Jeffrey Epstein. It says he's an Italian citizen. It says where he was born in Italy. It tells us that he was known for finding zero-day vulnerabilities in iOS and BlackBerry and Firefox. It tells us even that he sold his company to a major cybersecurity firm, which they name in the document. It says he sold his company to them in 2017. It tells us he became a vice president at that company following the acquisition. So how long do you imagine it takes people to work out who this redacted individual, this alleged hacker, actually is? I know. It's honestly rather petty, isn't it? Instead of just saying what it is, it's we're going to dangle these carrots around, knowing the community that they're talking to, by the way, which is made up of a bunch of us who literally put the carrots together. I see what you mean. I mean, I can totally see how you might imagine they're kind of dangling this for us as almost a parlor game. But the truth is, I think this was done through incompetence. I think that—
Oh man, that's so much less fun. It is less fun. I'm sorry. But you know, it took me about two minutes to work out the name of the only person this could be. And judging by online discussions I've seen, everyone else pretty much figured it out just as quickly. And some people just took that information as to where he was born and what he did and the company that he went to work for, they put it into an AI and it just spat out the answer immediately back to them. No. In fact, this is exactly what we tell people not to do on social media, which is kind of funny. Being careful about putting out these little breadcrumbs in our digital presences, literally to avoid what happened.
Oh, yeah. Yeah, absolutely. And I can understand the challenge to those agents who are tasked with the job of going through millions of documents and redacting details.
Especially with the content. Yes.
Yes, absolutely. So, I mean, it may be that they didn't pay enough attention to this. I want to be really clear. This document contains allegations from a confidential FBI informant. They're not proven facts. This is just one source making claims. We have no way of knowing how reliable that source was. But what is clear, if you look up places like jmail.world or DOJ's website, Epstein and this particular individual were in contact. There were emails, albeit fairly mundane communications, you know, arranging meetings and things. But where it gets interesting, I think, for the cybersecurity world is that the informant's claims, if you take them at face value, they paint quite an alarming picture. So they allege that this alleged hacker developed zero day exploits, as we know, sold them to multiple governments, including the United States and the UK, and also allegedly to Hezbollah as well. Apparently it was paid for with a trunk full of cash and that he helped establish a Middle Eastern government's cyber surveillance program as well. Again, these are unverified claims from a single source. We don't know if any of this is true. But if we look through the implications here, what about this company that acquired this guy's startup back in 2017? They are one of the biggest names in enterprise cyber security. Their software runs on so many hundreds of thousands of endpoints across countless major organisations worldwide. Their technology is trusted to protect sensitive systems, critical data all over the planet, right? Now, imagine you are a CISO at a Fortune 500 company who's a client of that particular well-known cybersecurity firm, which it appears hired this guy that the allegations were made about by this informant. And you're reading these headlines over your morning coffee. What's going through your mind? What would be going through your mind at that point?
Oh man, I think my initial reaction would just be like woof, that's rough. I don't even know because when you're thinking oh man that's such a different level of threat I think too. Anytime you're dealing with anything governmental I think the impact is just so much stronger and in the private sector oh man I don't know, I honestly are just speechless.
Yeah, because even if the chance of there being an actual problem are incredibly small, even if this is all just unsubstantiated rumour from a single informant that's leaked out because of the Epstein files being published, you're now going to have to answer some questions. Your board might ask you, hang on, don't we use that company's software? Your security team's going to ask. Someone's going to want to know if there's any possibility, however remote, that there could be vulnerabilities or backdoors in the software that your firm is now running. And what are you going to tell them? You don't know. All you can do is say, well, you know, it's probably all right, but you haven't got total confidence there. And this is the thing when it comes to trust, when it comes to cybersecurity, it's incredibly hard to build trust, but it's so, so easy to damage and fracture trust. And so this humongous security vendor who hired this guy who bought his technology, bought his company, they haven't commented on any of this as far as I'm aware. And honestly, what are they going to say? They're going to say, oh, we vetted him when we acquired his company and we're confident he didn't leave any back doors behind when he left. And hopefully that's right. But some people are still going to be nervous. And that guy, meanwhile, set up his own identity security company. What do their customers think? If they have even the teeniest, tiniest suspicion that their CEO might have engaged in some shady practices in the past, it makes you nervous, doesn't it? You may think it's a safer thing to do to go with someone else for which there aren't any people spreading rumors about.
I mean, that's the brand impact of this, right? Anytime we talk about a major incident, brand impact very closely follows. And this is a terrible example of that. I mean, because now not only do you have the potential technical issues, but now you have the social implications of this as well. So we've seen this with some other vendors who have made decisions to keep certain hate speech things alive on their platforms, etc. And the way that the community and the rest of the world responds to that. So now not only are you having to justify that you need this product in the first place because often security is trying to fight for budget anyway. Now you have this solution and they're like, yo, man, we can't have anything that comes close to touching the Epstein thing, obviously. So, yeah, that's just a whole other thing. It's kind of scary. This whole grey market where researchers are finding unpatched vulnerabilities and selling them to governments.
Yeah, and at what speed, right?
Well, let's take a moment now to thank one of this week's sponsors, Meter. Now, if you've ever worked in IT and especially networking, you'll know when the network's working, nobody notices. When it isn't, everybody notices. The problem is that most business networks are a mess of different providers, tools, dashboards, contracts, and crossed fingers. And somehow, despite all that complexity, they're expected to be fast, secure, reliable, and magically fix themselves. And that's where Meter comes in. Meter builds networks from the ground up. They deliver a complete, full-stack networking solution, wired, wireless, and cellular, all as one integrated service. And this is genuinely full-stack. Meter designs the hardware, writes the firmware, builds the software, manages the deployment, and runs the support. They even take care of things like ISP procurement, routing, switching, firewalls, VPNs, DNS security, SD-WAN, and multi-site networking. In other words, fewer vendors, fewer dashboards, fewer who owns this problem conversations, and far fewer late-night panic attacks. Meter's approach is about real control, proper visibility, and networks that behave themselves. And for IT leadership, it means something almost mythical in networking, predictability. If you're responsible for keeping the business online, you really should check out Meter. So go to meter.com slash smashing to book a demo now. That's M-E-T-E-R dot com slash smashing. And thanks to Meter for supporting the show. Tricia, what have you got for us this week? Oh, boy. Well, it's also governmental. Yeah, not recommended, is it?
I would say that if you were looking at good cybersecurity hygiene practices, putting government sensitive documents into the public one is not high on my list. Right. But I don't know, maybe I'm old fashioned. So here's why I find this story so freaking fascinating, because as we get new technologies in AI and all these other wonderful digital connected things, the easier it is for bad things to happen with significantly less technical barrier to entry. So depending on what was in the documents, right, this could have been a potential massive breach that happened by the government head.
And this is the head of the cybersecurity and infrastructure security agency who you would think would understand about cybersecurity, you know, and the defense of data. Right.
I mean, you'd think so. That I thought that that was implied, but I don't know, it's 2026. Maybe we should just throw it all out the window. So, it's so interesting to me that as technologists, as security people, we love to focus on the technical problem, right? And what is amazing to me about that is that every technical problem was still created by a human. Even everything that comes out of ChatGPT, that was built off of a ton of human interactions that are now collated, right? So, arguably, every threat is a human threat. And especially when you're dealing with stuff like this. What's even scarier is they actually did have tools and things in place for DLP and all that stuff, which did fire. It did alert. Right. And nobody caught it even still. Oh. Yeah. Not until after it had already happened. Yay. So this actually happened last summer, 2025, and they're only just now coming out with what has happened. Yeah. Big scary.
In defense of this person who is the head of CISA, they're relatively new to the job, aren't they? It's an interim. Until fairly recently, it was Jen Easterly who was in charge of CISA, who I think was fairly beloved by the cybersecurity community. And she was fired by the Trump administration. And she's now heading up the RSA conference, which is going to be happening in San Francisco in a couple of months. And I even heard that the US government isn't going to be sending officials from CISA to the RSA conference, which for anyone who isn't aware, is probably the biggest cybersecurity conference. It's the biggest collection of minds and knowledge and the industry in the entirety of the United States, if not the world. It's one of the biggest cybersecurity events in the world. So they're boycotting it because the former head of CISA is now in charge of it, which seems, again, rather short-sighted. I can't imagine that Jen Easterly would have been uploading these documents to ChatGPT. Yeah, it's
Funny. I don't think so either. It's so funny. Yeah, I agree. I'm with you on that. I do want to take a second here. Insider threat is easy to do. It is because frankly, a lot of insider threat is not malicious. We created the internet and told people to click on things. And then we created security and said, don't click on things. What? Obviously, people are going to click on things. So it's anyway, I am a huge defender of users in a lot of ways because it is often an accident. I don't necessarily think this was intentional, obviously, but that's a big accident. And I think when we're talking about the governmental level and this was the head, right? So that's the other issue. It's not as if this was an underling who did this. This was the head of the organization. Who answers to that? Who is there? What is the failback mechanism for whenever the person who is the leader is the one actually making the mistake? It's a very interesting issue. And it's going to get even worse the more that we integrate these AI tools. Because again, the easier that something is to use for a non-technical person, the easier threats can happen. Because you're just allowing people opportunities to upload very sensitive information, even things that may not seem like it's sensitive to you. It might not be, but to your competitor, that might be exactly what you need. So it's, oh, it's such an interesting time that we are in. I've always talked about the human threat in security. I think it's huge. I don't think that we focus on it enough, even though we talk about it a lot, we don't do it right. And this is another example of how this can happen. In a very real, very real scenario, government documents were now at risk. Yay.
And I'm reading this article right now, which we've linked to in the show notes from Politico. And it suggests that normally the Department of Homeland Security does have a policy of blocking access to AI tools. It doesn't allow people normally to upload these kind of things. And it sounds like the interim head, they actually were given permission. They requested permission to use it, were given the permission. And then the alarm bells went off, and it's like, whoa, no. It's the age-old story of the bosses think, well, those rules don't apply to me.
I mean, I can't imagine where they got that idea. I mean, it's not like that's happening in everywhere else in the government too. So I guess, you know, why would this be any different?
You're so naughty. You know, I'll get complaints.
Oh, sorry. Cut that out then.
I get all the feedback, you know. I never, ever say anything bad like that. But you've gone ahead and you've upset a percentage of our, to be honest, most of them have probably left already. But anyway. Sorry. Okay. Before we go any further, we've got time to chat quickly about one of our sponsors today, Vanta. So a question for you. What do you worry about at two o'clock in the morning when it comes to your company's cybersecurity? Is it, do we actually have the right controls in place? Is it, are our vendors quietly on fire? Or the truly terrifying one, why are we still trying to do all this with spreadsheets? Well, if that sounds like you, enter Vanta. Vanta takes all that painful manual security busy work, chasing all the evidence, filling out questionnaires, updating the same spreadsheet for the thousandth time, and it automates it. Their trust management platform continuously monitors your systems, pulls everything into one place, and helps keep your security program audit-ready all of the time. And yes, it uses AI, but in the useful way, flagging risks, streamlining evidence collection, and fitting neatly into the tools you already use. So you can move faster, scale with confidence, and maybe even sleep through the night. Get started today at vanta.com slash smashing. That's V-A-N-T-A dot com slash smashing. And thanks to Vanta for supporting the show. And welcome back. And you join us at our favorite part of the show, the part of the show that we like to call Pick of the Week. Pick of the Week is the part of the show where everyone chooses to sign a light. It could be a funny story, a book, a movie, a record, a podcast, a website, or an app. Whatever they wish. It doesn't have to be security-related necessarily. Well, last week, my pick of the week was the movie Polite Society, which I greatly enjoyed. And watching that sent me down a rabbit hole to find other things that the writer and director of that movie had done, which brought me to a place I'd never been before. I give you We Are Lady Parts. Are you familiar with lady parts at all, Tricia? Or should I not ask such an indelicate question?
Let's see. How do you want to answer this, Graham?
Anyway, I'll save your blushes. We Are Lady Parts is a sharp, funny, punk-powered TV sitcom from Channel 4 here in the UK about an all-female Muslim punk band trying to survive friendship and find their way in the world. All seen through the eyes of a geeky microbiology PhD student. She's on the lookout for love and she finds herself recruited to be the band's unlikely lead guitarist and it's great, amazing. It's really fun, it's properly funny, great characters, cracking dialogue and it's got a super soundtrack. They have songs "Bashir with a Good Beard" and my personal favorite "Voldemort Under My Headscarf." It's an awful lot of fun. It came out a few years ago, I think it may still be going. There's been at least two series of it so far. Oh wow, that's great. But it's smart, it's not smug, it's political without being preachy, it's refreshingly free of all those normal cliches you get in sitcoms. The episodes are bite-sized, it's well worth your time. Each episode's about I don't know 20 or 25 minutes, really entertaining, really enjoyed it and it is We Are Lady Parts and that is my pick of the week.
Amazing. I hope that it's on BritBox. Oh, I hope so. It sounds amazing.
I'm sure we'll be able to find somewhere you can watch it. Oh, sure. I'm sure. What's your pick of the week? Oh, my goodness. So are these stories which have been interspersed with Zygons and Ice Warriors and Doctor Who baddies like that?
Oh, yeah. Oh, yeah. I mean, there's a Dalek and a Cyberman right on the cover.
Well, they have to do that, don't they?
They gotta exterminate. You can't have anything Doctor Who that doesn't have Dalek involved.
Is it just Hamlet or are there other Shakespeare stories? There are others. In fact, Romeo and Juliet makes an appearance. Let's see, what else do they have here? Midsummer Night's Dream. Oh, cool. Are these set out as plays or are they set out as prose? I mean, could you perform, if you wanted to, the Doctor Who version of Midsummer Night's Dream?
I would be insulted if someone didn't. Yes, you can. You can, in fact. It is actually set up like a play. It's great.
So if I ever wanted to delight my Doctor Who loving friends with my particular bottom, I'd be able to go ahead and do that.
That's right.
Fantastic stuff. Okay, the Shakespeare notebooks, we will link to it in the show notes. And that just about wraps up the show for this week. Thank you so much, Tricia, for joining us. I really appreciate it. Where can people follow you online and find out what you're up to?
Ah, yes. The best place to find me is on LinkedIn, believe it or not, under Tricia Kicks SaaS. So that's S-A-A-S. If you just search Google for Tricia Kicks SaaS, I think it's the first one that comes up. So that's about it. And thank you so much. It's such a joy to talk to you and be part of the show. So thank you for having me again.
Always a pleasure. And of course, Smashing Security is on social media as well. You can find me, Graham Cluley, on LinkedIn, or you can follow Smashing Security on Blue Sky or Reddit or Mastodon. And don't forget, to ensure you never miss another episode, follow Smashing Security in your favourite podcast app such as Apple Podcasts, Spotify and Pocket Casts. For episode show notes, sponsorship info, guest lists and the entire back catalogue of 453 episodes, check out smashingsecurity.com. Until next time, cheerio, bye bye. Sayonara. Well, you've been listening to Smashing Security with me, Graham Cluley. And thanks so much to Tricia Howard for joining us this week. And to this episode's sponsors, Mita, Vanta and Passwork. And you know who else we've got to thank? Yep, it's going to be our chums over on Smashing Security Plus, our Patreon platform. Let me dig into the hat right now and pick out some names. Who have we got here? OK, we're going to thank this week Ryan Hall, Teppotastic, sounds less like a person and more like a limited edition kitchen appliance. Adina Bogut O'Brien, John W, 636B, still refusing to confirm whether they are a person or a software build. MJ Lee, who could easily be three consultants in a trench coat. Steve B, who presumably is good friends or arch enemies with John W. You Ask Leo who arrives both with answers and an exclamation mark and of course our latest privacy conscious recruit example name the patron saint of placeholder text everywhere. Well would you like the opportunity to have your name read out occasionally at the end of the show? All you've got to do is join Smashing Security Plus for as little as five dollars a month. You'll become part of our merry band and get early access to episodes without all of the annoying ads. Just head over to smashingsecurity.com slash plus for more details of that. And you can support us in other ways, of course. You can like, you can subscribe, you can leave a five-star review, or just tell your friends about the show. Go on, spread the word. Every little bit helps, and it really makes all the effort worthwhile. Well, I will be back next week, and I hope you will too. I expect you to have your lug holes pressed firmly against your smartphones as I tell you the latest crazy stories of cybersecurity with a fabulous special guest. Until then, cheerio. Bye-bye.
Host:
Graham Cluley:
Guest:
Tricia Howard:
Episode links:
- Notepad++ hijacked to serve malware in targeted attacks – Notepad++.
- Porn-quitting app caught leaking users’ sexual habits – 404 Media.
- MicroWorld Technologies’ eScan anti-virus update turned into a malware delivery system – Morphisec.
- Jmail.World.
- Informant told FBI that Jeffrey Epstein had a ‘personal hacker’ – Techcrunch.
- Confidential informant statement given to FBI – US Department of Justice.
- Post by Graham Cluley – LinkedIn.
- Trump’s acting cyber chief uploaded sensitive files into a public version of ChatGPT – Politico.
- We are Lady Parts – Channel 4.
- We are Lady Parts trailer – YouTube.
- “Bashir with a good beard” by We are Lady Parts – YouTube.
- “Voldermort under my headscarf” by We are Lady Parts – YouTube.
- Doctor Who: The Shakespeare Notebooks – Penguin.
- Smashing Security merchandise (t-shirts, mugs, stickers and stuff)
Sponsored by:
- Passwork – a reliable secrets manager and password management solution.
- Meter– Network infrastructure for the enterprise. Get a free personalised demo.
- Vanta – Expand the scope of your security program with market-leading compliance automation… while saving time and money. Smashing Security listeners get $1000 off!
Support the show:
You can help the podcast by telling your friends and colleagues about “Smashing Security”, and leaving us a review on Apple Podcasts or Podchaser.
Join Smashing Security PLUS for ad-free episodes and our early-release feed!
Follow us:
Follow the show on Bluesky, or join us on the Smashing Security subreddit, or visit our website for more episodes.
Thanks:
Theme tune: “Vinyl Memories” by Mikael Manvelyan.
Assorted sound effects: AudioBlocks.