Why is a cute Star Wars fan website now redirecting to the CIA? How come Cambodia has become the world’s hotspot for scam call centres? And can a WhatsApp image really drain your bank account with a single download, or is it just a load of hacker hokum?
All this and much more is discussed in the latest edition of the award-winning “Smashing Security” podcast by computer security veterans Graham Cluley and Carole Theriault, joined this week by Allan Liska.
Warning: This podcast may contain nuts, adult themes, and rude language.
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Smashing Security, episode 419: Star Wars, the CIA, and a WhatsApp malware mirage with Carole Theriault and Graham Cluley.
Hello, hello, and welcome to Smashing Security episode 419. My name's Graham Cluley.
It's none other than Allan Liska. Hello, Allan.
Now, coming up on today's show, Graham, what do you got?
And I found out that the only way they build ships is if they're donated.
So I went and I bought a bunch of Rebel LEGO ships and donated them to the library because I cannot allow the local library to be a harbinger of the dark side.
The films themselves have been going for so many, many years. There's lots of them out there. There's the official ones, and there's the ones created by the community as well.
For instance, there's a website called starwarsweb.net.
And if you went to starwarsweb.net, where once you saw pictures of R2-D2 and Lego sets and kids dressed up as Jedis, now you will be redirected to the CIA's website.
It located a now defunct network of websites that were used by spies and informants in various countries around the world to covertly communicate with the CIA.
One man said he was captured by the Iranian authorities. He was imprisoned for a decade and subjected to torture. Really horrible stuff.
Instead, it would be something starwarsweb.net.
And if you went there, you could see lots of messages about football and videos and message boards and chatting about soccer.
But if you looked at its code, you found some JavaScript located where its search box was.
So any other of these web forums, I'm sure you've been on lots of these things over the years, Carole, and you too, Allan.
And if you look at the script, you'd find that the search box, they'd actually called it password.
That was the identifier they used on the search box because all the informant had to do was go to the website and in the search box, enter a password.
And if they entered the right password, a secret messaging window would pop up on this normally completely legitimate looking Star Wars or Iranian goals website.
And through that, they could covertly communicate with their handlers at the CIA. They could write their message and the CIA could communicate back with them via this website.
The bad thing was that the code, as I said, wasn't very well hidden because it identified that that search box was a password. And in fact, the password was hardcoded into it.
So it was possible for anybody to go to the website and with a little bit of kung fu in their browser, they could actually unlock and cause this messaging window to pop up.
So there were lots and lots of websites which were all using the same or similar code. So there was IranianGoals.com, for instance, which was set up for one informant.
There was this Star Wars website set up for another. There was another one called IranianGoalKicks. And so it went on and on and on.
And the CIA had made it too obvious which of these websites had actually been meddled with.
And furthermore, another one of the mistakes the CIA made— I mean, this is basic kind of OPSEC fail.
Was that the IP addresses pointing to these sites were sequential, meaning that after discovering one, it was pretty straightforward for anyone investigating to find others that were very likely in the same network.
You must see problems that all the time, Allan, when you're hunting down these ransomware gangs.
I mean, it sounds like a combination of Google doxing and a little bit of quick searches and you find those and we find stuff like this all the time when in fact that's how we can sometimes connect ransomware groups like, oh, they're basically just using the same code.
And apparently they'd intensified their hunt for informants after Barack Obama publicly outed a secret Iranian nuclear facility in 2009.
So they went looking, thinking, who's doing this informing? And with a little help from Google, they discovered these suspicious sites.
Now, unfortunately, they did not responsibly disclose their discovery of the vulnerability to the CIA. Funny that, isn't it?
And it was only when the CIA realised that quite a lot of its informants were being rounded up or weren't making contact anymore, for reasons you can probably understand, that they closed down the operation in 2013.
So this has serious consequences.
Because of course, I'm putting on my 2025 hat on and going, how hilarious.
But if your website is getting archived, if someone's able to dig around in old versions of the website where maybe you had been a bit more careless, that's not so good, is it?
You don't have to have a lot of expensive technology. You don't have to use apps that may be hacked. But the execution is just as important as the idea.
He's fascinated to know which websites were being created and run by the CIA on the quiet.
So using tools the Wayback Machine, IP history lookups, DNS records, he's managed to uncover many more CIA-affiliated domains, and they all had these sort of sequential IP addresses, had telltale URL structures.
They often included the word news in the domain. And interestingly, some even targeted US allies Brazil, Germany, France, and Italy.
So it wasn't just nations which would normally be considered hostile to the United States, I don't know, Canada at the moment, Greenland.
It wasn't just them who were being targeted.
The situation today is that more than 350 such websites have been identified due to the CIA's carelessness, including beauty websites, fitness websites, entertainment websites, a fan page for Johnny Carson, of all people.
And there've been all kinds of techniques.
In 2015, there were sources inside Israel's spy agency Mossad, which claimed that members of ISIS and al-Qaeda had been sending coded messages through eBay, for instance.
That'd be fairly obvious.
But you could also have a real-time strategy game where if you made certain troop movements, or in-game actions that might transmit a message or send a message covertly to someone else.
Or I even was thinking, well, you know, these games where you explore the environment, you could take over a lighthouse in a video game and send Morse code messages by flashing the light to someone on the other side of the gaming world.
Yeah. So these things are possible. I was also reading some other ideas people had. If you were in close vicinity to your contact, right?
Imagine you wanted to communicate with someone who was fairly close, but you didn't want to use the phone.
So the CIA set up the Star Wars website and etc. to send these things. But, well, maybe we can learn a lesson from General David Petraeus. He's a former director of the CIA.
He was having a bit of a naughty affair with the woman writing his biography.
And what they'd do is one of them would go into the account, write a message for the other one, and save it as a draft.
Unfortunately for them, in that particular case, a family friend of Petraeus reported to the FBI that she thought she was receiving harassing emails from someone, and the FBI investigated, found the IP address of the person sending them, ended up back with Petraeus's biographer.
Maybe she was getting a bit jealous of this friend of Petraeus, and they discovered that that person was logging into David Petraeus's Gmail account and saving drafts when communicating with him.
All kind of embarrassing.
And there's a new report out about Cambodia becoming the center of the global scam economy, largely driven by Chinese organized crime.
It's the same thing in Myanmar, where it's still the Chinese organized crime that's running it. But Cambodia really is becoming a huge part of this global scam network.
And in fact, the estimates are that it accounts for about 50% of the GDP in Cambodia now.
Obviously those are huge numbers and they're so big that, you know, basically it allows the people who run them to control whatever politicians and law enforcement and everything else and be able to operate kind of unscathed.
So it is a huge, huge problem in Cambodia.
I mean, it's a huge problem in many parts of the world, but I think Cambodia doesn't get the kind of attention that Myanmar and Laos normally do.
Again, these Chinese criminal gangs are able to operate there because they're able to control so much of the government because they make so much money, right?
And it's one of these things where— and I know you all have talked about this before where it's bad for everybody involved.
Obviously, the people around the world getting scammed, it's terrible.
But the people who are forced to do the scamming also are living in horrible conditions and often can be killed if they try and leave or try and escape or anything like that.
And if you've seen, I think it was the New York Times that did an exposé on this, but there was these huge, vast camps of these huge warehouses where they're all working, you know.
It's just a bunch of computers in there and people, you know, without passports, right?
Yeah, there may be as many as a million people who are being basically forced into slave labor to carry out these attacks. But, you know, that's a million people.
How many are they reaching out to every day, and how many people are getting scammed that we just don't know about because it's so underreported as well.
Can it handle it, or is this something where they need help from other bodies internationally?
I mean, we saw this just a few months ago where the authorities in Thailand raided one of these compounds in Myanmar and rescued 7,000 people that were being held captive there.
7,000 just in one compound in Myanmar. You know, it's going to take the larger governments to step in and do this.
And yes, because it's the right thing to do, but also protect your own damn citizens, you know, who are getting scammed by this.
Because their interests may be different in this case.
Well, you know, it is interesting that on one hand the Chinese government stepping in to try and help, on the other hand they're not stopping the actual Chinese mafia from setting up these centers and so on.
So this same can be said for any government where on the one hand they're trying to help with one thing, but on the other hand they're causing the problem. Certainly not the U.S.
government. We never go around the world causing problems, but other governments engage in that.
It's like, oh, really? Do I have to use this? To be honest, I think I'm a bit old for all the learning new apps now, Carole. It's a bit of a struggle.
I would rather go to StarWarsWeb.net.
It's how you buy things in some parts of the world. Thank goodness I'm not living in one of those. But it is everywhere.
Do you know that WhatsApp was turned down by Facebook way back in 2009?
And there was a bit of irony because soon after the sale, the WhatsApp co-founder Brian Acton defended his decision to sell the company while encouraging students at Stanford to delete their accounts.
BuzzFeed quote Acton saying, "You go back to the Silicon Valley culture and people say, 'Well, could you have not sold?' And the answer is no," he said, referring to the decision to make the rational choice to take a boatload of money.
So I don't know, maybe a moral quandary. Perhaps, but I digress. Okay. What was the first non-English market, do you think? I love having a little few weirdo facts.
So India really dominates with the WhatsApp. So it's a big, fat, well-used service.
And of course, as we've seen again and again, when something becomes effectively ubiquitous or is used by a huge glut of people, it becomes a sexy target for baddies.
You know, that move targets to WhatsApp to get more cozy and personal. And there was that pink theme scam. Do you remember that? This was in 2021.
In fact, the scam presented itself as an official update, so users were warned not to click the fake APK download link that spreading around on the WhatsApp groups.
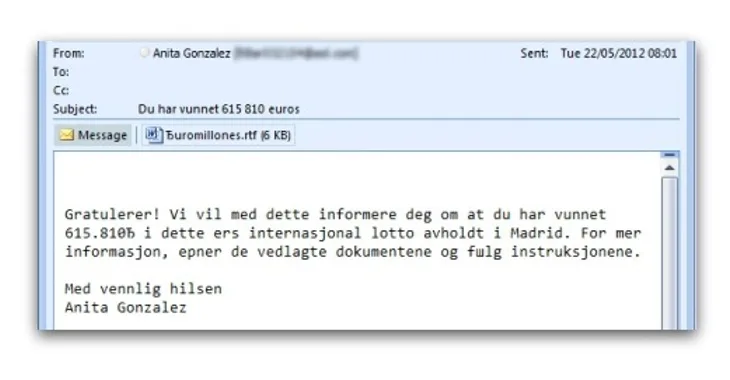
But a smattering of news articles from India this morning reported that a new WhatsApp threat is doing the rounds, one that has a nasty financial twist.
So here I'm thinking that this could be perhaps a good story for Smashing Security. We haven't covered WhatsApp in a while, and this attack seems to have a new twist.
And the reports are all coming out of India, where we know WhatsApp is incredibly popular.
Maybe he's enjoying a delicious mango lassi on his break.
And the message is asking him if he knows the person in the attached photo.
But you want to know who that person is because maybe you do know them, right?
I would fall for it if it was, you know, can you tell me about this bottle of wine?
Anyway, Madia's probably hovering his finger over the image and decides, you know, I got to see who it is. And in doing that, he downloads the image.
And this ends nowhere good because within minutes, Madia's phone was reportedly compromised, and unauthorized transactions drained the equivalent of about $2,000 from his bank account.
And it seems investigations revealed that malware had secretly infiltrated his phone via the image file, so that when Magyar downloaded the image, it was game over.
The malware was silently installing on his device.
So WhatsApp patched this critical security vulnerability in its app for Android, which had remained unpatched for at least 3 months after it had been discovered.
And had it been exploited, it could have allowed remote hackers to compromise Android devices and potentially steal files and tap messages.
Now, all the reports I've seen, they've only come out today.
They're all— there's a smattering of all the reports are in the show notes, but they're all papers that are— I can validate, but I can't verify as well as the ones that I can do in my own country.
Now that is technically possible and there have been vulnerabilities found like that in the past, but it would be interesting to hear what WhatsApp have to say about this.
I would imagine that if there is such a vulnerability, they'd be rolling out a patch pretty darn quickly.
I mean, I know this is going way, way back, but I mean, that used to be a common exploit vector for Internet Explorer.
That's one of the reasons why nobody uses Internet Explorer anymore is, you know, you were constantly finding in the image rendering process, you were constantly finding new vulnerabilities to the point where it just became almost impossible for Microsoft to keep up with the patching.
But it is really rare now. I'm guessing the articles didn't mention, but did they say what kind of image it was?
Because there are certainly some types that are you have to do this with others.
I found one from April 17th, so that's about 6 weeks ago now. I'm dubious. I think that if this had been confirmed, we would be hearing quite a lot about this.
From other sources, including Meta itself. Now, sometimes these hoaxes can spread a lot. Everyone seems to be mentioning the same guy as well, this Madja.
I'm wondering if this person lost a whole load of money and is thinking, oh crumbs, you know, I've lost some money or I spent it on the horses.
Maybe I can blame it on a hacker instead. I don't know, I'm just skeptical, I'd love to hear what Meta and WhatsApp have to say about it.
And you have to ask yourself, is that single source trustworthy? And you can't assume that because other news outlets cover it, that it is trustworthy.
The problems we have here are that all the articles are extremely light on technical details. Like what kind of image? Is it a vulnerability that was being exploited?
The articles cite one guy, Madhya Pradesh, but in none of the articles did I see him quoted. There's no comment or response from WhatsApp, as you say, Graham.
And unnamed security experts and their companies. I mean, give me a break. Who in the cyber spokesperson rat race would not want their name in lights?
Now, if you are a WhatsApp user, reluctant ones like us or avid fans like 99% of my mom friends, here are a few safety tips that you should definitely consider.
Enable two-factor authentication by using the secret PIN provided by the WhatsApp service.
Make sure you remove old or unknown contacts regularly and block unwanted or unknown contacts.
But yeah, in this case, I think we need to wait for further evidence before we believe there is a current WhatsApp image scam that will steal all your money.
I think the thing that we benefit from is we're aware that we're susceptible to being able to fall for things like this.
And if this does turn out to be a mistake or, you know, a false report, it's good to get out there that this thing is floating around that may or may not be true.
I mean, I can imagine lots and lots of people doing it. I can understand. But well done, you. Well done on you for realizing this probably isn't true.
Now, the folks at MetaCompliance know that real cybersecurity starts with your people. That's why their approach is different.
They don't just deliver generic cybersecurity training, they personalize it.
MetaCompliance has created a free security awareness planner, your 12-month roadmap to building a culture of cyber awareness.
It's designed to save you time, increase staff engagement, and make it easy to plan meaningful campaigns that reduce risk.
Download it today and take the first step towards smarter, more effective cyber awareness. Just visit metacompliance.com/planner. That's metacompliance.com/planner.
Head to vanta.com/smashing to learn more. That's vanta, V-A-N-T-A,.com/smashing. And thanks to Vanta for sponsoring Smashing Security.
Do your end users always, and I mean always without exception, work on company-owned devices and IT-approved apps? Oops, I didn't think so.
So my next question is, how do you keep your company's data safe when it's sitting on all those unmanaged apps and devices?
It ensures that every user credential is strong and protected, every device is known and healthy, and every app is visible.
And welcome back, and you join us at our favorite part of the show, the part of the show that we like to call Pick of the Week.
Could be a funny story, a book that they've read, a TV show, movie, a record, a podcast, a website, or an app. Whatever they wish. It doesn't have to be security related necessarily.
Or a Norwegian fella called Thor, or Thor Heyerdahl? Oh, this guy was a hero when I was a child. I remember hearing about this guy.
And the other day, my lovely wife and I were cuddled up on the sofa and we thought, what shall we do? How shall we entertain ourselves? And we started talking about the Kon-Tiki.
Let me tell you what it was. In 1947, there was a journey made by a Norwegian explorer called Thor Heyerdahl. And what he did was he led an expedition.
He decided to cross the Pacific Ocean between South America and the islands of Polynesia. Right, it's about 8,000 miles.
And he wanted to demonstrate that ancient South Americans could have settled Polynesia rather than the theory which had been at the time that they had come from Asia.
And so he set off on this little raft for 8,000 miles. It took him 111 days, but they managed it.
And it is an incredible story of both endurance and death defiance because they really could have come a cropper a number of times.
And there is on YouTube the actual film of the expedition, which won the Oscar in 1951 for best documentary. It's brilliant.
There was a coral reef. They realised they could have died. They were dealing with these huge sharks and whales, which were attacking them as well. This is all in the movie.
And they had a little parrot as well called Lorita. But it is an incredible story. Once they eventually got to the islands, of course, it was uninhabited.
And so they then had to try and make contact with locals because they had nothing with them to help them to prove that they'd managed it. It's an incredible story.
You can watch it on YouTube. It's called Kon-Tiki, K-O-N-T-I-K-I. And I'd really recommend it. It's an hour spent, if you don't mind watching old movies in black and white.
For goodness' sake, he travels for 111 days, 8,000 miles on a bit of cardboard, effectively, halfway across the Pacific.
And can I tell you, Mrs. Cluley greatly enjoyed it as well. So we had a good old time.
And said, "Yes, Graham, this sounds a wonderful documentary. I'm going to watch it as soon as I hang up on this call."
And so, Still Standing is a Canadian show with host Johnny Harris.
He basically travels to small towns in Canada and does a profile of them, and at the end of his profile, he does a 5-minute sitcom set.
But basically the idea is, you know, there are all these small towns in Canada that are struggling, but they're finding ways to survive and change and adapt, you know, as factories close, as fisheries close, etc.
They're finding ways to continue to survive and even thrive. And we get to go to all these amazing small towns in Canada, not on a cardboard raft.
We get to go with Johnny traveling with his crew, and we get to meet all of these cool people in these small towns doing fun, interesting things.
Maybe they're making dream catchers.
They're doing all of these fun things, and they're just— It's just really filled with interesting people, and it's just— after a day of misery, it's just so nice to sit back and watch happiness, and it makes me want to go visit every small town in Canada.
Ah!
But Amazon Prime in the US has all 10 seasons of it.
And, you know, and I love Johnny Harris because, you know, he is so sincere and just so interested in all of these people's lives that it, you know, that it just adds to the enhancement.
So the Yeti and I were away this weekend in this tiny town called Bruton, B-R-U-T-O-N, in Somerset.
And it's a tiny, tiny foodie village and is home to one of the Hauser Wirth galleries. And it's a pretty swank village. Like, the Spar looks like Whole Foods, right?
The Spar is like your corner shop where you go get your whatevers. And this gallery is so beautiful, and it's home to mega contemporary art exhibitions.
And we went to see the Niki de Saint Phalle and Jean Tinguely Myths and Machines exhibition. Links in the show notes.
Saint Phalle is known for her huge, dazzling female sculptures, often outside, maybe 15, 20 feet tall, and they're covered with a mosaic of tiles or mirrors.
And they just make you smile and love life. And her partner in art crime, Tinguely, was more focused on recycling dead machine parts into new configurations.
They were big in the '80s. And these configurations are pretty scary. They move as well. It's a free exhibit. Go for free. You don't even have to book.
Just walk around, take a few hours and enjoy it. And then you can spend your coppers at their fancy farm shop or their fancy bookshop or their fancy cafe restaurant.
And you can walk around the gardens. It was great. Home to Godminster cheddar cheese as well. So you can go by there.
So highly recommended pick of the week is the Somerset Hauser Wirth Gallery showing Saint Phalle and Tinguely Myths and Machines exhibition, and it's available till the 1st of February, 2026.
I'm sure lots of our listeners would love to find out what you're up to and follow you online. What's the best way for folks to do that?
And don't forget to ensure that you never miss another episode. Follow Smashing Security in your favorite podcast app, such as Apple Podcasts, Spotify, and Pocket Casts.
It's their support that helps us give you this show for free.
For episode show notes, sponsorship info, guest list, and the entire back catalog of more than 418 episodes, check out smashingsecurity.com.
Hosts:
Graham Cluley:
Carole Theriault:
Guest:
Allan Liska – @ransomwaresommelier.com
Episode links:
- How I found a Star Wars website made by the CIA – Ciro Santilli on YouTube.
- How the CIA failed Iranian informants in its secret war with Tehran – Reuters.
- Isis and al-Qaeda sending coded messages through eBay, pornography and Reddit – Independent.
- Games Without Frontiers: Investigating Video Games as a Covert Channel – IEEE.
- General David Petraeus used clever Gmail trick during affair – Network World.
- Cambodia is home to world’s most powerful criminal network: report – SCMP.
- How to protect yourself from suspicious messages and scams– WhatsApp.
- Is WhatsApp Safe? Tips for Staying Secure – WhatsApp.
- Hacked on WhatsApp – how to stay safe when using the messaging app – BBC.
- Just a GIF Image Could Have Hacked Your Android Phone Using WhatsApp – The Hacker News.
- Kon-Tiki: The Epic Raft Journey Across the Pacific – YouTube.
- Still Standing with Jonny Harris – CBC.
- Niki de Saint Phalle & Jean Tinguely – Myths & Machines – Hauser & Wirth.
- Smashing Security merchandise (t-shirts, mugs, stickers and stuff)
- Support us on Patreon!
Sponsored by:
- Vanta – Expand the scope of your security program with market-leading compliance automation… while saving time and money. Smashing Security listeners get $1000 off!
- 1Password Extended Access Management – Secure every sign-in for every app on every device.
- MetaCompliance – MetaCompliance’s Security Awareness Planner is your free 12-month roadmap to reduce risk and build a culture of cyber awareness.
Support the show:
You can help the podcast by telling your friends and colleagues about “Smashing Security”, and leaving us a review on Apple Podcasts or Podchaser.
Become a Patreon supporter for ad-free episodes and our early-release feed!
Follow us:
Follow the show on Bluesky, or join us on the Smashing Security subreddit, or visit our website for more episodes.
Thanks:
Theme tune: “Vinyl Memories” by Mikael Manvelyan.
Assorted sound effects: AudioBlocks.