What can X Æ A-12 Musk teach us about passwords? How did our guest finally hunt down the author of one of history’s biggest virus outbreaks? And what on earth is a hacker doing breaching Roblox security?
All this and much more is discussed in the latest edition of the award-winning “Smashing Security” podcast by cybersecurity veterans Graham Cluley and Carole Theriault, joined this week by our man-in-Manila, technology journalist Geoff White.
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
If you can be arsed, please go to smashingsecurity.com/vote and vote for your favorite security podcast.
Voting closes on the 11th of May, so don't delay or I'll electrocute your eardrums. That's smashingsecurity.com/vote.
My name is Graham Cluley.
So something we need to raise, Geoff, is that as well as doing Cybercrime Investigations, that podcast of yours, you've also launched another podcast, haven't you? Earworm Island.
That's pretty much it. Similar to other desert-based radio programmes you may have heard.
And then apparently you also spoke to Rik Ferguson, who we had on Smashing Security last week.
Now, on today's show, Graham is going to give us a password update.
Geoff tracks down a notorious hacker and gets the lowdown, and I'm exploring the world of Roblox and find out how a hacker upset the apple cart.
All this and much more coming up on this episode of Smashing Security.
Yes, a child has been born just a few days ago.
Just a few days ago, he was making headlines by calling for the end of lockdown. Did you see him on Twitter?
You're going to have to share with me." Right? Because all the 6 bedrooms are full.
Which are not things for him to say, because I remember he's gone a little bit postal before on Twitter and has had an impact on his share price.
So much so that he's actually been told the lawyers have to— he has to run any controversial tweets past them.
So he can't have done this on this occasion because he went the full McAfee, right? He would never go the full McAfee.
And it's not a presidential bid, although I'm sure that will be coming. I'm sure it's only a matter of time.
Well, the answer as to why he's acting so peculiarly may be that he's having a little bit of stress at home where he lives with his girlfriend Grimes. Are you familiar with Grimes?
Was welcome to planet Earth. It was announced on Monday by Elon, and he posted a picture of his newly born with tiny face tattoos over it.
So, which I think had been added via Photoshop. I hope so.
Yeah, the eyelashes and lips are more sumptuous. It looks like the baby's wearing makeup as well as tattoos.
Now, you might be wondering what Musk Minor is going to be named. That's an obvious question. You know, how much is the baby? You know, how does it measure?
And everyone thought, "Oh, he's having a joke." And then Grimes chipped in, and she explained the name.
It's the Elven symbol of AI, which can mean love and/or artificial— The Elven? Yes. What does that mean? As in Lord of the Rings. Oh, AI.
Great in battle, but non-violent, she says.
So that's the name of the new Musk, which is going to be a challenge, I think, when they fill in the birth certificate. As to whether the form's going to accept it.
And now, are you— X for short, so that's what's gonna happen. You might be wondering, why am I bringing this up on Smashing Security?
As is every first Thursday in May, is officially World Password Day, when we're all reminded how important passwords are and about password security. Every year?
No, the first Thursday in May.
And they continued to promote the event, you know, every year for a few years, and then they got a bit bored of it.
Is that how everybody's supposed to celebrate World Password Day? Make sure you do it with a mask if you're going to do this. Yes, of course. Of course, yes.
He's got a mixture of capitals and lowercase. And I thought it's probably fairly unique, I think. I can't imagine there's many more of them out there.
And then I thought, well, maybe, you know, people keep on saying that passwords are dead, right? And that passwords are gonna be replaced by something else.
So I think if you tried to register a child as X, I don't know whether you can register that birth with that name. I don't know.
They went through over 2 billion breached passwords, and they came up with some of the most common ones, right? So lots of people are still using sports teams.
This is 2020, and people are still doing this. Apparently, the number 1 sports team or sports slogan is Roll Tide. I don't even know what that means.
Yankees, the Steelers, Eagles, and Red Sox. And then people are choosing sports like baseball, football, and soccer. Superheroes. The top superhero or cartoon character is Tigger.
You're a bit of a muso, right? The top songs and bands. The number one apparently is Blink-182.
And the other one which confused me, and I've Googled it, is 867-5309, which apparently is some pop song. I think it's meant to be a girl's number in a song.
It doesn't ring any bells with me. No idea.
And then it's 123456.
So, if you haven't already started using some sort of random character generator or a password generator to generate stronger, more unique passwords, just like he's named his child.
Hey, maybe rather than creating unique passwords for every site, maybe we should all create unique usernames instead. So you have a different username for every single site.
Oh, good point. By naming and tweeting. Yeah, well, I think—
Geoff, what have you got for us?
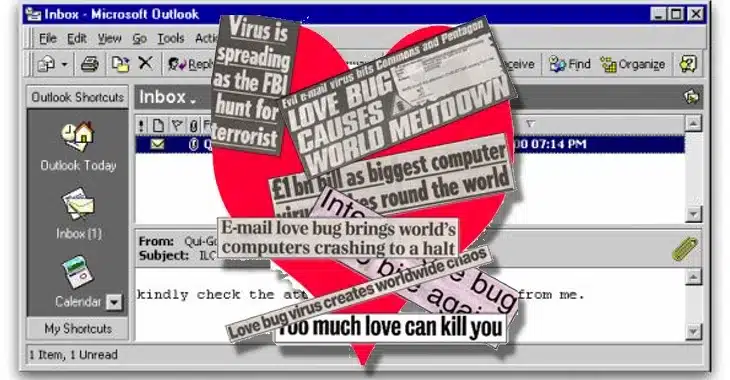
And it was 4th of May, 2000, it was launched. You guys must remember.
It was a big deal.
I was giving a talk and during a break, lots of people turned on their phones and their phones started bleeping and they came up to me and said, hey, have you heard of a virus which sends love messages?
And I said—
The funny thing was that morning I'd been telling people about funny viruses and I said, oh, there was this virus called No Smoking and what it could sometimes do is send a message, a network broadcast message saying I love you or something, or I'm in love with you.
And I was joking about the problems that could cause in the office. So I'd made this joke and then we broke for coffee and things.
Everyone's pagers started going off and they said, is that thing, is that in the wild? And I said, oh no, no, no, no, you know, you're not likely to encounter it.
And they said, well, we've just been bombarded with love messages. And it was the Lovebug that day.
Every time you looked up from your desk, there was a new person sort of staring at their computer and phoning IT support. It just went around like wildfire.
It's 45 million machines, it's estimated. Yeah, it was huge, it was huge. What was interesting was a lot of the damage it caused was it flooded email servers.
So basically you just got inundated with messages because it was a self-replicating worm.
So for every person who got hit, it would attempt to send a copy of itself to everybody in their Microsoft Outlook contacts. We call them mass mailers.
So interestingly, it was the disconnection of stuff that caused a lot of the disruption, because it wasn't that you got hit by Lovebug necessarily, but you'd had to unplug all of your email server.
So I find that interesting in that if you look at coronavirus, the period we're in now, a lot of the economic damage is being caused not by the virus itself but by the measures we're having to take to prevent the virus propagating.
So I find it's an interesting sort of echo down the line because we've disconnected rather like the Lovebug virus made us disconnect.
So anyway, so they traced— so the part is a password-stealing virus as well.
It was stealing passwords and it was sending them to an email address investigators tracked the email address to Manila.
They had a couple of suspects at the time, but there was no law at the time in the Philippines against computer hacking. Yeah, so they tracked back to an apartment.
A couple of people connected with the apartment were computer science students at a local college, notably a guy called Onel de Guzman and a friend of his called Michael Buen.
So, you know, these guys, you know, they did a press conference, people asked them and stuff, but there was no law against hacking.
And Onel de Guzman when asked about this, said, "Oh, it's possible maybe I released it by accident, don't know." And then that was it.
You know, everybody packed up and there was nothing more could be done.
There'd been nothing like it. And to be honest, there wasn't much quite like it in the years since either. It was one of the biggest outbreaks in history.
And one of the things I've talked about in the book I'm publishing in August is, you know, that prior to Lovebug, it's not quite as binary, but prior to Lovebug, it was quite difficult to, A, you know, infect lots of people and get a good base of infections, but also it's quite difficult to make money out of that stuff.
And I really feel in 2000 that changed.
Suddenly it's like, yes, you can infect millions of people, And obviously one of the effects of that is, well, then millions of people can potentially be robbed, defrauded, and so on.
So yeah, you're right. I think it really was a sea change. I mean, I've talked about, you know, the world's first global computer virus. There was obviously Melissa before in '99.
But with de Guzman, nothing seemed to happen.
And the reason I chose the Love Bug was, A, as you say, it's a massive thing. B, it was my first sort of failed attempt at journalism.
I sent a badly written article to The Guardian newspaper and they wrote back and said, we're not going to print your article.
And by the way, sending us an email titled Love Bug during the middle of an outbreak called Lovebug isn't exactly the smartest move.
Geoff, I sent out a newsletter this week to my subscribers, and I mentioned the 20th anniversary of the Lovebug, and I called the subject line of my newsletter, because I'm just childish, I said, 'Kindly read the attached newsletter coming from me,' which is a kind of spoof of the message that the Lovebug had sent.
And I did get some people coming back to me saying, "I'm not sure I trust this email." I'm not going to open this.
It's still the hacker's number one way in.
And if you think of what you need to do to trick people to open the message, the lure that you're going to need, the Lovebug was the best lure ever created because it's got universal appeal.
The one thing everybody in the world wants is love. You could not come up with a better lure for an email. It was inspired, absolutely inspired. Yeah.
So I thought, I'm going to settle this dilemma. You know, who created Lovebug? There was two people. There was Onel de Guzman and Michael Buen.
Michael Buen, as far as I can work out, still in the Philippines, still a coder. He's a very smart guy. He's very witty. And there's some stuff in the Lovebug, some little in-jokes.
And I looked at it and I looked at Michael Buen and I thought, you know, he does look like the kind of guy who, you know, might have written it.
So I started getting in touch with him, sent him many messages, and he just didn't reply. Onel de Guzman just went underground, never heard of again.
Then there was a little comment, like one comment on a forum, on an internet forum, from somebody who said 'Oh, I think I saw him in a market in Manila.
I think he was working in a mobile phone shop.' And they named where the market was. I thought, well, I'm going to the Philippines anyway to research another story.
I thought, I'll just go to the market. I'll pop by. So I looked—
And I thought, well, I'm here now, I've done some desperate things, I'm going to do a desperate thing.
So I wrote his name on a piece of paper and I literally went around the market showing it to people just in these phone shops.
And I was just— and of course, you know, I'm taller and lighter skinned than most of the people there. I just look like a tourist dad who'd lost his kids.
I was like, hello, have you seen this man?
So I went over there and I go around the mall with my little sign with his name on, and I get to the very back of the mall, like the real cheap bit of the mall, the cheap booths, and somebody says, oh yeah, he works at that booth down there.
So I went down there.
And he said, oh yeah, Onel works here, but he'll be back tomorrow, it's his day off. And I was flying out the next day at 7 PM. I said, what time do you turn up to work?
And he generally turns up about 3 or 4. I was like, oh no.
And I just thought, well, he's not going to talk, obviously he's not going to talk to me, I'm a journalist, why on earth would he do that? And B, he's going to turn up late.
He's got every opportunity to dodge this interview. But I'm here now. So I spent two days in the shopping mall. I didn't leave. I stayed there.
And sure enough, the next day he turns up. And I sat down with him, and I was expecting him to, you know, I was expecting to have to put my evidence to him and finally force him to.
But he just started, he just started talking about it and just admitted it pretty much straight off, to the point where I was so paranoid I thought, well, this must be a wind-up.
This can't be the real guy. So I was making notes in my notepad, and I just thought, well, how can I prove this is actually Onel de Guzman? And I noticed he had moles on his face.
So I started drawing in my notebook a map of where the moles were.
He also knew some other people I've been speaking to. So during the course of it, it was an hour's conversation. It became clear this was Onel de Guzman. He did create it.
He said there was a case that I think the ISP that he was using to gather the email addresses, I think they tried to bring a case against him, but that got dropped.
It would be stunning after 20 years, I think, if there was an attempt to prosecute him.
Because it was, you know, it was a decent pull-together of the virus potential at the time. He's not proud though, he deeply regrets, you know, the damage that was caused.
And he had no idea it was going to go international. He just released it at about 1 in the morning and he sent it to somebody in Singapore.
There was a Filipino person in Singapore he says he was chatting to online, so he sent the virus to him.
And then Onel de Guzman went out drinking with a mate and just forgot about it.
Michael Buen though, he has always won my award for the dumbest virus writer in history because he wrote the WM97 Michael B virus, as we called it at Sophos at the time, which at the end of the month would print out his entire CV and say if you didn't give me a job, he was going to release another virus.
And so you had his name, address, and contact details. If only, if only de Guzman had done that, you'd have been able to reach him. Yeah.
So you're quite right that the Love Bug caused this huge problem of clogging up email systems. But what's occurred to me is that virus stole your dial-up internet passwords.
So people used to connect things to FreeServe and CompuServe and things that.
It would steal those passwords and it emailed them to an address that de Guzman was in control of, presumably.
As millions and millions of people got infected, didn't that mean that his own email system would have run out of quota?
I'm poor, I can't get access to the internet. Other people do and can pay for it. So if I can just take their passwords, I can get access to the internet for free.
The problem was that where we were ordering online, they weren't going to sell us an individual box. We had to get like a crate. And so— How many's in a crate?
So we've got— Look, I don't want to talk about this. Can we please move on? Please, let's move on. Wait, is it above 100?
And for some reason in Roblox, it's a virtual environment and there are police forces.
And so they've set up Twitter accounts for Roblox police forces, but they're the same as the real police forces.
So they have to say, look, this isn't really Manchester Police, this is the Roblox virtual. That is weird.
In Roblox's case, it's like a massive online game development suite, and it tends to focus on a younger audience.
So kids, teens seem to love it, and it allows users to program games.
It's like they have their own language and they can create characters, design really complex, impressive environments from what I saw on YouTube.
And they're all programmed in this thing called Roblox Studio. And the main draw of Roblox is that it offers thousands of free user-created games for users to play.
And there's 100 million monthly active users. So no small potatoes. There is a lot of action and activity on here. So basically people can also make money on Roblox too, right?
They're called Robux and you can get Robux either by paying an online subscription or by creating objects that other people desire and then selling them on. Okay.
Much of the content seems to be developed with monetization in mind. So some developers have even become millionaires for flogging their creations. Wow.
There's this YouTuber called LinkMon99, and he's well known in the Roblox community for being the richest Roblox player for selling items for online games.
There's big catalogs and you go after certain people because they're better or they make certain cool stuff and you then spend your Robux.
Now, and they seem to do, Roblox as a company, seem to do some good community stuff, like helping with online fundraisers.
For example, they've just launched a $2 million fundraiser to support COVID-19 charities. This is UNICEF USA, Code.org, and No Kid Hungry.
And the idea is they've created some items, people buy them, and then they'll donate money from those purchases to those three charities. So it all seems good.
It's teaching people how to be creative, how to generate money, how to program. And I think it sounded quite cool.
So I couldn't help but wonder what the head honchos at Roblox were feeling on May 4th after Motherboard's Joseph Cox published this article.
Apparently a hacker tried to bribe a Roblox employee to gain access to the backend customer support panel of Roblox. You think, why would he want that?
Why would he want access to that information? So the employee could have said, how dare you, sir? But didn't. Apparently the bribe was successful.
Oh, so the way it worked is the hacker is said to have first paid an insider to perform a user data lookup, and that info helped the hacker choose his target, a customer support representative.
And the hacker provided Motherboard with a series of screenshots showing the alleged communication between them and the insider.
And the insider, this employee on LinkedIn, the worker is listed as having worked as an in-game support contractor for Roblox.
So again, LinkedIn is used as a treasure trove of information to help hackers pinpoint their targets in a company.
And that's obviously, you know, kind of an insider threat in a way, isn't it? Because you've got humans and they're bribable.
Well, let's just wait.
So I'll share a few highlights, and I want you guys to help me sniff out if he's a good hacker or a bad hacker.
The hacker could steal virtual in-game currency from people. Oh, nice. The hacker could change passwords. A hacker could effectively lock people out of their accounts.
They could turn off two-factor or multifactor authentication, ban users, and more. Wow. Okay, so he had access to the motherlode here.
And he told Motherboard, "I did this only to prove a point to them." And Motherboard has granted the hacker anonymity to speak more candidly about the crime. Okay?
So you're reading this and you're "Okay." Turns out the hacker first phished the Roblox worker to gain access to the backend customer support. So that was true.
But he backtracked when he was talking to Motherboard and said, "Actually, it was due to an issue in a piece of authentication software." And I was thinking, why would he first say it was— he phished and then say there was an issue?
So I think when he first started his story, he realized that actually that didn't mean there was any vulnerability in their system. Because he had done a social engineering attack.
And then the deal is you report those to the company to say, hey, you must fix this problem.
Once the problem is fixed, both companies can go out and tell the world about what happened. And then companies sometimes pay the researchers in response.
But this hacker's request was denied. And you remember that Linkmon99? The rich Roblox YouTuber guy? He was snagged because he's super high profile.
The hacker also stole passwords and stole items from Roblox users. And he said he did that only when he had a feeling the bounty shit was going to go south.
But surely Roblox may want to get the authorities onto this person and do some investigation.
And should an investigator knock on Motherboard's door, do you think as a journo, would the Motherboard journalist know the identity of this hacker or would he not know him at all?
Would it be safer for him not to know who the identity of this person?
So there's anonymity where you know the source and you meet them and you verify, you know, the classics of whistleblower where you chat them in a pub, but then when you publish the piece, you don't reveal their identity.
But then now, particularly in the modern tech era, there's also the possibility that somebody gets in touch with you and you have no way of verifying their identity, which is what happened in the Paradise Papers story, where the identity was never known, or that they give you an identity that's just fake or that there's no way to verify, right?
So a lot of outlets have started doing — saying, 'Well, okay, if the data is good, if the source is giving me data that I know is verifiable, and I can check, then I'll go with the story even though I can't identify the actual source of it.'
So the classic was the Sony Pictures Entertainment break-in where a lot of the fingers are now pointing at North Korea.
So a lot of the journalists who were taking information from sort of anonymous hacking groups and saying, 'Well, we don't know who's behind it, but we're publishing it anyway.' Then later on, it turns out that actually it was somebody who was basically manipulating you as a journalist to work to their agenda.
So yeah, it gets you off the hook for prosecution, for the police coming to you and asking you for the identity of the source.
But because you don't know the identity of the source, you're then at risk from a whole other angle because you could have just been basically manipulated and had your strings pulled.
Zoom is obviously experiencing massive growth right now, and they turned to Oracle Cloud Infrastructure to support them as they innovate and provide an essential service while so many folks are working remotely.
If you want to check it out for yourself, Oracle is providing some great cloud services for free for an unlimited time.
Sign up and you'll soon be building, testing, and deploying cloud applications securely with Oracle. Learn more at smashingsecurity.com/oracle.
You can manage every access point with integrated single sign-on and password management.
Let me tell you about some extra features: central admin dashboard, easy user management, group management, directory integrations, advanced reporting, multifactor authentication options, password sharing, and the list goes on.
Check it out at lastpass.com/enterprise.
Join our friends at Domain Tools for a webinar as they walk you through the process of identifying a nefarious domain, mapping connected infrastructure, and reverse engineering a ransomware attack which used a coronavirus disguise.
Learn more about how Domain Tools helps security analysts turn threat data into threat intelligence and watch the webinar at domaintools.com/smashing. On with the show.
And welcome back. And you join us on our favorite part of the show, the part of the show that we like to call Pick of the Week.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they wish.
It doesn't have to be security-related necessarily. It better not be.
No, not Animal Crossing. This is a game that we play while sat on the sofa, is a game of looking at people's bookcases when they appear on TV programmes.
So everyone's dialling in to news reports or magazine shows, and they've carefully set up the bookcase behind them to appear erudite and smart.
And, you know, we don't listen to a word that all these talking heads are saying, but we're saying, oh, look at that, that he's got in the background.
You know, why has he left that out?
When I regularly broadcast from my study before I came to the Podcast Pleasure Palace, my wife used to regularly panic about some of her books which were behind me, which she thought weren't entirely appropriate.
So there is a Twitter account called Bookcase Credibility. Twitter name is @BCredibility, and it is an account which is celebrating the backdrops behind the people appearing on TV.
Absolutely brilliant. And what they're doing is really rather creative.
They are describing the backdrops rather like they're— there used to be an art critic called Brian Sewell, who had the most wonderful voice.
So we've got one here that they've done a bookcase behind David Baddiel, who is a writer and comedian. And he goes, "No chances taken here.
David surrounds himself with bookcases in the vaguely hexagonal shape suggests they move around us, closing us in with him in a honeycomb of credibility.
The sensation is of being welcomed into the hive of a particularly well-read bee." And these writers— What accent was that? Sorry, that was Brian Sewell still. Oh, right.
That wasn't David Baddiel. And I'll do him another time. But you get these wonderful write-ups, and they're done in this pretentious artistic way. And it's a joy.
So that is my pick of the week, and it's Bookcase Credibility on Twitter. Okay, I've just subscribed. Geoff, what's your pick of the week?
That is one of the joys of life that I achingly miss. So a friend of mine recommended some software to me recently.
Now, I should say at the beginning, I have not done a full security audit of this software, so don't come back to me if you get hacked. But it's called SyncPlay.
And what it does is it syncs up. We've been using it with VLC player, which— oh yeah, great player.
So what you do is you all download the same movie file, you use SyncPlay, and effectively SyncPlay sets up a server that then connects to you all.
And so you can all start, because you know you have this thing of, "We're going to start the movie at 8," and then somebody hits the play button a bit too late, and then they end up laughing at the joke before you've all laughed at the joke.
We've just had this experience actually, Geoff, because Carole, I, and Maria Virmarsis just recorded for our Patreon supporters a commentary of the movie Zardoz.
Have you ever seen Zardoz? With Sean Connery walking around in a red nappy?
So you've downloaded this and you're all running VLC.
And then SyncPlay will allow you to play it and pause it. So anybody can play, anybody can pause it.
But the other thing I love is you can give yourself a username when you log in to SyncPlay, which obviously endless fun with movie names.
But also you can comment and your comment appears on VLC over the top of the movie. Oh!
So we watched Flash Gordon through this and I had the joy of logging on as Klytus from Flash Gordon and typing out, "Hawkman, dive!" onto the screen.
So, I haven't done this yet, but I've had a few people recommend it to me. So, it's a way of watching Netflix together.
I've put the link in the show notes, but— Yeah, so same idea, and you can have a screen so your notes appear on the screen.
Same, similar idea to yours, but might be a little bit simpler if the movie is already available on Netflix and all your friends are already having a conversation.
We could have done with that, Carole, couldn't we?
You can get fresh produce to things like crisps and other ready-made meals.
And this is a YouTube channel from a producer called Ashens who likes to, amongst other different playlists that he seems to provide, likes to do some food reviews.
So let me allow you guys to click on this link. This is his video of chicken in a can. You can turn off the sound. I found it's almost more enjoyable.
I do recommend watching it without sound almost, just so you can be absolutely revolted and you have your own commentary.
And he'd try and guess beforehand whether it was going to taste nice or not. So he would open these things up and then would try them out. And he had quite a lot of subscribers.
Yeah, this guy eats everything he opens.
So this is the channel, it's called Ashton's, it's on YouTube, and amongst his various playlists he does a number of revolting food reviews, which will put your potentially not wonderful dinner— if you don't have great cooking skills at home and you're stuck there and you can't wait to go to restaurants again, this will make you feel better about the food that you may be producing.
Geoff, I'm sure lots of our listeners would love to follow you online or check out one of your podcasts. What's the best way for folks to do that?
And on Reddit in the Smashing Security subreddit, go and find us there.
Also, a huge thank you to this week's Smashing Security sponsors: Oracle, Domain Tools, and LastPass. Their support helps us give you this show for free.
Check out smashingsecurity.com for past episodes, sponsorship details, and information on how to get in touch with us.
It's not even dark out. Well, it will be in a minute. After dusk. Well, during dusk. Smashing Security during dusk.
Today we are going to be doing a commentary on a movie which Maria brought up on a recent episode of Smashing Security. And that movie is Zardoz.
I thought it might be useful if each of us described our relationship with Zardoz before we began. How are we coming to this movie?
Maria, as you're the person who first mentioned it, you start us off.
They had a 24-hour bad sci-fi movie marathon called Schlock Around the Clock, and Zardoz was sort of like the prime feature. And a bunch of my friends and I went to see it.
Some of them had seen it, some of them hadn't. And I— you can't forget your first time.
And every year when they would do this festival, I would always make a point to bring someone with me who hadn't seen it before.
And at that point, I would just watch their face and not the movie. It's just a— in my group of friends, we all love how bad this movie is. And yeah, I love it in a bad way.
I've never seen it, Maria, and I wish you could see my face. I wish we had a video cam on so you could watch it. Me too.
I'll take selfies as appropriate when you say take a selfie now. Okay, you can line me up and I will do that for you and send them to you.
Basically the whole first half of the movie, just record your face because— The beginning is especially— The beginning is extraordinary. Yeah, it loses steam.
Just a fair warning. It just kind of— Yeah. Well, you know, we can always hurry through. If it gets boring, we just call it off, right? Yeah. Well, that—
I will make it very formal. I'll say, "Question!" or something like that, I'm raising my hand.
So Mr. Maria is not a fan? He's never— no, he would love to see it. He was actually asking to watch this with me while we're doing this, but someone has to watch our kids.
All right, for the most part. Okay, okay. Can we just kick this off? Yeah.
What year is this? 1974? Something like that. There's only one Zardoz.
They hoped this would clarify things. I know. So he slowly goes down. I'm so into this already. Okay, I'm, I'm sitting back.
He was also in Mamma Mia. Oh well, I didn't realize they filmed this in Ireland. Are those real horses or CGI? Fake horses. Oh, I love the logo. I love the logo.
No, I love it, I love it. Oh, here it is. You're gonna be so disappointed when you learn what Zardoz means. Oh yes, yeah. Okay, spoiler, I'm gonna— I'm painting this tomorrow.
This is inspiring me. Oh yep, okay. I'm gonna— I'm seriously, I'm gonna do it. So more than one Sean Connery in this movie. That's important.
Yeah, do you? Yes, do you, Carole? I'm having a Zardoz party when this is all over, Graham.
This is the edited version.
Just visit patreon.com/smashingsecurity for more details. Until next time, cheerio, bye-bye.
Hosts:
Graham Cluley:
Carole Theriault:
Guest:
Geoff White – @geoffwhite247
Show notes:
- Vote for Smashing Security in the EU Security Blogger Awards!
- Graham Cluley on Earworm Island — Earworm Island podcast.
- Carole Theriault on Earworm Island — Earworm Island podcast.
- Elon Musk tweets a photo of his newborn child — Twitter.
- World Password Day — Days of the year.
- Grimes explains the baby's name — Twitter.
- Don’t Make These 5 Password FAILS! (But Do Notch These 2 Password Wins) — ID Agent.
- Love Bug Virus Creator Comes Clean — Geoff White.
- Memories of the Melissa virus — Naked Security.
- Roblox — Wikipedia.
- What is Roblox? — Digital Trends.
- Hacker Bribed 'Roblox' Insider to Access User Data — Motherboard.
- I'm Officially RICHER Than ROBLOX!! (WORLD RECORD BROKEN) — Linkmon99 on YouTube.
- WM97/Michael-B virus analysis — Sophos.
- Bookcase Credibility — @BCredibility on Twitter.
- Five Minutes With: Brian Sewell — YouTube. So you can see how good Graham’s impression is.
- Syncplay.
- Netflix Party.
- Whole Chicken in a Can — Ashens on YouTube.
- Poundland Food Special – All Day Breakfast — Ashens on YouTube.
- MRE & Ration Reviews — YouTube. A man experiencing and reviewing military rations from 1863-current day.
- Smashing Security merchandise (t-shirts, mugs, stickers and stuff)
- Support us on Patreon!
Build, test, and deploy applications on Oracle Cloud – for free.
Sign up now at smashingsecurity.com/oracle and you’ll soon be building, testing and deploying cloud applications securely with Oracle.
LastPass Enterprise makes password security effortless for your organization.
LastPass Enterprise simplifies password management for companies of every size, with the right tools to secure your business with centralized control of employee passwords and apps.
But, LastPass isn’t just for enterprises, it’s an equally great solution for business teams, families and single users.
Go to lastpass.com/smashing to see why LastPass is the trusted enterprise password manager of over 33 thousand businesses.
Join our friends at DomainTools for a webinar as they walk you through the process of identifying a nefarious domain, mapping connected infrastructure, and reverse-engineering a ransomware attack which used a Coronavirus disguise.
Learn more about how DomainTools helps security analysts turn threat data into threat intelligence and watch the webinar at domaintools.com/smashing now.
Follow the show:
Follow the show on Bluesky at @smashingsecurity.com, on the Smashing Security subreddit, or visit our website for more episodes.
Remember: Subscribe on Apple Podcasts, Spotify, or your favourite podcast app, to catch all of the episodes as they go live. Thanks for listening!
Warning: This podcast may contain nuts, adult themes, and rude language.