It’s been over seven years since the Conficker worm spread around the world, cracking passwords, exploiting vulnerabilities, and hijacking Windows computers into a botnet to distribute spam and install scareware.
It became one of the most serious malware outbreaks of all time.
Microsoft even offered a $250,000 reward for anyone offering information that would lead to Conficker’s creator. As far as I’m aware, that bounty has never been paid and the malware authors remain at large.
So, you may be wondering, what of Conficker today?
Well, according to the latest statistics provided by Check Point, Conficker remains the top malware attacking its UK corporate customers – accounting for some 1 in 5 of all detections.
As The Register reports, Conficker may not be causing as many problems as it did seven years ago – but plenty of computers remain infected, allowing the worm to continue to try to find other Windows systems to infect.
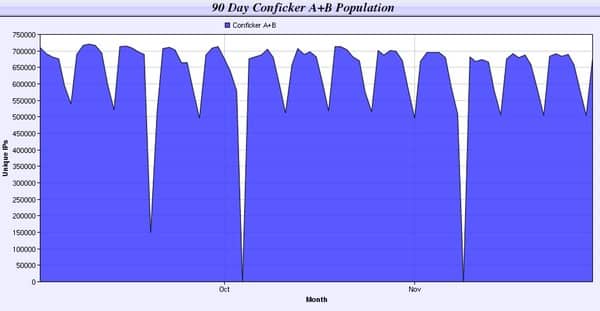
The Conficker Working Group, which tracks the number of unique IP addresses on the internet that are infected with Conficker, estimates that over 600,000 unique IP addresses remain infected by the malware.
As long as there are Conficker-infected computers connected to each other, the malware will continue to hunt for new victims.
Perhaps we shouldn’t be surprised to see Conficker and other old timers like Sality and Cutwail continue to be responsible for so many attempted malware attacks.
Most of the malware we see today doesn’t spread via its own steam like the Conficker worm. Instead malicious hackers write Trojan horses that are designed to not draw attention to themselves, and are sometimes sent only to a small list of targets to improve their chances of infecting systems undetected and give attackers access to your files and communications.

Every good anti-virus program (in fact, most of the really crummy ones as well) can detect Conficker. The problem is that the computers infected with Conficker attempting to infect other Windows PCs aren’t running anti-virus software.
Ironically, Conficker should never have been capable of spreading in the first place – as Microsoft issued a patch for the vulnerability that Conficker relied upon a full 29 days before Conficker began to spread.
Be a responsible part of the internet community. Make sure that all of the computers under your control are strongly defended against malware attacks with security software and patches. Don’t allow one computer in the corner of the room to be the one that continues to spread malware that has no right to carry on living.
flickr photo shared by Jitter Buffer under a Creative Commons ( BY-NC-ND ) license

No surprise I'm afraid to say, I keep still finding companies that are infected and get re-infected by Conficker all the time.
Why? Mainly because the forget to scan SMB/CIFS shares on Linux/AIX and other OSes that Conficker sees as "Windows Shares" and promptly drops a copy, or copies of itself there….ready to start the next round of infection when a Windows PC calls in and executes one of the infected files.
This doesn't mean that the Linux/AIX or other OS hosting SMB/CIFS is infected, no, just that it acts as a digital foxhole for the malware to hide in.
Then there are still loads of companies running un-patched Windows systems, ones that still have autorun enabled for USB as well as weak passwords (in the list of passwords that Conficker has inside itself) as well as no account lock out policies to stop dictionary password attacks. Maybe one day they will learn?
Hmmmm, hang on, don't think that will happen any time soon as the same companies are the ones getting hit by the rebirth of Macro malware (it's like it is 1995 all over again!).