
The digital miscreants who developed the SamSam ransomware raked in approximately US $450,000 over the span of one year.
SamSam, otherwise known as ‘Samas,’ ‘samsa,’ and ‘MOKOPONI,’ first reared its ugly head back in December 2015.
In the year that followed, criminals primarily leveraged the ransomware as a post-secondary attack tool after compromising the networks of organizations like hosted desktop and cloud provider VESK.
But SamSam’s authors weren’t the only ones who were busy.
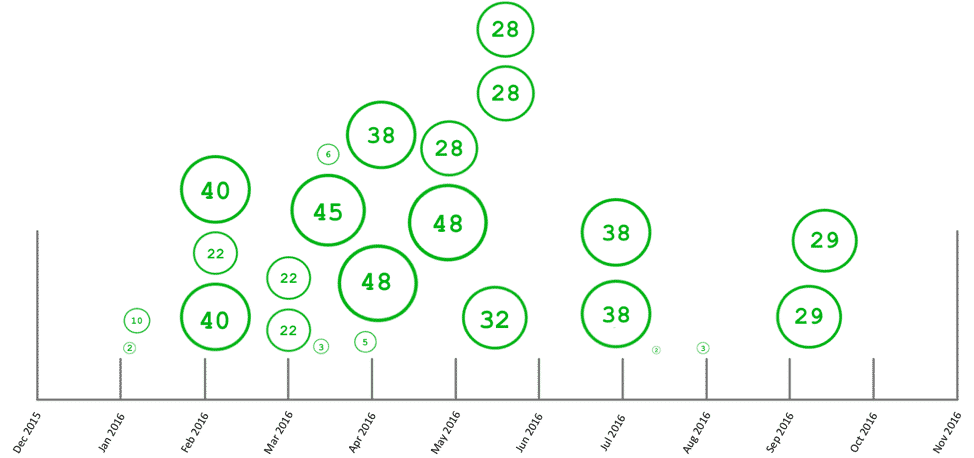
Palo Alto Networks’ Unit 42 research team spent the past 12 months gathering 60 samples of the ransomware, a total which is less than those of other crypto-malware families like Cerber and Locky.
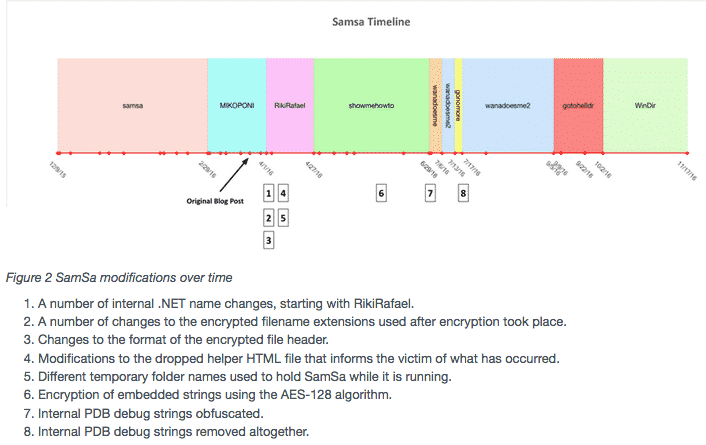
In that span of time, they saw 24 samples of SamSam adopt a number of disguises and modifications in how it functions.
All of SamSam’s active samples were tied to 19 unique Bitcoin addresses, a fact which allowed Unit 42 to continually monitor the blockchain for transfers into those wallets.
In the process, Palo Alto Networks’ researchers learned just how lucrative the ransomware’s first year proved to be. As they explain in a blog post:
“Of those 19 unique BTC addresses we observed since March 24th, 14 of these have received payments totaling roughly 394 BTC. Prior to March 24, 2016, we observed roughly 213 BTC received, giving us a total of 607 BTC received by the SamSa actors. Using today’s current BTC rate of $744.43, this allows us to estimate that the attackers have obtained roughly $450,000 since their operations began. It’s important to also note that there are likely a number of samples that exist, which we were unable to obtain, causing the actual figure to likely be much higher.”
It’s no wonder Unit 42 doesn’t think the actors behind SamSam will retire their ransomware anytime soon. With that in mind, users need to remember to prepare for the worst. They can do so by regularly backing up their critical data, patching their systems on a regular basis, and installing anti-virus software.
SamSam seems to mostly appear after a successful hack. Organizations need to therefore shore up their defenses against some of the most common attack vectors like phishing scams by training their employees to not click on suspicious links/email attachments and by deploying email filtering tools. They also need to make sure their data backup strategy is functional.
For additional protection, companies might want to consider investing in file integrity monitoring software that’s capable of detecting suspicious changes on their networks.


