 CNN has published a report claiming that hackers, backed by the Russian government, hacked into parts of the White House computer system.
CNN has published a report claiming that hackers, backed by the Russian government, hacked into parts of the White House computer system.
According to the news outlet, the hackers were able to use an already-reported hack of the US State Department as a springboard for a subsequent attack against the White House.
As a consequence, the hackers are said to have been able to access “sensitive information such as real-time non-public details of the president’s schedule” and planned policy announcements on a network the White House considers unclassified.
A classified computer system which is supposed to be used for all sensitive White House communications is run separately, and is said by officials not to have been breached.
Although the White House may currently be nervous of directly accusing the Russians of involvement in the hack, CNN seems to have no such qualms:
The FBI, Secret Service and U.S. intelligence agencies are all involved in investigating the breach, which they consider among the most sophisticated attacks ever launched against U.S. government systems. The intrusion was routed through computers around the world, as hackers often do to hide their tracks, but investigators found tell-tale codes and other markers that they believe point to hackers working for the Russian government. A spokesman for the National Security Council declined to comment. Neither the U.S. State Department or the Russian immediately embassy responded to a request for comment.
In all likelihood, the White House hack is being connected to a cybercrime operation known as “Pawn Storm” that saw government, media and military agencies in the United States, Pakistan, and Europe targeted with spearphishing, watering hole attacks and malware-laced Word documents.
Earlier this year, Operation Pawn Storm was even revealed to be targeting users of non-jailbroken iPhones and iPads.
But my guess is that the most likely avenue for the hackers would have been a plain-and-simple phishing operation, tricking users into handing their passwords over to the hackers, or visiting a webpage which contains a drive-by malware attack designed to pilfer login credentials.
Yes, it’s basic social engineering – but it works an astonishing amount of the time.
Aside from Western agencies, Operation Pawn Storm also targeted politicians and dissidents who oppose the Russian government.
You don’t, therefore, need to be a rocket scientist to work out who might be high on the list of suspects.
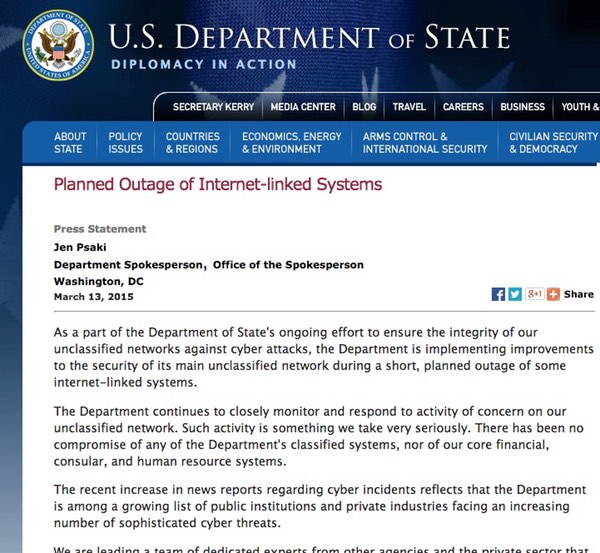
In what was clearly a step linked to the current crop of hacks, the State Department last month temporarily disconnected its main unclassified network from the internet for what it described as a “planned outage” to make improvements to its security.
The news of the White House hack has come within days of President Obama ordering new sanctions against overseas hackers.
 One cannot help but wonder if that was a pre-emptive strike by Obama, knowing that Russian hackers might be inside the White House. After all, Obama has hardly endeared himself with the Kremlin recently after slapping sanctions on Russian separatists fighting in Ukraine.
One cannot help but wonder if that was a pre-emptive strike by Obama, knowing that Russian hackers might be inside the White House. After all, Obama has hardly endeared himself with the Kremlin recently after slapping sanctions on Russian separatists fighting in Ukraine.
Of course, even if fingers of suspicion are pointing towards Russia, that’s very different from having convincing proof that Moscow is behind the hack.
Attribution of internet attacks is notoriously difficult and much harder than the average man in the street (and possibly politician) imagines, which is certainly a frustration for news reporters who wish to tie up a story with a simple bow for the benefit of the audiences at home.
Many were rightly skeptical that the hack of Sony Pictures could be so easily placed at North Korea’s door, and similarly we shouldn’t jump too easily behind headlines claiming that the Russian government is behind this latest hack of the White House either.
And let’s not forget, the likes of the NSA and GCHQ aren’t above spying on other governments, and hacking overseas companies, via the internet either.



"backed by the Russian government"
Prove it.
"but investigators found tell-tale codes and other markers that they believe point to hackers working for the Russian government."
That's your (did you even see it?) evidence, is it, that the Kremlin is involved? Or was it is just filler since you have nothing other than accusations with no real authority in these types of things (which is expected, understandable and perhaps acceptable; after all, reporting news is very different from this, and things that appear similar aren't always as similar as they appear, this even includes outside of technology)? Whatever you call it, I suppose with said logic you can also claim that all old viruses that were in the same family were written by the same person, yes? The problem is it is just like everything else – so much in this world can be very similar in appearance/trait to something else, yet they aren't necessarily as related as they seem (if at all). For instance, all media outlets love sensationalism but that doesn't mean they're of the same parent organisation (perhaps called CNN?), does it?
Maybe you do, but of course even if it is state sponsored, and even if said state is Russia, you could change their name to other countries and it would be similar (perhaps different targets). The victim of this attack, perhaps?