
Online privacy is a subject of many layers. For all that we’ve discussed protecting your privacy on social networks like Facebook, there are other facets to consider.
Operating systems, for instance. Needless to say, Windows 10, OS X El Capitan and Ubuntu are highly distinctive OSes, both in style and substance.
Some questions have been raised about features in Microsoft, Apple and Canonical’s latest operating system offerings. Making things more “relevant” to your needs and sending data for “suggestions” are common themes in the verbose Terms of Service.
Couple these chummy ambiguities with a perplexing array of opt-in settings and you’ve got a surefire recipe for confusion. Do not be alarmed, I’m going to get right to the point.
Today, I’d just like to share a few hard facts about how to get your OS privacy settings in check. We’ll take a look at what we know, what’s being sent where and how to turn things off – starting with Windows 10.
Windows 10
During installation
You first encounter Windows 10’s privacy options during the installation process. We’ll start by identifying and exploring each of the settings, in order.
Immediately after installing Windows 10, Microsoft prompt you to “get going fast” and skip all customisation options. Choosing to use “Express Settings” is not recommended, so select the bottom-left “Customise Settings” option instead.

Of the first page of settings, I would recommend switching all of them off:
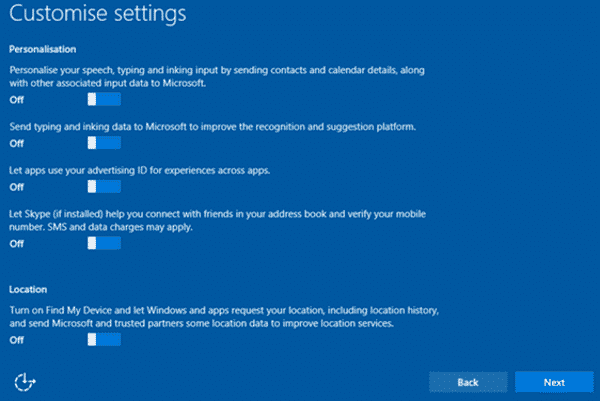
- “Personalise your […] input” will allow Windows to improve its autocorrect suggestions and personalised language data for you, at the cost of providing “input data.”
- “Send typing and inking data” lies in the same vein: more accurate predictions of typed and handwritten text through transmitted data.
- Your “advertising ID” allows advertisers to deliver targeted advertisements within Windows UI apps.
- It’s unusual that Microsoft mention allowing Skype to “connect you with friends” via your mobile number during this process. Leave this setting switched off.
- The “Location” option encompasses several sub-settings, which can be configured separately later.
The second page of settings relates to “connectivity and error reporting”. I would also recommend disabling all of these:

- Connecting to “suggested” Wi-Fi hotspots is a big no, especially due to the fact that “not all networks are secure.”
- On the principle, using your “contacts” for network sharing (through the Wi-Fi Sense feature) is another definite turn-off.
- Automatically connecting to hotspots “temporarily” can also be considered a risk (due to Evil Twin style attacks) – it’s your choice to initiate a connection.
- Finally, sending “full error and diagnostic” info to Microsoft is a classic turn-off setting, again on the principle of privacy.
The final set of settings concerns the browser, and should be considered individually:

- I would recommend leaving “SmartScreen” services enabled, as Windows browsers and apps will be protected from malicious downloads. It’s a matter of choice.
- The fact that “your browsing data will be sent to Microsoft” for “experience” purposes makes the next setting a clear turn-off.
- Obtaining updates from “other PCs on the Internet” (in Peer-to-Peer style) is another turn-off; I recommend sticking to the classic update process.
After being swamped with all these settings, the familiar waiting screen appears. After a couple of minutes, you are taken to the Desktop.
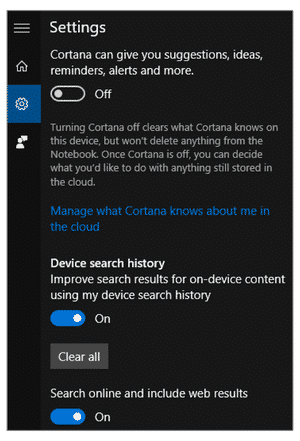
You’ll notice the icon for Cortana (Microsoft’s digital assistant) in the bottommost search bar. Click or tap the bar, and choose “Not Interested” to turn down the PA for good. Sorry, Cortana.

Most (but not all) of the offending privacy settings will have now been disabled. In the same interface, click or tap on the small cog icon to reveal two more search-related features.
While “device search history” refers to non-transmitted data (stored locally), the “search online” feature offers suggestions which should be disabled.
The rest of the settings are covered in post-installation, and can be accessed by clicking the “Other Privacy Settings” link.
Post-installation
If you’ve already got Windows 10 installed, don’t worry. Let’s take a look at each of the options as found in your PC Settings.
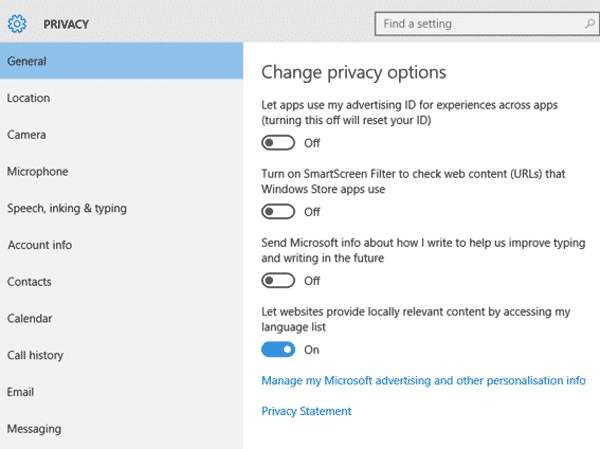
The “General” section covers all of the aforementioned settings, with the addition of “locally relevant content” from your language list. It’s a very minor option which informs websites that you’re browsing from an “English (UK)” system.
All but one of the following sections are self-explanatory, and can be toggled as per your preference. Microsoft provide granular control of permission settings.
The “Feedback and Diagnostics” section deals with the classically obscure “usage data” – which can be set to the lowest (“Basic”) level per your request.
My final point concerns the Microsoft Account at large. Non-enterprise customers are funnelled into creating a Microsoft Account when you install Windows 10, which is another concern in itself.
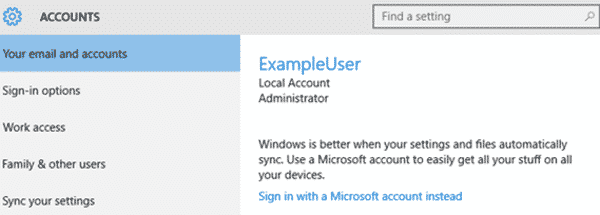
From the Privacy section of PC Settings, select the upper-left blue cog and visit the “Accounts” area. You can switch between a Local (recommended) or Microsoft-based account here.
Beyond the Operating System
By the way: it’s not just a case of securing the operating system, but also securing the apps that run on it.
You may wish to reduce your surface of attack by removing apps that you may not really require, but which have a history of being targeted. For more information, check out my guides for updating (and completely uninstalling) Adobe Flash, Oracle’s Java and Microsoft’s very own Silverlight.
As we explored in a previous article, plugin exploits are packaged into multi-pronged “Exploit Kits” designed specifically to take advantage of newfound vulnerabilities.
What’s more concerning is that data leakage isn’t limited to the OS and its plugins. The very applications which you use to carry out day-to-day tasks may have compromised your privacy.
Companies the world over have been picked up for their laissez-faire approach to securing your PII (Personally Identifiable Information). If you become suspicious of an app’s data collection practices, don’t hesitate to ask for advice and avoid using the software for a while.


You need to do a Part 2 to set up some router firewall rules to permanently block the several NSA^H^H^H Microsoft telemetry IP addresses.
Yasin, your guide only stops a very small proportion of telemetry and tracking data from being sent to Microsoft.
For your reference, and for others who want to protect their privacy, I suggest reading the official documentation:
https://technet.microsoft.com/en-us/itpro/windows/manage/configure-windows-10-devices-to-stop-data-flow-to-microsoft
To achieve a reasonable standard of privacy in Windows 10 is VERY difficult; look at how long that guide is! (Not all versions of Windows 10 allow you to completely disable everything anyway).
My suggestion to most people, particularly those who are non-technical, is to download ShutUp10 – it "is entirely free and does not have to be installed". It also automates the complex process and removes the potential for making mistakes.
https://www.oo-software.com/en/shutup10
Did they fix the data gathering so that all privacy settings are honored? I remember that early on some settings were ignored. It's why I haven't upgraded yet.
Guess that answers my question