
The CEO of a child tracking company has accused a security researcher of hacking the firm after the researcher reported on a database error that exposed thousands of customers’ children’s personal information.
uKnowKids offers software that “Makes Parenting Easier, and Keeps Kids Safe” by allowing parents to monitor what their children are up to on social networks and mobile phones.
Parents who sign up with the company are required to create a profile for their children. As a bare minimum, those profiles include their child’s name and date of birth. However, customers are also encouraged to enter in school names and mobile phone numbers, among other information.
 All of this data somehow plays into the company’s main mission of monitoring children’s engagement, connections, etc. on social media. Specifically, the firm’s website reveals that it tracks kids’ Facebook, Instagram, Twitter, and a number of other online accounts on both Android and iOS devices.
All of this data somehow plays into the company’s main mission of monitoring children’s engagement, connections, etc. on social media. Specifically, the firm’s website reveals that it tracks kids’ Facebook, Instagram, Twitter, and a number of other online accounts on both Android and iOS devices.
This is a lot of information for a company to monitor, which has led the firm to adopt the use of 128-bit SSL connections to transmit data, among other precautions.
Unfortunately, a simple error has rendered much of those protections meaningless for hundreds of customers.
On Monday, news first broke about how Chris Vickery, a security researcher who now blogs for MacKeeper, came across a misconfigured MongoDB installation.
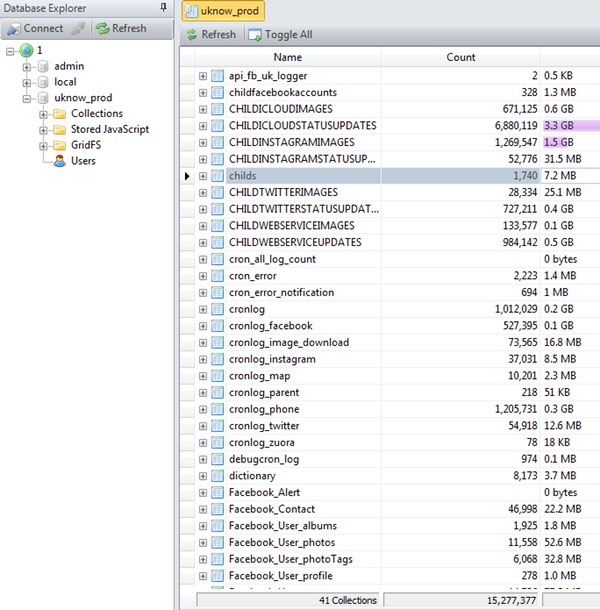
The misconfiguration, which turned out to be uKnowKids’ failure to set up any login credentials on a database, ultimately exposed 6.8 million text messages, 1.8 million images (some of which include children), and 1700 children’s profiles.
Vickery contacted DataBreaches.net about the security failure, telling them that exposed data included “full names, email addresses, GPS coordinates, dates of birth, and much more”, although “he did not see payment info or parent details exposed.”
A screenshot provided by Vickery indicated that data related to 1,740 children was accessible.
Later that same day, uKnowKids CEO Steven Woda posted a statement on the company’s website entitled “Breaking news… A uKnow database was breached by a hacker, and here are the facts as we know them right now”.
In that advisory, Woda says that his firm patched the vulnerability shortly after Vickery notified the company, conducted an investigation of all uKnow systems, reconfigured all encryption keys, hired security experts to review its systems, updated its security policies, and contacted the FTC and law enforcement authorities.
Woda goes on to refer to Vickery’s claims as a “white-hat” hacker but states that it is fully investigating his background to confirm the researcher’s “benign” intentions.
This skepticism arose when Vickery allegedly refused to delete the database he had downloaded from uKnowKids.
We have repeatedly requested that Mr. Vickery permanently delete any and all copies of uKnow’s intellectual property including its proprietary customer data, business data, database schemas and field names, trade secrets, curated data dictionaries and algorithms.
After initial resistance, Mr. Vickery claims to have deleted the downloaded database in its entirety. However, he has reportedly retained an unknown number of screenshot copies of uKnow’s intellectual property, and is so far unwilling to permanently delete this information. In an effort to protect our customers and stakeholders, we continue to request the destruction of any and all copies of uKnow’s database including screenshots which are, in fact, copies of uKnow’s database.
This type of refusal would be enough to make anyone wonder if the researcher were in it for his own personal gain.
However, such behavior is inconsistent with Vickery’s past work, not to mention his own explanation for what happened following this incident, as he told CSO Online:
“After considering the potential worry to parents, I securely wiped it within 48 hours and notified uKnowKids of this fact. However, the few retained screenshots are completely redacted of all Personally Identifiable Information and are being kept for purposes of credibility and to keep uKnowKids (minimally) honest in their claims.”
Vickery goes on to note that uKnowKids is likely just the first of many child tracking companies that will go through an exposure such as this. He’s likely right.
With that threat in mind, parents should weigh buying into these services very carefully. There could be other ways for you to teach your children about safe web practices, such as by being open with your kids and limiting their web access near bedtime.
If you do decide to go with these types of services, it might be wise to provide them with as little information about your child as possible. Your kids are young and innocent; they shouldn’t have to worry about the effects of identity theft so early in their lives.



I highly respect and admire Vickery's research and I am also a huge fan of Shodan/Matherly as well. Another MongoDB misconfiguration and one more company that will not take responsibility. . .
Security researchers are integral to bring awareness to the security community and to the victims who suffer at the hands of bad security practices.
Vickery has my support and I say "keep em coming" – security researchers are one of our best assets to keep the Internet safe and to expose what needs to be fixed.
One might reasonably wonder why Vickery (and databreaches.net) felt it necessary to copy and publish any information about the vulnerable company, and why they should not be called out for it. It should have been enough to notify uKnowKids that they had left the database unsecured and accessible from the public internet, and apparently it was. From the Databreaches.net report, uKnowKids corrected the vulnerability in about 90 minutes. A short report that the vulnerability had existed, and had been corrected ought to have been enough.
100% agree.
There is a line that you cannot cross that goes from ethical to something else.
Many, many, many companies get breached. The folks in question here seemed to have jumped on it super fast and publicly reporting a ton of details… More than my corporate counsel would ever let me disclose.
I think uKnowKids deserves kudos for addressing this quickly and transparently.