 You would think, considering how many security problems have beset the teen sexting app Snapchat, that it would be hard to produce a competing app which was more careless with users’ data.
You would think, considering how many security problems have beset the teen sexting app Snapchat, that it would be hard to produce a competing app which was more careless with users’ data.
But, if reports are accurate, it seems Puffchat has managed precisely that.
Puffchat is a fairly new iPhone and Android app which claims to provide a way of sending texts and photos to your friends that will automatically expire, removing all evidence that they ever existed.
Unfortunately, according to security researcher Thomas Hedderwick, the service is beset with privacy issues and security vulnerabilities.
Hedderwick detailed issues with the app in a blog post.
For instance:
- Information (including the user’s address book) is sent to Puffchat’s servers in unecrypted form – using HTTP rather than HTTPS. This opens the door for hackers to intercept communications.
- The secret key used by the app isn’t actually secret at all, as no attempt is made to disguise it during transmission
- Searching for fellow users of Puffchat reveals not just their registered username, but also their birthday and registered email address.
- API operations can be performed without access to the account, or local access to the smartphone. For instance, Hedderwick was able to trick Puffchat into sending himself a friend request from the Puffchat founder’s account.
- And, fatally, images aren’t actually deleted when Puffchat claims. Images remain on Puffchat’s servers, and it’s just the Puffchat smartphone app that declines to show the image. If you know the URL for the image (helpfully revealed by the unsecured transmission between the app and its servers), you can still view it.
You can clearly see the server knows the message has been read and yet it remains; it’s downloaded to your phone every time you make a request for your messages, the client just doesn’t show it to you… and yes, that includes the nude dickpics you’ve been sending to that account.
To top is all off, you can visit the pictures publicly and see via their site – nice! This is an incredible breach of privacy, and a blatant lie to their customers. It’s ‘secure’ but no SSL, it’s ‘secure’ but I can control your account remotely, it’s ‘secure’ but I can see your junk on the web by visiting a public page.
Hedderwick says he attempted to responsibly inform Puffchat of the serious issues, but received no response:
In the interest of responsible disclosure I did try and contact the dev multiple ways, I was either ignored or not replied to and I feel users deserve to know what’s happening with their data.
Well, after publishing his public blog post, he’s got his desired response from the company now.
Unfortunately, Puffchat founder Mike Suppo’s response was to demand that the security researcher take his blog post down.
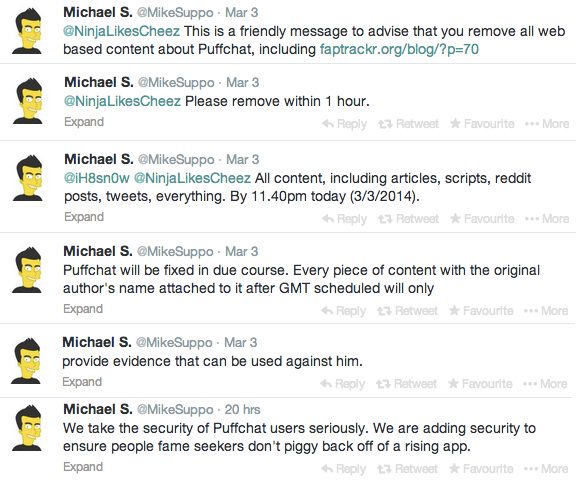
This, apparently, was a “friendly message”.
Suppo has since posted on Puffchat’s official blog (I say it’s their official blog, but it’s hosted on Blogspot.co.uk. Make of that what you will…) that “the information was not emailed to any of our Puffchat administration accounts and was therefore not responsibly disclosed over the internet.”
At the time of writing, Hedderwick’s blog post is showing no sign of being withdrawn.



Lol, his twitter account got hacked recently.
Why is this even news? Just another useless snapchat clone made by a moron who thinks he know his shit and an app no one has even heard of. Don't know why this researcher would bother researching such a small app. Kinda pointless.
I think I've figured out why Puffchat has such wonderful security. In his New Year's Day post (http://www.puffchat.blogspot.co.uk/2014/01/happy-new-year.html), Michael S. suggested some New Year's resolutions to his readers:
… Discover a new skill at college, learn a language or musical instrument… or learn to code and work for us! :)
Perhaps this is what you get if you hire coders who only have two month's experience.