
If you’re unfortunate enough to find your Windows computer has been infected by the ProLock ransomware, you’ll find the recovery instructions from the criminals who compromised your PC tell you to do the normal things if you want to regain access to your encrypted files:
- Download and install the Tor browser
- Visit the ProLock website using Tor, and enter your unique ID
- Read how much it’s going to cost you for a decryption key, and pay the required ransom in cryptocurrency into a wallet under the criminals’ control.
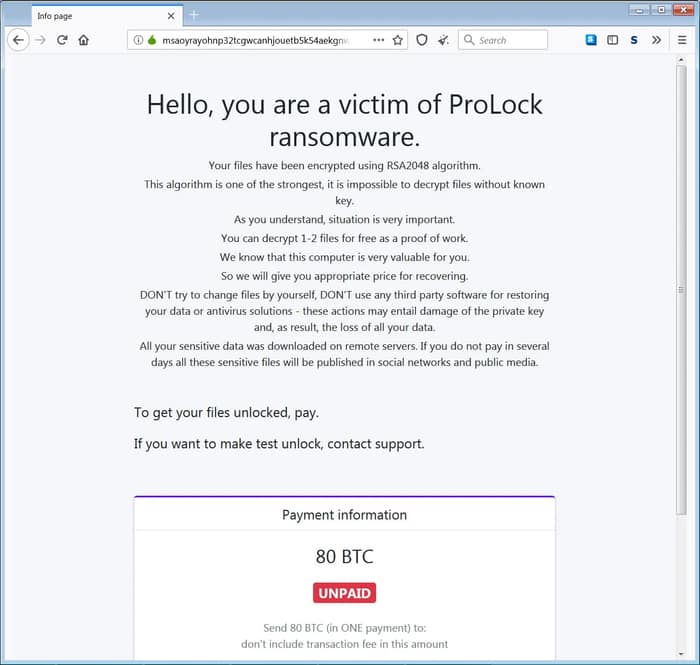
In some cases you may find yourself on the wrong end of a bill totalling hundreds of thousands of dollars to get your files back after they have been ravaged by the ransomware, which is thought to gain access to networks via the Qakbot Trojan horse.
What the hackers don’t tell you – let’s be generous, perhaps because they’re not aware themselves – is that there’s a bug within ProLock’s decryption code.
And, according to a “Flash” alert distributed by the FBI to companies earlier this month, ProLock’s decryptor can actually corrupt files as it tries to decrypt them:
The decryption key or “decryptor” provided by the attackers upon paying the ransom has not routinely executed correctly. The decryptor can potentially corrupt files that are larger than 64MB and may result in file integrity loss of approximately 1 byte per 1KB over 100MB. Added coding may be necessary for the decryptor to function.
Well, that’s upsetting. You’ve spent all your money to get your files back and then the decryption process provided by the hackers doesn’t work properly. I wonder if that might reduce the chances of them successfully winning your custom in future?
It’s not as though there’s a customer service desk you can complain to at the hackers’ HQ…. well, actually there is. There’s an email address hosted by ProtonMail, although lord knows how successful you’ll be at getting the problem fixed to your resolution without ending up out of pocket.
In the past the FBI has advised companies to not give in to ransomware demands, saying – amongst other arguments – that there’s no guarantee victims will get their data back.
With this revelation about the bug in ProLock’s decryption code, it does indeed appear that there’s no guarantee at all.
Of course, if you’re really desperate, and don’t have access to a secure backup of your data (always the best way to remedy a ransomware attack), you might still choose to pay your attackers in an attempt to recover at least some of the data that they encrypted.
That’s not a pleasant situation to find yourself in, but if it’s the only way to protect your customers, employees, and shareholders I’m certainly not the one who is going to criticise you for it.
But maybe you’ll gain some small satisfaction from knowing that whoever is behind the ProLock ransomware does seem to be having a lot of headaches when it comes to decryption.
ProLock was born out the ashes of the PwndLocker ransomware at the end of March, after its creators decided their ransomware needed a new name as part of a rebrand after security researchers found a flaw that made free decryption possible.
Maybe with this latest news it will be time for ProLock to get yet another name change and rebrand?


