 Do you think hacking financial institutions and selling stolen information onto others is a viable career? You could be flushing your life down the toilet…
Do you think hacking financial institutions and selling stolen information onto others is a viable career? You could be flushing your life down the toilet…
A Malaysian man who was arrested last year by an undercover Secret Service agent, has admitted hacking into a series of financial institutions, and pleaded guilty to possessing stolen credit and debit card numbers with the intention to defraud.
Officers arrested 32-year-old Lin Mun Poo in a diner, shortly after he flew into New York from Malaysia, and claimed to recover over 400,000 credit card numbers and bank account details from his “heavily encrypted laptop computer”.
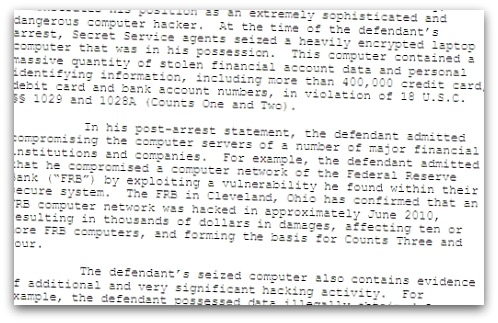
Lin Mun Poo found a security vulnerability on Federal Reserve Bank of Cleveland’s network in June 2010, and claims to have added malicious code to a Federal Reserve computer. However, it is believed that he stole the treasure trove of credit card numbers and other account information from other financial institutions.
No Federal Reserve data or information was accessed or compromised, according to a spokeswoman for the bank.
It seems that Lin Mun Poo didn’t limit himself to merely breaking into financial systems, as court documents have alleged that he also hacked into the network of a major Department of Defense contractor.
Lin Mun Poo is being held in a Brooklyn jail, and faces up to 10 years in jail when he is sentenced on 13th September.
If you’re considering a career of cybercrime, and think that hacking and identity theft could be your route to riches, just take a minute or two to reflect on how you could be making the worst decision of your life.
How would you feel, waiting to find out how many years of your life you’ll be wasting locked up in jail?


