The administrators of the PEAR package manager website have taken the site offline, having discovered that hackers breached the site, and planted a backdoor into the software.
PEAR (PHP Extension and Application Repository) is a framework and distribution system for reusable PHP components, making it easier for PHP developers – many of whom are creating websites – to reuse existing open-source libraries or packages rather than code from scratch.
Normally, PHP developers download PEAR from pear.php.net, but if you go there right now, this is what you will see…
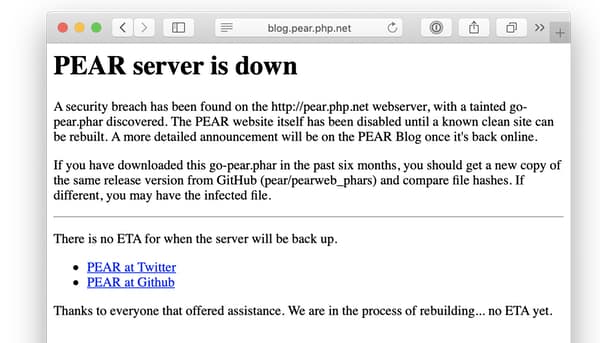
A security breach has been found on the http://pear.php.net webserver, with a tainted go-pear.phar discovered. The PEAR website itself has been disabled until a known clean site can be rebuilt. A more detailed announcement will be on the PEAR Blog once it’s back online.
If you have downloaded this go-pear.phar in the past six months, you should get a new copy of the same release version from GitHub (pear/pearweb_phars) and compare file hashes. If different, you may have the infected file.
What is perhaps most alarming is that it appears that anyone downloading and installing an updated edition from PEAR in the last half-year could have been compromised.
For once it’s quite a good thing if you weren’t diligently downloading every update for every piece of software running on your web server!
Users who wish to download an up-to-date and unaffected version of PEAR are being directed to Github.
No date has yet been given by the PEAR team as to when the pear.php.net website will return to normal service. My guess is that they could be some time – hopefully they’re thoroughly investigating how their website became compromised in the first place, and ensuring that no security holes exist that could allow a malicious attacker to simply break in again when the website is brought back up.
Readers with long memories will perhaps recall that this isn’t the first time one of the official PHP websites has been hacked to spread malware.