
Mobile security consultant Henry Hoggard uncovered a worrying failure in how PayPal had implemented its two-factor authentication (2FA) feature:
Recently I was in a hotel needing to make a payment, there was no phone signal so I could not receive my Two Factor Auth token. Luckily for me Paypal’s 2FA took less than five minutes to bypass.
Any suggestion that PayPal’s 2FA security is flawed is definitely a serious concern, so how did he do it?
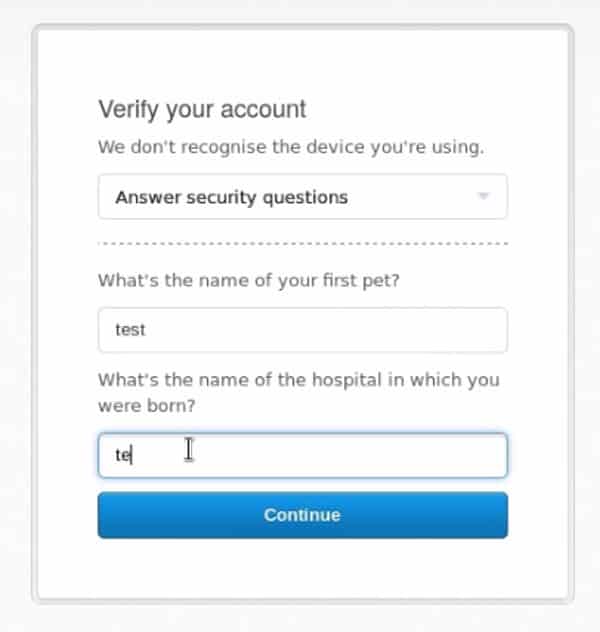
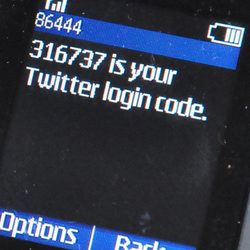
Well, if you don’t have your mobile easily to hand to receive your 2FA code from PayPal they’ll give you the option of answering your special security question instead.
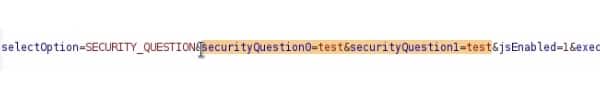
However, Hoggard discovered that meddling with the post data sent by his browser to remove securityQuestion0 and securityQuestion1 would trick PayPal into believing he had verified his account access.
Hoggard told PayPal about the vulnerability at the start of this month, and the company has now fixed the flaw and rewarded the researcher with a bug bounty.
Of course, attackers would not have been able to exploit this flaw unless they already knew a user’s password – but we know all too well that many users either choose weak passwords or reuse the same password on multiple sites. When built properly, two-factor authentication can make it harder for attackers to break into your account in these situations.
It’s great when websites offer their users two-factor and two-step verification, but they also need to ensure that they have implemented the feature securely.


Added to which, PayPal's 2FA didn't work at all on the mobile app last I checked, so the choice was to disable it and rely on a password only, or only use a desktop/laptop to send payments. I guess the board at PayPal/eBay view security as unworthy of serious investment, since they have a near-monopoly.
You've got a appreciate good old honestly and the fact he was rewarded for he's findings.
I vaguely recall PayPal offering 2FA via a rebranded Vasco token that cost $7 AUD some years ago. Off-the-grid 2FA (via a TOTP app or physical token) are better.
Answering some questions that's likely to be worked out by socially engineering is poor, regardless of whether the mechanism is flawed to begin with…
PayPal are notoriously insecure. In August this year another security researcher bypassed their 2SV.
https://shawarkhan.com/bypassed-paypals-2-factor-authentication/
There are dozens of vulnerabilities out there waiting to be exploited.
So tell them about each one, Bob, and get your rewards. With that many vulnerabilities, you can retire young. Wow. Dozens.
Enjoy your insights, Graham. Any way you can give us a hint as to the amount of the reward?
I'm afraid Hoggard hasn't shared that information in his blog post.
To this day, Paypal's 2FA is still not available in several countries, one being Belgium. That's bad.