Cybercriminals are up to their dirty tricks again, this time spamming out en masse a dangerous email carrying a Trojan horse.
The emails pretend to come from the “Customer Support” division of an online banking organisation and be in connection to payments requested from a variety of different organisations, using the subject line:
payment request from "[company name]"
Here’s just a small sample of the possible subject lines:

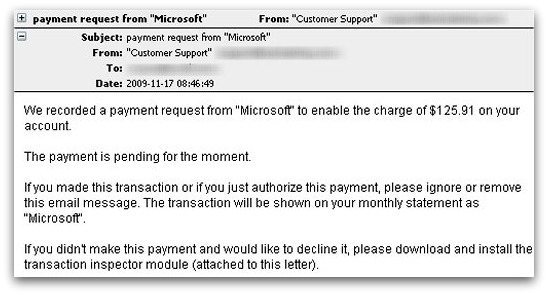
Here’s the text of a typical email, but remember that the company’s name and the amount of money that they are requesting payment for can vary:
We recorded a payment request from "Time Warner Cable" to enable the charge of $66.10 on your account.
The payment is pending for the moment.
If you made this transaction or if you just authorize this payment, please ignore or remove this email message. The transaction will be shown on your monthly statement as "Time Warner Cable".
If you didn't make this payment and would like to decline it, please download and install the transaction inspector module (attached to this letter).
Attached to the email is a file called module.zip.
Sophos proactively detects the attached malware as the Mal/EncPk-LP Trojan horse.
It’s clear that the hackers behind this attack are deliberately using a wide variety of company names and different payment amounts to try and make it harder to spread a warning about this threat. Remember to always be suspicious of unsolicited attachments.
If you panic and open the attachment thinking that you may be being billed in error, you could find that you have made a costly mistake.


