
The notorious Pawn Storm group exploited a Microsoft zero-day vulnerability in a number of spear-phishing campaigns before the tech giant had a chance to release a patch.
Trend Micro explains it saw the Russian hacking group abusing two zero-day bugs to target various governments and embassies around the world between 28 October 2016 and early November 2016:
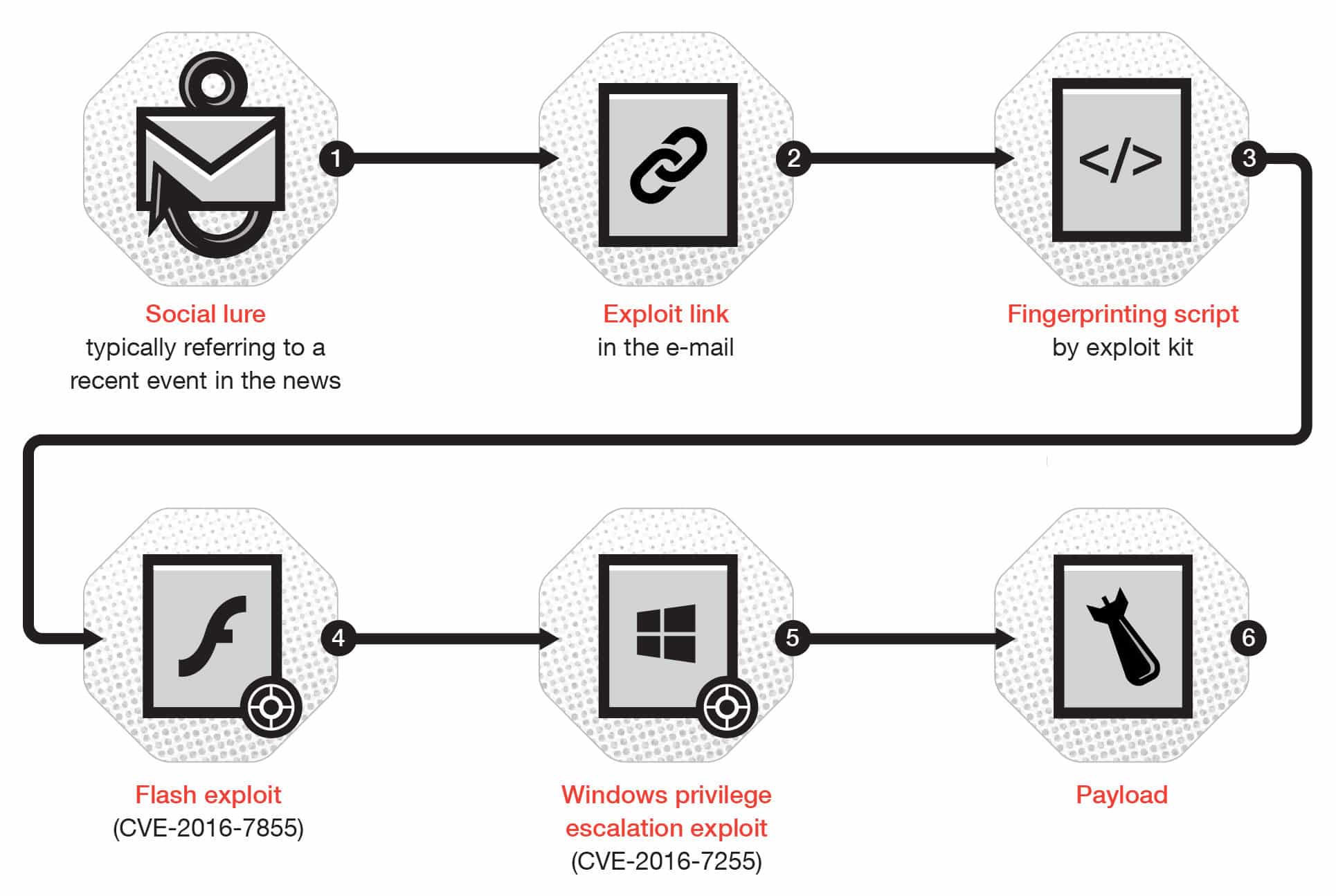
“In these campaigns, Pawn Storm used a previously unknown zero-day in Adobe’s Flash (CVE-2016-7855, fixed on October 26, 2016 with an emergency update) in combination with a privilege escalation in Microsoft’s Windows Operating System (CVE-2016-7255) that was fixed on November 8, 2016.”
In one campaign, the attackers spoofed the account of a press officer to send targets a fake email about nuclear threats in Europe. The email came with a link which, when clicked, directed victims to Pawn Storm’s exploit kit.
After collecting information about the target’s machine, the exploit server either redirected them to a benign server or sent over an exploit for one of the two security holes.
Another wave of attacks tricked recipients into thinking they had received an invitation to a threat intelligence and incident response conference in November.

Trend Micro says that campaign came with a malicious attachment called “Programm Details.doc”:
“Opening the RTF document (detected by Trend Micro as TROJ_ARTIEF.JEJOSU) would show the program details of the real conference, which was to be held in London in late November 2016. However, the RTF document has an embedded Flash file (SWF_CONEX.A) that downloads additional files from a remote server.”

By no means is this Pawn Storm’s first round of attacks. The hacking group, which also goes by the names “Sofacy” and “Fancy Bear,” has also conducted malware attacks against the aerospace industry and targeted journalists who investigated the crash of Flight MH17.
What makes these particular campaigns interesting, however, is that they abuse CVE-2016-7255.
Most of us learned about that Microsoft vulnerability when Google disclosed details about the bug in early November. It took Microsoft a week to close the hole, which means other attackers could have potentially launched their own attacks in that time frame.
Shame on you, Google! Competition is no reason to jeopardize users’ digital security. Your teams should have worked with Microsoft to raise awareness about the bug, an effort which should have went public once the latter released a fix.
I can only hope Google will make better decisions in the future. If not, perhaps its competitors won’t mind doing some irresponsible disclosure of their own, thereby further making the rest of us unsafe.


