When you log into your company’s email system when you’re working from home or on the road, do you see something like this?
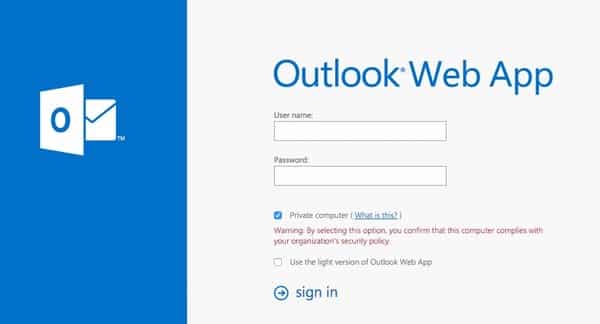
That’s the login page for Outlook Web App (formerly and commonly known as Outlook Web Access or OWA).
It runs on your company’s Exchange server to give you a web-friendly way of accessing your business email when you’re out of the office, and handles all the important business of authenticating that you are who you say you are – rather than some bad guy attempting to snaffle your firm’s secrets.
It does that by checking your login details against your business’s Active Directory server.
However, researchers at security firm Cybereason are claiming in a newly-released report that they have discovered malicious hackers targeting an unnamed company in a novel fashion in order to steal their employees’ OWA usernames and passwords, and access email accounts without permission.
 According to Cybereason, a suspicious DLL file was found on the server running Outlook Web App.
According to Cybereason, a suspicious DLL file was found on the server running Outlook Web App.
The DLL, which used the same name (OWAAUTH.DLL) as a legitimate part of Outlook Web App, was able to retrieve all HTTPS server requests in cleartext after they had been decrypted – grabbing the username and password of everybody who logged into the company using OWA.
The researchers report that they discovered a log file in the root directory of the server. Once decrypted, the log file revealed that some 11,000 username and password combinations had been logged from the company.
“This treasure trove essentially gave the hackers complete access to every identity and therefore every asset in the organization.”
With that information, the malicious hackers could read sensitive communications, impersonate members of staff, but more than that… with the malicious DLL in place the attackers had opened a backdoor, giving them covert access to the server.
Questions remain, of course, as to how the attackers were able to gain remote access to the OWA server to plant the malicious DLL in the first place. One has to consider the possibility that the code was placed on the server with some internal assistance.
The Cybereason report says that they have only uncovered this particular attack at one company and that it appears to have continued for “several months”.
But, in my opinion, it sounds like the kind of intrusion that would be attractive to criminals and intelligence agencies alike, keen to snoop upon the communications and activities of a targeted organisation, or to spy upon a partner or customer of an organisation that is of special interest.
Chances are that there may be more companies and organisations out there who are unaware that their Outlook Web Application has been compromised, and is spilling secrets into the hands of hackers.


I had two thoughts when I read this report today.
The first was that the firm is purely pushing for business – and not giving any real information in the process. I mean, it's pretty clear from the exploit that there had to be other vectors at play for it to work.
The second was, what exactly was the state of their environment, security around it etc, in order for this to have been possible – and not traceable. The process itself is pretty interesting in that they have been able to essentially inject into OWA, but it's not exactly complex – but it does need escalated access to the box.
Generally, I classed it (almost) a non-issue … feels too much like a commercial "look at us" type piece.
Andy
Thanks for commenting Andy.
I think that's a not unreasonable point of view
Regardless of Cybereason's motivation for issuing the report, I think it's still a timely warning to companies that they should keep a close eye on the security of their OWA servers, including who they grant access to it – and bear in mind that this is a potential vector for passwords to be hoovered up.
I would say that the fact they left a log file in the *root* directory is hardly untraceable or undetectable.
Traceable is up to interpretation but still, to have a log file in the root directory – it boggles my mind they hadn't discovered it sooner.
A few things we'd like to emphasize:
The hackers managed to obtain access to this server using stolen credentials. The problem is that this server was in a very unique position. On one hand it's completely internet facing and on the other hand, it is a focal point for the full credentials of all employees in the organization. Companies should be wary of using this server without requiring VPN (although this is usually its biggest advantage) and at the very least, require 2FA (2 factor authentication). As always, companies should adopt a mindset assuming they're already breached. Even having all these passwords is not the endgame for the hackers, but just another step.
"The researchers report that they discovered a log file in the root directory of the server."
As I already hinted at, that was really stupid of them. But the fact it worked for long is the real mystery (and problem).
I'm also pointing out the irony that the letters OWA are the first three letters in OWASP and that they logon to a website.