
If you weren’t nervous enough about the prospect of meeting a complete stranger after connecting on an online dating app, there’s something else to worry about.
Just how carefully is your app keeping your personal information and location out of other people’s sight?
Researchers at Kaspersky have taken a look at a number of online dating apps for Android and iOS, and found that some are doing a pretty poor job of securing users’ details.
Firstly, some apps encourage users to enter their place of work on their profile:
First of all, we checked how easy it was to track users with the data available in the app. If the app included an option to show your place of work, it was fairly easy to match the name of a user and their page on a social network. This in turn could allow criminals to gather much more data about the victim, track their movements, identify their circle of friends and acquaintances. This data can then be used to stalk the victim.
More specifically, in Tinder, Happn and Bumble users can add information about their job and education. Using that information, we managed in 60% of cases to identify users’ pages on various social media, including Facebook and LinkedIn, as well as their full names and surnames.
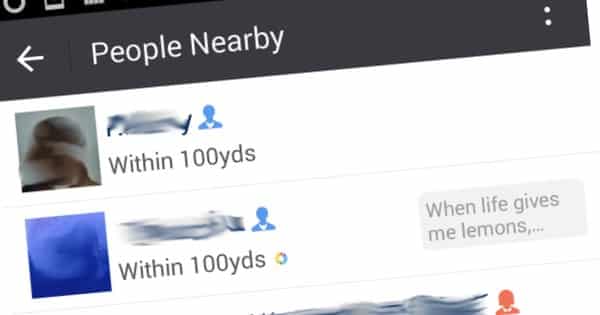
In addition, some dating apps were found to track users’ location – displaying the distance between a malicious party and a target. If a target was staying in one place, a hacker could feed an app bogus co-ordinates and receive information about their relative distance to track down the location of the person they were interested in.
The researchers reported that users of the Tinder, Mamba, Zoosk, Happn, WeChat, and Paktor apps were particularly susceptible to having their location determined.
Meanwhile, some apps were guilty of elementary security failures – transmitting sensitive information in an unencrypted format, opening opportunities for an attack to intercept the data in transit:
Most of the applications use SSL when communicating with a server, but some things remain unencrypted. For example, Tinder, Paktor and Bumble for Android and the iOS version of Badoo upload photos via HTTP, i.e., in unencrypted format. This allows an attacker, for example, to see which accounts the victim is currently viewing.
So, what should you do about this?
The first rule has to always be to think carefully about what information you share online (including in dating apps). Even if the information you have provided to the app isn’t in itself enough to identify you, remember that chances are that you have left plenty of other information about yourself lying across the internet (maybe on Facebook on LinkedIn for instance) which will help someone to track you down.
 It may even be possible for an attacker to conduct what are known as “reverse image searches”, where rather than type words into a search engine to look for something, someone could use the image that you have posted on a dating app and see if a similar image appears anywhere else online.
It may even be possible for an attacker to conduct what are known as “reverse image searches”, where rather than type words into a search engine to look for something, someone could use the image that you have posted on a dating app and see if a similar image appears anywhere else online.
My guess is that many people may be quite happy using the same flattering snap of themselves in a dating app as on a social network or Instagram.
The other issue is that clearly some of these apps are poorly written. Your dating app may contain vulnerabilities that could lead to you unwittingly leaking your personal information, or provide clues that could lead someone to determining your true identity or location.
Depending on the vulnerability there may or may not be ways in which you can protect yourself from this – but I would always recommend using a secure VPN to protect your privacy when connected to the net via public Wi-Fi (even better use 3G or 4G if you’re unsure about the Wi-Fi) and as a general rule only share information you don’t mind ending up appearing in public online.



What is the risk here? So the hacker knows my name, my employer, my alma mater, and my location? Then what?
If you read dating services' TOS and Privacy Policies you'll find plenty of grist for concern about their handling of literally everything you submit to them. Common issues include dating site takes a permanent license to use everything submitted (text, pics, etc) in all possible ways by them and all affiliates/transferees/assigns, data transferred about you or your ad copy & pic not subject to the same privacy provisions as the original site, no right of the 'customer' to know/review/approve what's retained/whether & how it's used by all affiliates/transferred/sold, no info about how the customer's info would be protected from exposure including upon transfer to others, no right of compensation for what's done with the info by the host, and no transparency into any of this beyond the TOS & Privacy Policy. The only way, hopefully, to end any of this or take control is to terminate the account.
Now put this in practical terms: You submit an paid ad with a facial pic to one of the big dating sites, they also get all your billing and other account info for internal uses. It's a big company with affiliates and an active marketing program. Their affiliates include ones in niche interest areas, some of which you would not want to be associated with in any way, but the company forwards your original ad info & pic to their niche site affiliate teams for seeding their count of 'members' for their marketers. So your ad, or parts of it, maybe the topic, your original text edited to suite the niche and your face attached. The company also sends out emails to mass lists of potential customers for the original site you submitted the ad to or for a niche site you have no intention of advertising in. No matter, respondents to your faked ad won't know why their responses go unanswered and only rarely will those niche site responses will be forwarded to you. You also won't know if your coworkers, family or anyone else got one of those marketing emails with your face on it, touting how great that niche site is. Or if law enforcement, insurers, employers, prospective employers, the university you applied to, the DoD, credit reporting agencies, or people you do business with has scraped any of the fraudulent ads or marketing using your mug into their dossiers about you. All without any notice or transparency to you, or your ability to control it. From your innocent ad looking for a partner in life……