If you’ve used Microsoft Windows for any length of time, then a dialog box like this will be no stranger to you:
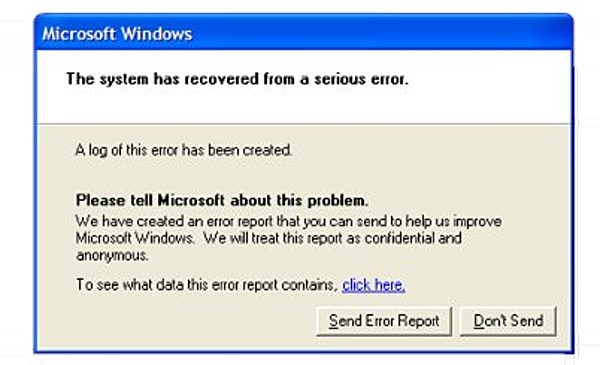
You may think that it’s harmless enough to click on the “Send Error Report” button and send details of the crash to Microsoft, but recent revelations about NSA surveillance underline that there are risks.
For instance, did you realise that by default Windows crash reports are sent unencrypted, potentially exposing information about the setup of your computers?
Indeed, according to a leaked presentation seen by Der Spiegel, the NSA’s TAO (Tailored Access Operations) division can be automatically notified whenever a targeted computer sends a crash report.
The automated crash reports are a “neat way” to gain “passive access” to a machine, the presentation continues. Passive access means that, initially, only data the computer sends out into the Internet is captured and saved, but the computer itself is not yet manipulated. Still, even this passive access to error messages provides valuable insights into problems with a targeted person’s computer and, thus, information on security holes that might be exploitable for planting malware or spyware on the unwitting victim’s computer.
To understand more about the threat, check out this investigation from the researchers at Websense.
Bizarrely, whoever created the NSA presentation found the interception of the Windows crash error reports so amusing that they mocked up a version of the familiar dialog with their own wording,
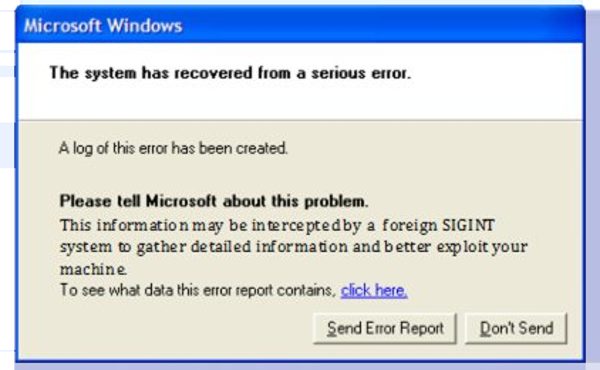
Truly bizarre.
If (unlike the NSA) you fail to see the funny side of this, and want to prevent computers in your organisation from sending Windows Error reports to Microsoft (and potential snoopers) you may wish to make a group policy setting change.
And maybe it would be good if Microsoft made some changes at its end too, ensuring that future crash reports are sent properly encrypted.



I can imagine the phone calls "Hi, this is Steve from the National Security Agency, your computer has been reporting a problem and we are here to help fix it for free. We already have remote access but if you could visit this site and download the software it will fix the problem. Oh wait I've seen something else, that'll be £39.99 please to remove."