By the middle of 2012, the NSA had infected more than 50,000 computer systems around the world with malware.
That’s according to secret documents, leaked by NSA whistleblower Edward Snowden, detailed in a report from Dutch newspaper NRC Handelsblad this weekend.
Presentation slides seen by the newspaper show a map of the world, showing access that the NSA has gained to computer networks and data connections across the globe.
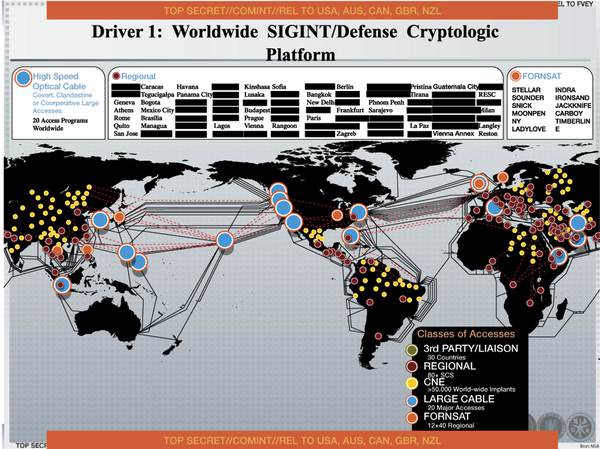
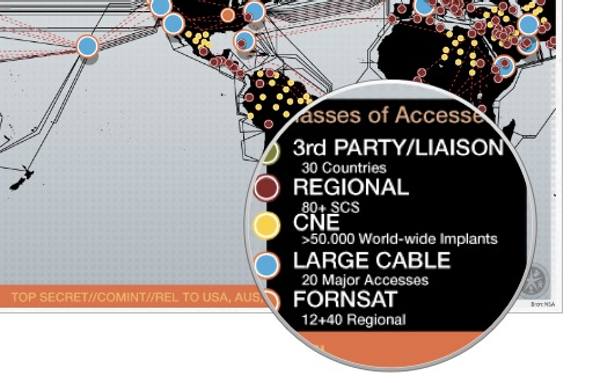
The NSA has a term for the planting of malware inside computer networks – “Computer Network Exploitation”, or CNE for short.
A specialist NSA department known as TAO (Tailored Access Operations) employs over a thousand hackers to help them break into computer networks and plant malware.
The malware, of course, is not the financially-motivated malware typically seen by regular computer users – but instead designed to not draw attention to itself, waiting for months or maybe years until required to steal information from compromised systems and feed it back to its spymasters.
As NRC Handelsblad describes it:
The malware can be controlled remotely and be turned on and off at will. The ‘implants’ act as digital ‘sleeper cells’ that can be activated with a single push of a button.
 Clearly, conventional criminal gangs aren’t the only people interested in breaking into computer networks anymore, and all organisations need to ask themselves the question of whether they could be at risk.
Clearly, conventional criminal gangs aren’t the only people interested in breaking into computer networks anymore, and all organisations need to ask themselves the question of whether they could be at risk.
Even if you don’t think that your company’s data would be of interest to the NSA, GCHQ or another foreign power, it’s possible that you have a customer who is of interest to them, or are part of a supply chain that could lead to an espionage agency’s ultimate target.
For that reason, all organisations have to protect their systems with the highest diligence, and cannot easily assume they might not be a potential victim of state-sponsored espionage.
Anti-virus veteran Mikko Hypponen summed up the situation well in an article published on this site last month: “who we’re fighting has completely changed in the last decade”.
Read more in the NRC Handelsblad report.



Wow! Fantastic article, terrifying story! The fact is we
HAVE to do something about the Patriot Act which has allowed for
this kind of crap. How that bill ever passed Congress I
don't know. Wait I do know… those idiots never read the
thing and those who did either didn't give a sh@t, were
compete idiots, or had something to gain from it (or all of the
above). Why aren't people more up in arms about that f-ing
act? I know there are organizations like the ACLU, the Electronic
Privacy Information Center and the Electronic Frontier Foundation
that are trying to get a ground swell going but nothing seems to be
moving. Maybe it's just me but we have to get the media on
board with this and get them to stop talking about 2016 election,
some blah, blah about Canadian crack smoking mayors, whose tweeting
whose wang, George Zimmerman, the knockout game, Sarah Palin
gossip, bears crashing birthday parties, yada yada.
The only surprising thing – to someone who has been into computer security for the past two decades, anyway – is the number is rather low. Nothing else surprises me. The NSA has a loooong history of this type of thing. I remember way back in 2000 they (and possibly the DOD and/or DOJ – I cannot find the document in question so cannot confirm this) were having problems with encryption standards (problems meaning concerns about not being able to break it). The problem is, as Bruce Schneier pointed out about the revelations (of the NSA spying activity), is that when you have weak encryption (or encryption with backdoors or otherwise data being sent in the clear or – with some things – stored unencrypted) is twofold:
1. It gives a false sense of security (security through obscurity, anyone?!) including to those relying on not weakened encryption.
2. It actually does the exact opposite of what they claim its purpose is for: by having weaknesses it risks information of citizens (including – potentially – confidential information) being discovered and I wonder (obviously a rhetorical question) how identify theft happens? Same goes for stolen credit card details and same for so many other things. So they can claim all they want that it is to protect the citizens but they're actually making things worse (not even considering storing information! that is another issue entirely).
Otherwise, I don't really find this information shocking or scary, because while this is just another example it has been going on for many many years. And Deborah, you're right that the patriot act is a problem but unfortunately you're wrong that they don't read it. It's more like they don't actually care: it gives them more power and that's all they want (and keep in mind: power corrupts, so the more power they get the more power they want and the more corrupt they get). I can think of three people (of many others) who put the issue of congress quite well (one is me and I'm not famous or well known and I'd rather keep it that way):
Mark Twain, who wrote/said three things (well, these are three of the things he said about congress, anyway):
"Fleas can be taught nearly anything that a Congressman can."
– What Is Man?
"All Congresses and Parliaments have a kindly feeling for idiots, and a compassion for them, on account of personal experience and heredity."
– Mark Twain's Autobiography; also in Mark Twain in Eruption
Suppose you were an idiot. And suppose you were a member of Congress. But I repeat myself.
– Mark Twain, a Biography
And Gore Vidal who said:
"The United States was founded by the brightest people in the country – and we haven't seen them since."
(though personally I think that the fact certain things are possible means they were not so bright but the point remains the same: politicians are not exactly expected to be all there in the head).
Otherwise, the EFF and the like can only do so much. They've done a lot of good but they can't solve all the problems and realistically you can't expect them to (because it is impossible). Thus is life…