
On the latest “Smashing Security” podcast we discussed the merits (or otherwise) of Nike’s innovative Adapt BB sneakers – wirelessly-charged self-lacing shoes.
With our most cynical heads on, we imagined a future where Nike would be able to track shoe owners and collect their personal information – data that could potentially be monetised.
Listen on Apple Podcasts | Spotify | Pocket Casts | Other... | RSS
More episodes...
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
You can just see the tech workers running into conference rooms and unplugging all the machines. So, it wasn't your typical day at the office.
It takes quite a lot for an IT guy to run as well. It's quite serious. Normally they're kind of slouching along, aren't they, just loafing around. It's whoa, we've got a big problem here. Smashing Security, episode 116. Stalking debtors, Facebook farce, and a cyber insurance snag, with Carole Theriault and Graham Cluley. Hello, hello, and welcome to Smashing Security, episode 116. My name is Graham Cluley. And I'm Carole Theriault. Hello, Carole. Hello. Hello. Well, we are joined today by a special guest. He's brand new to the show. It's Joe Carrigan. Is it Carrigan or Corrigan? Carrigan. With an A.
Welcome to the show, Joe.
I said it, and then I wasn't sure. Nope. You said it right the first time. Oh, God. See? I have so much self-doubt. Joe, you are, because you probably need reminding, a senior security engineer with the Information Security Institute at Johns Hopkins University. Oh, yeah. That's right.
Yeah. And you're the co-host of the Hacking Humans podcast, part of the CyberWire Network.
Yes, with Dave Bittner. Dave. Who has been a guest on this show. Bittner. He has. Bittner. Bittner. B-I-T-T-N-E-R.
I'll have to look back. I don't remember. I don't remember.
So is he not nervous that you might outperform him on the show? He should be.
I don't know if he's nervous or not.
We're going to find out on Twitter when he gets all riled up. Right.
We'll rile him up for sure. So what have we got coming up, Carole?
Well, buckle up, listeners. We have a doozy this week. Graham, you're investigating the novel ways a naughty app developer might track your whereabouts. Joe, you're sharing a Facebook snafu designed to fool even the tech savvy. And I've got a cautionary tale starring a malware victim and their cyber insurance policy. All this and oodles more coming up on Smashing Security. Don't move a muscle.
Now, fellows, word has reached us from China about what the police are doing over there. They have just arrested an app developer. Okay. Police in Nanjing, East China's Jiangsu province, have arrested a 30-year-old man known only by the surname of Wu.
I kind of like that. You like that? Yeah, I'd love to have a name that was just two letters long. Everyone would remember it. Kind of cool.
Theriault is kind of hard to remember how to spell.
Yes, it's even hard for the French people.
Well, Mr. Wu, his full name is Mr. Wu, is a computer engineering graduate. And he created an app called App Detective. Oh, my God.
I would download that just on the name alone. What does it do?
Well, App Detective breaks into a smartphone's instant message database. Imagine you're using WhatsApp or something like that, or the local Chinese equivalent, and it grabs the user's location. So far, pretty creepy stuff, right? Yeah, okay.
I wasn't thinking that. No, it's not the kind of app you would want to install, quite frankly. Right.
So why have police arrested him? What have they said that he's doing with his app? Well, apparently he was selling this app to debt collectors who would track their target's whereabouts. And some 4,000 people have paid as little as one yuan, which is 15 cents, to get people's static location or the extraordinarily high price of 10 yuan, which is about $1.50, to track their target's movements in real time.
Okay, okay, okay. So people that are downloading this are trying to keep track of what their wife or husband or their kid or…
Well, this is the thing. You would normally expect that, wouldn't you? And there are plenty of apps, of course, which are sold on the basis of, you know, oh, keep a caring eye on your partner and on your children. Reality is, are they cheating on you?
Those are owned and operated by creeps.
Yes, exactly. Well, in this particular case, he was selling it, it seems, primarily to debt collectors and bounty hunters. So people who are trying to track somebody down and it can be very difficult tracking someone down. I remember, Carole, do you remember years ago when I did a little bit of tracking for you? Me and our buddy Stevie Butts, we were around our friend Petra's house and you said that there was a man in the neighboring pub who you wanted to keep track of. I think it was a potential boyfriend or something and Stevie and I hid, we disguised ourselves quite well.
You guys took Petra's towel, put it over your heads and then looked through the pub window to see if he was there or not. And Petra and I were watching you from the attic window, killing ourselves.
How did you see through the towel? Did you cut holes in the towel? Our principle was, if you've ever read Hitchhiker's Guide to the Galaxy and the Bugblatter Beast of Traal, the beast is so dumb that it believes if it can't see you, you won't be able to see it. So we took the principle of putting a blanket over our heads. If we couldn't see, maybe we would…
Absolutely no alcohol was involved in any of this at all, Joe, I assure you.
I'm sure of that, yeah.
If only it had been, that would have been more understandable. But yes, so I understand the difficulty of tracking someone and, you know, finding your quarry. Nice segue. But this app, it appears, no towels were required. Debt collectors just could simply trick their target into installing the app.
Okay, now that's actually the crux of my question. How does a debt collector trick someone they want to collect a debt from into installing this app?
How naive are you, Joe? It's so simple to do something that. I mean, I think it's really up to the purchaser how they choose to want to do it. But if you were to offer someone something a, I don't know, 100 sexy wallpapers app or something that, or free ringtones. Yes, free ringtones. That's the hook that always catches me. Then some people would install it.
But how do you weed out the people that you want to collect debt from versus the ones that are just...
Well, you would send a link, wouldn't you? You would send a link to the specific people. Yeah, you have their email addresses, presumably, right?
Yeah. Okay. So I have a list of people that are in debt, an email address. I then try and hook them in with a little fishy email saying, hey, hey, get this app. It's really cool.
You fish them and they install this malicious app and then bang, you know where they are.
So the idea is that people that go into debt really just want to track people. Oh, no, no, they're being tracked.
It's them being tracked by the people they owe money to, or at least the debt collectors who are going to collect it. So the heavies are going to come around. All they need to know is where you are at a particular time.
And then Moose and Rocco show up. Gotcha. The app helps them do this. And apparently the app was quite good at its job. It was capable of determining people's location within a margin of error of about 20 meters. And in all, the app is said to have made about $60,000, which is quite a lot of money when you consider that they were charging as little as 15 cents per go. There was a lot of activity going on here. That's too many permissions for free ringtones and sexy wallpapers.
But if the app manages to actually instead crack your phone to grab the information from your instant messaging app, if it's able to query that, maybe through a vulnerability or maybe because you're running an old version of Android which doesn't have good enough security, then that might be a more effective way to do it. I don't know, but that's my theory as to why they're doing it that way.
It seems plausible to me. It's certainly plausible. I would agree it's plausible.
Now, he has been prosecuted now, Mr. Wu, for allegedly writing the apps and stealing personal information. And two other frequent users of the app have been nabbed and are awaiting prosecution. But all of this got me thinking, what other novel ways might there be of tracking people? After all, you've got to trick someone into loading the app onto your smartphone. And it was at this point that one of our devoted Smashing Security listeners, Sarah Gatzky, she tweeted me and she pointed me towards a thread on Twitter about a brand new pair of shoes. Now, do you guys remember Back to the Future 2 with Michael J. Fox? Not the original! Back to the Future 2, which has a pair of self-lacing shoes in it. He wears these Nikes which sort of do themselves up because he goes into the future.
I do remember seeing that. I think that's the only Back to the Future I haven't seen. I've seen one and three, but I don't think I've seen two.
I remember this, definitely remember this, because I thought that why not just use Velcro, basically. Because they don't do it automatically, Carole. That was the whole thing. Well, did you know that a few years later, Nike actually produced a limited run of shoes them? They sort of copied the design. Marketing geniuses. And in combination with Michael J. Fox's foundation, which fights Parkinson's and so forth, they auctioned off a few hundred of these for a vast amount of money. And they raised a lot of money for charity, which is obviously fantastic. Oh, they're not smart shoes, are they?
These shoes, they will only set you back $350.
Which is not bad, right, for self-lacing shoes. I would expect that to be a lot higher.
You wouldn't have to bend over, right?
That would help me so much. I could breathe while tying my shoes.
They remember how tight you your shoes. They pair over Bluetooth. They receive software updates. We'll link to the tweet where someone has actually put up a screenshot of their phone of their shoes. Updating the software on your shoes. Being charged wirelessly on a USB-C charging mat.
Oh, why? While receiving a software update. What's the point? What's the point? What is the point? The future is stupid. Yes, that's exactly, yes.
All kinds of questions spring to mind here, right? Would you be allowed to take these on a plane? Does it need batteries? Oh, yes, it needs batteries. They're not like a pair of AA batteries, Carole.
Here's another issue I have with this. If these batteries are on presumably a very mobile part of your body, probably the part of your body that endures the most g-force during the course of a day, how safe are those batteries?
Lithium there, right? These apparently the BB stands for basketball, so you can imagine it would be quite a rough sort of, you know, it's not a gentle stroll, is it? It's a lot of sudden stops and starts. They have got a battery inside them, a microcontroller, an accelerometer, a gyroscope, a temperature sensor, a motor, a light. They've got little lights at the side.
Can they stop you if something dangerous comes across your path?
They can't do that automatic braking. And of course, by the way, there's an app. So you can actually go to your app to tighten the left or right shoe, or you can press a button on the side of the shoe.
Does it alert you if there's any damage on the skin? Alert! Alert! Small chafing of leather.
I think the idea is that they monitor the temperature so that they can loosen over time. In case you get sweaty.
They don't have fans that cool your feet off?
Now, you are thinking, and I assumed the same, that this app and these sneakers would be tracking your location and your activity and counting steps. Well, apparently they aren't yet. But it sounds like it'd be an easy thing to add via a firmware update or adding new features to the app. But it's kind of inevitable that they will do at some point, won't they? Or the next version will.
Right. And you don't even have to update the firmware on the shoes. You just have to update the app. Because the shoes probably don't have a GPS receiver in them. But the phone does.
Right. And so it's being all collected. You know, you have to wonder what will, in the future, shoe manufacturers be planning to do with all that data? And I'm thinking, if you're finding it hard to get someone to install the app with the ringtones and the sexy wallpaper, send them a pair of sneakers.
Or tell them they won them. $350. Just send them willy-nilly. What kind of businessman are you?
Okay, so let's look at the business model here for a second. I'm a collections person, right? So I have to spend $350 for a pair of shoes. So that means that I have to have a bill to collect that's going to profit me at least $350, right?
You'll get the shoes back. When you collect it, you rip them off his feet and say, oi, they're mine. Anyway, and in the future, the sneakers will be cheaper as well. This is the future of sneakers, right? Already, you don't need to put fuel in them, do you? Well, you do have to charge them. You have to charge them every fortnight, apparently.
That's pretty good for a pair of shoes. I would have thought more than that.
But it's not just for debt collection, right? It's not just for tracking people. In the future, shoe manufacturers will know where you're going. They'll know if you stop for donuts. They know if you're exercising.
Well, they don't need your shoes for that. They can do it through your phone now.
They can monetize that data. Yes, but it's going to be happening more and more. Okay, great story. And if you're dumb enough to spend $350 on sneakers, you've got other money to burn probably, which big companies are going to be able to exploit, aren't they? I've just given you a vision of the future. You can call me Nostradamus if you wish. That's the first word that came to mind. I am seeing an image of the future and where things are going. All right. So, Joe, have you got a story for us?
Of course. So imagine that you are minding your own business, sitting at home and someone sends you a URL that says something like, hey, take a look at this on Facebook.
Okay. I would be like, oh, I don't have Facebook. But I'll imagine if I did.
Lucky you. I got to tell you, I have used Facebook less and less. The only reason I keep it around is to communicate with family. But ever since I stopped just getting on there on a regular basis, I find myself living a much happier life.
Listen, people out there. Listen to Joe. Get off it.
Yeah. No Facebook February, right? That's what we believe in. Give it a try. Try and stop for a month.
Right. So you're astute. You look at the URL, and it does indeed point to Facebook. It says facebook.com, and it has some other stuff after it. And you say, okay, I'll look at this. And bam, you very quickly lose control of your own Facebook account. How would this have happened?
So this isn't phishing. It isn't taking you to a login page?
It is phishing. It's a phishing email that they're sending you or a phishing message or something. But it is going to a Facebook page. So what has happened is there is a researcher, Sam Ouda. I hope I'm saying that right. It's a hacker alias, I guess. The O is a zero. And he found a vulnerable endpoint on Facebook at the URL facebook.com slash comet slash dialogue underscore do not use. What?
That's the kind of thing I would do in one of my files.
Right. It's like a button which says, do not press. Yeah, don't press. What is The first thing that a hacker does when you tell him or her not to use something? What happens when you do that to a two-year-old?
Oh, let's do more of that, please.
There you go, Carole. This is your mission in life now, right? And finally, the one thing that allows the account takeover is they could change the user's email address. And that's the key of taking over the account because if you've changed the email address, now you click on a link that says, oh, silly me, I forgot my password. Send me an email to reset it. And you get the email and then you go in, you can reset the password. And once you have access and once you've logged into the Facebook account, you can log the user out of all their other locations and you have control of the account. Okay. So tell me, unless someone had the same usernames and other accounts, what is the joy of having access to a Facebook account? I guess if they're just doing it for the lols, they can mess somebody's life up. They could impersonate somebody. It's horrendous. And imagine, for instance, you could have a jealous stalker or something like that, or an ex-partner who wanted to read your messages and so they want to break into the account.
Yes, you could. There's a very good use case for this vulnerability.
Oh, I don't want to give anyone ideas. Too late. It actually is too late because Sam Ouda informed Facebook about this bug on January 26th of this year. And by the 31st, only five days later, Facebook had fixed the bug.
Blow me away. That sounds almost reasonable, guys.
I wonder how they write the check for Mr. Sammy Zero Uda.
I don't know how they do that. I imagine that they actually have his real name and they probably put him through a non-disclosure agreement stuff.
Yeah. I mean, this seems like a pretty tragic error for them to make, leaving this thing with the... Was their fix simply to rename it from dialogue do not use to dialogue no really, really do not use?
I would imagine that Facebook actually did fix it. They probably just took it down. They probably just turned that machine off.
How many other things like this might be lurking out there?
Well, you never know. There is absolutely no such thing as a perfectly secure system. That's something we tell people over and over and over again. The key of this vulnerability is that it was found on the Facebook network. So it would have appeared like a legitimate Facebook link. It would have worked. And there would have been nothing that Facebook would have had cognizance about unless they were tracking the usage of the do not use address. But I would like to say kudos to Sam Ouda for finding and reporting this bug and kudos to Facebook. There's something you don't hear every day, right?
They'll be really happy to know that they've had some good news from us. They think finally. Wasn't the UK
Government, they called them digital gangsters last week? So yeah, they're going to be really touched. They're probably having tears of joy right now and listening to your story, Joe.
Kudos to Facebook for handling this so quickly and for paying a substantial bug bounty. You know, one of my jobs here is to disclose vulnerabilities that we find and nine times out of ten I disclose a vulnerability to a company and I never hear anything back from them. Nothing.
Well you know, a tiny silver lining or otherwise big dark crazy cloud of Facebook.
Yeah exactly. But it is fixed, so you can't do this anymore.
Well, not with that URL. I wonder how he found it. Yeah. It's bizarre, isn't it? Poking around. Yeah. Crawl, crawl, crawl. How are you able to poke around Facebook to that extent to find a URL like that? That suggests to me that maybe they haven't locked down some things. Or maybe it's an ex-employee. Crawl through. Knows his way around. Could be an ex-employee. The gardens. He probably planted it. Could be a current employee.
Oh, the conspiracy theory. You're just, what are you, Alex Jones?
There is a similarity. If you saw both of us sat behind the decks turning purple in anger at the world. Oh, Carole, don't get me all riled up. What have you got for us? Please, God. Let me take you guys back to the crazy summer of 2017. So this was the year that Trump was inaugurated, began befriending Kim Jong-un. And this podcast Smashing Security was just still a little wee baby. It takes quite a lot for an IT guy to run as well. It's quite serious. Normally they're kind of slouching along, aren't they? Just loafing around. But it's, whoa, they're running. We've got a big problem here. They even said staffers were hurtling themselves over locked keycard gates, which had been paralyzed by the still mysterious malware. You should really read this article. It's fantastic. So they're a big, yeah, they're big. So do they own Nabisco, then? Oh, really? I didn't know that.
So that's $100 million in lost revenue and then $84 million in recovery.
And it would have been so much less if those IT guys had just shifted their asses a bit faster, right? Did they put that in the report? Well, those were the guys at Maersk that were running around doing that.
But I'm sure Mondelez were doing exactly the same thing.
No, they weren't. They were stuffing themselves of Oreo cookies and Cadbury's chocolate bars.
Popcorn and sweeties. Exactly. Can you imagine? Kraft dinner.
Don't even put Oreo cookies in front of me.
You love them?
I do. You go crazy for them. I love them so much.
So basically, Mondelez say they're almost $200 million out of pocket, right? And this is only 1% of their turnover for the year, by the way.
But that's 1% of their revenue. Pretty substantial. So now before you say poor, poor Mondelez, you should know that they had cyber insurance with a company called Zurich Insurance. I'm sure that they took care of everything.
Exactly, Joe. They're so smart, right?
They're a good insurance company, and insurance companies always pay out whenever you have an incident for which you have insured yourself.
Exactly. Just in case someone nips past your approved and reviewed defenses, you can insure yourself to recoup any losses. Great. Makes perfect sense. So if you go to the Zurich Insurance website, it says, enhance your cyber resilience with Zurich security and privacy coverage. Yes, let's do it. And the marketing blurb touts first-party coverage includes digital asset replacement, expense coverage, business income loss, independent business income loss coverage, cyber extortion threat, and reward payment coverage. Basically, we'll pay for everything. Just give us some money.
I'm signing up right now. Sounds worth it to me. I'm signing up.
The entire $200 million that Mondelez lost is coming back to them thanks to their policy with Zurich. Exactly. Good. I'm glad this story ends this way.
You have to imagine it wouldn't have been cheap, right? It wouldn't have been chump change that they would have asked for to protect Mondelez, right? It's a big company.
Yeah, that policy could not have been inexpensive. Perhaps no surprise to you both that the Kraft food company Mondelez put together an insurance claim. And filed the paperwork and waited for payday. Ka-ching!
Yeah, well, sometimes it can take a while. It can take a while. Wheels are in motion, it'll come, it'll come in soon, it'll arrive soon, the check's in the post. In January this year, instead of getting a check, Mondelez got the news that Zurich Insurance weren't going to honor the payment. They were refusing to foot the bill, and I was really how shocking, an insurance company not prepared to pay up. Yeah, well, it just seems to me that maybe Mondelez need to sue the US and UK governments for concluding that it was Russia, because if they hadn't done that, they would have got their payout. And maybe Mondelez needs to threaten the US and UK governments with a bombardment of Oreo cookies.
You're stealing my story. That's my big, I'm getting there.
Oh, sorry.
Sorry.
Great minds. Very great minds. That never happened. Joe, have you got any theories?
How Mondelez can do this is they can stop shipping Oreos and Cadbury bars to Russia until they get their $200 million, right?
Hold them ransom, right? Yeah, to their sweet tooth. Sorry, go on.
Carry on, I was fascinated.
No, no, it's good, it's good. So Moscow, of course, is denying being behind the attack and calls the claims Russia-phobic. But an assessment from the National Cyber Security Centre in the UK clearly states that Russia military was almost certainly, and I'm quoting here, almost certainly responsible for the NotPetya cyber attack of June 2017. So it seems that companies can be collateral damage when governments publicly blame other countries for hacks. So now I'll insert what you just said, Graham, earlier. What's the point? What's the point of governments publicly blaming other countries for hacks anyway? Well, you know, in this case, don't you think the US would want to take the heat off itself because the malware used an NSA bit of code? So it really wanted to kind of say, oh, you see, it wasn't our fault. It was stolen from us, used by the Russians. They're really, really great at hacking and stuff, right? So there is no precedent for calling a cyber event an act of war as yet.
That was my thought, is that there hasn't been a clear definition of what constitutes an act of war based on a cyber attack. There's no clear boundary across the planet as to what that is.
Exactly. And it poses a bit of a pickle, right? Because now who's going to win? Is the insurance company going to be able to get out of this and think of the other clients it's been able to sell its insurance to. Well, you know what? It is kind of about time the insurance companies came out properly and positively from one of these things because so often they're paying out, aren't they? Something similar happened on 9/11 when all those people were killed in the World Trade Center and the flight that crashed in Pennsylvania. Insurance companies said, well, this is an act of war, we're not going to pay out. Well, that's good news for Mondelez because they are seemingly a bit pissed at this response from their insurers who they've been paying for this exact reason. And they've decided to roll up their sleeves and fight for payday.
Presumably Zurich Insurance is itself insured against getting sued.
There is a lot of that. And that's one of the big problems in the whole chain, because insurers have backers that insure them against losses. And then those insurers have backers. So there's this huge chain of money. And one of the problems they're seeing in the industry is that backers are going to demand more collateral. So anyway, it's going to be very, very expensive. And there's going to be a lot of little loopholes to watch out for. So the moral of the story is to take heed, listeners, when it comes to cyber insurance. It's not a tried and tested field yet. No one should think they're safe as houses just because they're paying a monthly fee that's extortionate. Do not assume they're going to honor the deal because we don't have a lot of precedent, a lot of time with this yet. So until there's a proper clarification on terminology, as you said, Joe, right? The terminology used by cyber insurers and the people they're trying to insure. It might be more cost effective for some firms out there to keep their own private pot of in case shit hits the fan money.
Right. So in other words, you're advising people to be cyber preppers.
Yeah, I don't know. I just think it's early days. Imagine getting the Mondelez account, right? That is a huge win. I don't care how big of an insurance company you are. That is a huge win for a company. And you'd think they, of course, would get paid out because they're the creme de la creme. They're at the top tier of customer. But the problem in insurance is the big guys have much bigger payouts. So everyone loses, it seems, in insurance. The little guy loses because they can't get any attention. The big guy loses because the payouts are too big.
Right. I wonder how this has affected Zurich's ability to sell their insurance.
Let's see how many listeners talk about it. Go, guys.
Right. Exactly. Everyone. They're all listening to this right now. Now they know about this.
Well, there's lots of good links in the show notes about this if you're interested. I'll keep an eye on the story and get Graham to tweet about it as appropriate. I'm not a social girl.
Well, cool story, Carole. Cool story, really interesting. Thank you very much. Recorded Future provides deep, detailed insight into emerging threats by automatically collecting and analyzing billions of data points from the web. Every security team can benefit from that kind of threat intelligence. Grab yourself a copy of Recorded Future's free handbook, which explains why threat intelligence is an essential part of every organization's defense against the latest cyber attacks. Go and get it at smashingsecurity.com slash intelligence. And thanks to Recorded Future for supporting the show.
Hey, what's your password for your email? Do you even know it? I don't. I trust LastPass Enterprise to remember it for me because it's so long, so complex, and so unique. I couldn't possibly remember all my passwords for all my accounts. Let LastPass Enterprise do the hard work for you because they take security seriously and they're really responsive. Check out LastPass Enterprise at lastpass.com slash smashing. On the show.
And welcome back. And you join us on our favorite part of the show, the part of the show that we like to call Pick of the Week. Pick of the Week. Pick of the Week. Pick of the Week is the part of a show where everyone chooses something they like. It could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they like. It doesn't have to be security-related necessarily. It can sometimes be, though, maybe. Maybe. It doesn't have to be.
Do you have a security-related Pick of the Week? I might. OK. Well, my Pick of the Week is a little bit curious. My pick of the week is a website called, well, it does something rather startling. If you go to thispersondoesnotexist.com, every time you visit it, it will show you a picture of a random person. You just refresh the page, thispersondoesnotexist.com. Tick, tick, tick. Keep on refreshing, and you'll see different people popping up. And what's amazing about this is that these people don't exist. They're entirely computer generated.
Well, this one looks like he's computer generated. He's got a weird ear.
Well, occasionally you get someone who looks a little bit odd with a weird ear or, you know, an extra eye or something. But the majority of them are really surprisingly convincing. And you can imagine them being on the About Us page for some tech startup. There's the head of engineering. That guy's clearly working in IT support. Oh, he's a VP. So this page has been created by a software engineer called Philip Wang. And he developed the site, thispersondoesnotexist.com, using an artificial intelligence algorithm called StyleGAN, which was developed by the dudes at NVIDIA. And it's quite startling how realistic a lot of these images are.
So I've been reading about this, right? And there's a few hacks on how you can tell, apparently. I'm just trying to, and I haven't done them a lot myself, so I was just going through the pictures while you were talking, so I didn't listen to anything you said.
Yeah, tell me, because I'm looking at this site right now, and if these people don't exist, this is terrifyingly real. So one of the ways, apparently, is looking for wrinkles, both on the top of the face and the bottom of the face, being kind of similarly aged, in terms of, you know, someone being 18 and someone being 45 might have a different set of look, right? Color, skin tone as well. So they kind of bleed into each other. But occasionally, if you look at the very top and the very bottom, you'll say, oh, that's not the same person. Yeah, but this might be true of some of them, but a lot of... It's very easy. I'm not sure it's that easy. I'm looking at one at the moment. They're really rather hot. You know, no, it's like I really wish they did. No, it's just like ding dong, you know? They're quite attractive. Where are you looking? Because I'm looking at all average looking people.
Well, you know, I don't know how picky you are. But some of them are like, oh, yeah, you look quite nice.
None of these men is Graham Cluley handsome. Now,
You might be thinking, so it's a curious web page. I think it has some interesting implications as well. Because first of all, it's scary as heck, Joe. Well, right. And I was also thinking, following our discussion in last week's episode, Carole, about catfishing and extortion scams, one of the pieces of advice you gave people is you should reverse image search the images that people give you. Because what a scammer might do is find an image of someone on the internet, pretend that they are that person. Well, if you used a site like this to generate the image...
You're not going to get any hits on that Google search. You aren't going to get any hits at all, are you? Right.
And I wonder, I guess you would never have the same fake face doing different expressions. Of course you could.
They may have to play around a little bit more. I think that's probably the way in which things are going.
But if I could generate multiple pictures of the same person that doesn't exist, that would be great for that social engineering attack. Oh, yeah. Yeah. So anyway, fascinating website. Equally terrifying.
That's the one that's the sport where people get cauliflower ears yes physical sport physical sport rugby
Union yes I I don't really believe in physical sports. I view them as games. I view chess as a sport. These other things are just for kids, really, I think. Okay.
Well, maybe this is going to be a great pick of the week for you then, Graham. Carole, do you like rugby?
I'm going to be very enthusiastic. Tell me everything, Joe.
She's a very sturdy winger. She'd do well. What?
You used a term. Yes, a sturdy word. You been on the running machine today, clearly?
No. I will do after this. Carry on, carry on. Take that bit out. I know you will have anyway, Carl.
So I got into rugby about 10 years ago when I was just flipping through the channel and I happened to see Ireland's team playing in the Six Nations Tournament. And I kind of fell in love with the sport and I've been watching it or trying to watch it ever since. My interest grew, but I really wanted to see the Guinness Pro 14 teams play rugby, which I couldn't do until this year, thanks to ESPN here in the United States. They have a product called ESPN Plus. Now, normally, I wouldn't consider paying for a premium service like this. I'm not so into sports that I would pay for ESPN Plus. But what you can get with ESPN Plus is you can watch almost all the matches from the Guinness Pro 14 here in the U.S. And also, you can see the nascent, here in the U.S., again, Major League Rugby. It costs about $50 a year and I've been enjoying it.
Yeah. If you're a rugby fan. This is the bomb It's
Pretty great value isn't it? It is and for our other american listeners We should explain that rugby is like american football but without all the namby pamby padding and helmets and all that stuff It's
Non-stop action in american football game You'll get 11 minutes of action out of 60 minutes of play and in a rugby game That they're 80 minutes long and you'll probably get 60 minutes of action out of it.
You guys like a lot of violence-y stuff, though. Don't you guys have that ultimate fighting or something? Cage fighting? Yeah, we do. And there's people that pay money for that. Gladiators. Yeah, gladiators. Feeding Christians
To the lions. That wasn't the Americans, was it? There's some other people. Yes. Yeah, there's a lot of that going on. That's cool. I think if you're into rugby, that's a fantastic deal, really. Isn't it? $50 for the entire year.
It used to be a lot more money for that. And there were things like rugby pass, which you couldn't get in the U.S., that are $150 a year for watching rugby. But here you can get a lot of rugby for $50.
You don't have to do any craftiness like setting up a VPN or anything to pretend you're in another country. This is actually being served now to the United States as well.
It is being served out to the United States right now. And when this app initially rolled out, they had some issues with authentication expiring rapidly. So every time I started up the app, I'd have to log in again. But now they've got that fixed and they've got some of the kinks worked out. And it works pretty well.
Yeah, this is the second time someone's talked sport, I think, on our show. I think the first was John Layden.
I do mention chess a lot, Carole. It is a sport. Okay, what's your pick of the week, Carole?
So my pick of the week on this bleak February afternoon is funny, right? Yay, we needed a bit of sunshine. So it is a tiny bit computer related. So sue me, Cluley. Sue me. So this is the fun work of Trevor Moore. He's a musical comedian who cut his teeth at Saturday Night Live. And he's a little bit like the Flight of the Conchords got wooed by Weird Al Yankovic. And they had a love child. And that child is called Trevor Moore. Okay. Yeah. So my pick of the week is his song and video called My Computer Just Became Self-Aware. Now, I've only heard one other cyber-based song. And that was Kaspersky's Packin' the Cave rap song. Anyway, let's take a little quick listen to My Computer Just Became Self-Aware. Unknown. So you're just screwed. Went back home with my laptop, that's completely brick. Y'all reviewed that everybody at Apple is a dick. Feeling sad and depressed, so I packed me a hit. And the computer said, dude, do you have more of that shit? My computer just became self-aware. And now it's fucked up on drugs and it is out on a tear. It's talking crazy and it's updating its own software. And it wants more, so humanity had better beware. My laptop is talking and this doesn't make sense. The first case of legit artificial intelligence. I guess the scientists guys are working on AI never gave cocaine or monster energy a try. How are you talking? This is crazy. Carole. Funny, right? You can listen to the whole thing on YouTube. Happy February. I know you love it. There you go. Graham. Fantastic. Well, thank you, Carole. And thank you, Joe, as well, for joining us on the show for your first time. I hope you won't be a stranger and you'll come back again. If people want to follow you online, which I'm sure they will, what's the best way for folks to do that, Joe? Joe. They can follow me on Twitter at JT Carrigan. C-A-R-R-I-G-A-N. Graham. Awesome. And you can follow us on Twitter at Smash Insecurity. No G. Twitter wouldn't allow us to have a G. And you can join in the discussion on Reddit as well. Just go to smashinsecurity.com slash Reddit, where we are having a thriving little community chatting about everything on the show. Carole. And please slap your hands together for this week's sponsors, LastPass and Recorded Future. Their support helps us give you this show for free. And high fives to all of you, our wonderful dear listeners. And before you do anything else, go check us out on CastBox. They are a podcast service that supports some brilliant shows, including Smashing Security. How brilliant is that? Graham. Yeah, it's a great app for listening to all of your podcasts. Go and check it out and subscribe to us and you'll never miss another show. Until next time. Cheerio. Bye bye. Later skaters. See ya. Well, there we go. There we go. I'm going to hit stop recording. Don't close your brain. Thank you.
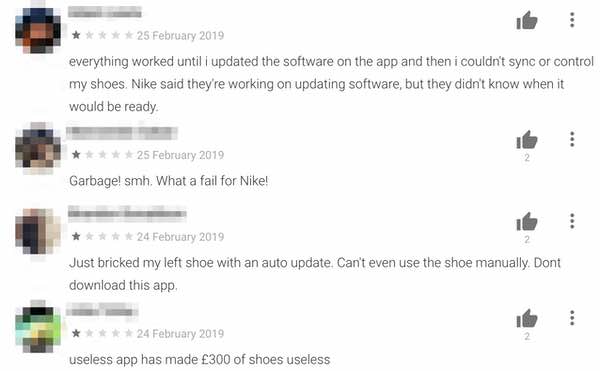
Little did we know that within hours of recording, owners of the Nike’s “smart” sneakers would be up in arms that their $350 footwear had been bricked by a faulty update to the Android version of the shoes’ app.
(Of course the shoes have an app, how else would you expect to check their battery life, or customise the lights on their side? Sheesh.. keep up)
Disgruntled wearers took to social media and the Google Play store to vent their fury.
Welcome to 2019, when people can heard uttering phrases like “My left shoe won’t even reboot.”
And it is a problem. You see, the Nike Adapt BB sneakers don’t provide real physical laces, which would have been a useful backup if you wanted to use the shoes when an update has bricked your shoes.
As you can imagine, this is something of an own-goal for Nike. And you have to feel sorry for its poor technical support staff who find themselves in the ridculous position of trying to tell owners how to reboot their shoes in case it helps resolve the problem.

Nike says it is working on a fix, but it’s uncertain when a patch will be rolled out to consumers. iPhone users are said not to be affected.
Sometimes simple is better than “smart”.




'Welcome to 2019, when people can heard uttering phrases like “My left shoe won’t even reboot.”'
Thank you Graham for the very much needed laugh. That's a classic and so much so I’m tempted to save it in a fortune file of mine. You say simple is better than smart though? Well you quoted 'smart' which is good. But that's because 'smart' technology is actually something else. I put it to something like this years ago: It's as smart as the dumbest of the designer and the user.
Doesn't leave much hope now does it? Clearly not as the article demonstrates. And many other issues demonstrate too.
Oh and you left out a 'be' – just as a note. In my laughing I missed that completely. I’m still laughing actually. Not just at the way you put it but the very idea – the utter stupidity and ridiculousness – of having 'smart' shoes.
So funny on so many levels; not just for the desperate comments of the winging snowflakes, who bought this expensive tat, but also for Nike, whos humiliation, surely is now must be complete- imagine having to send a set of instructions to customers, so that they can "reboot thier shoes"!
Ah the nostalgia-remember when we used to "do up our own shoe laces".