Nick Griffin, for those of you who aren’t aware, is the leader of the extremely right-wing British National Party (BNP).
As you can imagine, he has his fair share of enemies.
Including, it seems, hackers who are interested in breaking into the Twitter account of the notorious MEP.
Not only has a hacker changed Nick Griffin’s Twitter profile to suggest he is a leading light in other organisations not traditionally supported by the BNP:

This is the official twitter page of British Gay Orgy Party Chairman and Member of the European LGBT Community for the North West region, Nick Griffin.
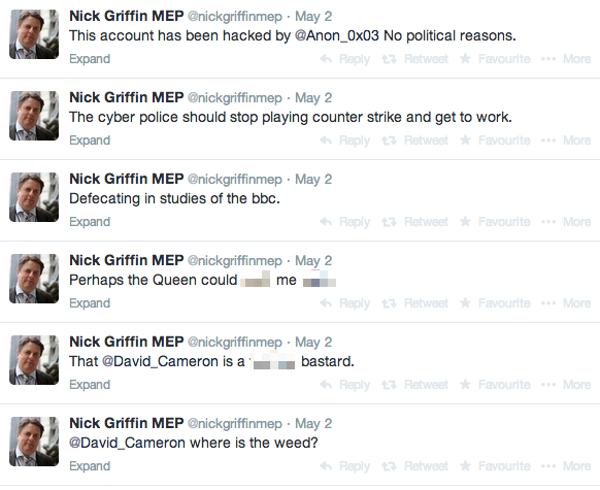
The attacker has also posted a series of tweets over the long British holiday weekend which – depending on your political viewpoint – you may consider either more or less offensive than Nick Griffin’s normal pronouncements.
According to a conversation on Twitter between the hacked account and a bemused follower, Nick Griffin’s mistake was to use the same password in multiple places.
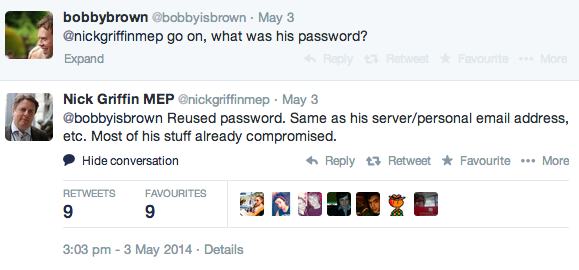
As I’ve explained many times before, you should never re-use passwords.
If you do, you could suffer the same fate as Nick Griffin – with multiple accounts compromised and your personal information and communications rifled through by unauthorised parties.
Passwords should be unique, hard to crack and impossible to guess. The smart approach is to use password management software like Bitwarden, 1Password, and KeePass to make them both safer and easier to remember.
A hacker calling themselves Anon_0x03 has claimed responsibility for the defacement, and at the time of writing, appears to still be in control of Nick Griffin’s Twitter account.
Update: Softpedia reports that the Twitter account of Griffin’s party, the BNP, has also been hacked. Same password? Frankly, you’d be bold to bet against that.

How terrible.
Re:"The smart approach is to use password management software like LastPass, 1Password, and KeePass to make them both safer and easier to remember."
There are however times where this does not necessarily apply. I can think of a few examples off the top of my head (or somewhere in the middle or bottom if you prefer):
1. If you don't like webmail (which I personally hate webmail) then your mail client could theoretically act as a password manager (but then if your user account has no password – bad – or a weak password or it is broken, then you do have a problem. However: that's what other things are for including volume encryption, boot passwords, keeping your belongings safe [more difficult with mobile type devices I guess], others…). This way also allows for not needing to remember long passwords albeit a bit less secure than having the login password (and user even), a master password but security always has that problem with how much inconvenience is too inconvenient or too convenient even.
2. I digitally sign packages that I maintain (for a redhat package manager – rpm – repository) and not only do I use more like pass phrases (that are quite long and that does include non alphanumerical characters) which indeed could be maintained through password managers, there's the tiny issue that this is done at the command prompt and there isn't always the option of this and certainly not having it enter the password itself (especially when no GUI around, like several of the machines I maintain – unless keepass has a command line version.. but even then there's potential pitfalls).
3. This wasn't one of the original thoughts I had but indeed: boot passwords would not apply here.
4. Similar to digitally signing packages is passphrases and indeed passwords for ssh (keys and also account passwords as well as switching between users, through the command prompt) or simply logging in with a password (which is less secure than requiring a key as well) or even (as already stated) switching users (temporarily). These two – both logging into remote systems at the command prompt – and authentication at the command prompt in general, actually – and digitally signing keys – are times when it is might not only be less practical, it might be impossible (and I don't see command line versions of password managers much better; in some ways it might be OK and in some ways not).
My other issue (though there might be ways around this.. not actually checked as the above are actually what mostly applies to me, especially 2 and 4) is the password being in the clip board (and whether or not – again, referring to keepass as that's the open source version = the version I would use – it can manage all types of automatically typing the password in for you [referring to different interfaces including APIs for logging in, authentication, etc.). That is itself a potential attack opportunity (but then again in that case you would probably make the wisest decision of if they are able to monitor that they are likely either key logging or sniffing [or both] anyway). Still, even while it is typing I would argue it has to be under heavy scrutiny as it does so.
Regardless, there are times where password managers aren't necessarily the best or most appropriate way. I would mostly agree that they are definitely a good thing but they are not fool proof (what is ?) either. Indeed, security is and always has been a multi-layered thing (sort of like networking is). Example: securid cards or other two factor authentication (or if you want to get really technical: have a dmz – note to normal users: referring to the security dmz, not the home router definition [which is a misuse of the term] – a bastion host and multiple subnets, perhaps physically separated [switch, etc.] where you have to log in to one machine to actually even get the chance to log in to another and those machines will have limited access between the others and the Internet as a whole).
One other pitfall is a rather unfortnate one: systems not allowing non-alphanumerical characters in their passwords. I have a list of hosts that have this problem and it's getting to the point where I'm seriously considering shaming them into fixing their terrible decisions (yahoo, I'm especially looking at you), and I mean by writing it on one of my websites for all to see (still have to decide on it though as unfortunately there is potential gain but also potential risks involved… guess I would have to try insisting they fix it first although I seriously doubt they will listen).