Now available to Netflix members: a new phishing scheme that tries to steal their credit card details and other personal information.
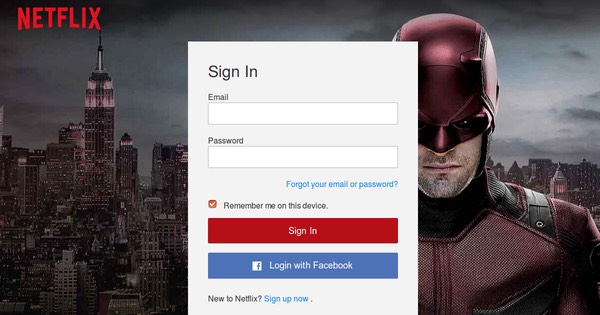
As security firm FireEye explains, the attack campaign begins when a Netflix subscriber receives a notification asking them to update their membership. The notification includes a link that takes them to a fake Netflix login page.
Upon “signing in,” a new page pops up and asks the member to validate several pieces of personal information including their name, date of birth, and place of residence.

The scam then asks the user to enter in their Social Security Number and payment card details.

Once the user has submitted all of their credentials, the campaign will direct them back to the real Netflix homepage.
Nothing groundbreaking in the realm of phishing, to be sure. But there’s more to this scam than meets the eye.
What makes this campaign interesting is some of the techniques it uses to avoid detection.
For starters, all of the phishing pages were at one time hosted on legitimate – albeit compromised – web servers. Those webpages also don’t display to users from certain IP addresses if its DNS resolved to companies such as Google or PhishTank.
As of this writing, the phishing pages are no longer accessible.
The phishing campaign also keeps one more ace up its sleeve to avoid detection. FireEye’s Mohammed Mohsin Dalla explains in a blog post:
“One technique is the use of AES encryption to encode the content presented at the client’s side…. The purpose of using this technique is code obfuscation, which helps to evade text-based detection. By obfuscating the webpage, attackers try to deceive text-based classifiers and prevent them from inspecting webpage content. This technique employs two files, a PHP and a JavaScript file that have functions to encrypt and decrypt input strings. The PHP file is used to encrypt the webpages at the server side…. At the client side, the encrypted content is decoded using a defined function in the JavaScript file….”
Every bit of information stolen from a user is sent to the attackers via the PHP mail utility, which means the bad actors can host the phishing pages on multiple websites and receive stolen credentials from a single email account.
Netflix, which instituted a password reset in June 2016 following several of the year’s mega-breaches, recommends users learn how to protect themselves by visiting https://www.netflix.com/security, where they will be reminded that Netflix never asks for personal information via email.
Users should also make sure they brush up on their anti-phishing techniques by remembering to not click on suspicious links or email attachments.



So the underlying lesson probably should be something like:
"Do not ever click on a link in an email message. If you do that, do not enter personal data in the web page that it links."