Late last week, Cloudflare reported on an interesting DDoS attack that had hit one of its customers.
The nature of the Javascript-based DDoS attack, which has moved away from being purely theoretical in recent months, saw a flood of browser-based traffic peak at a whopping 275,000 http requests per second.
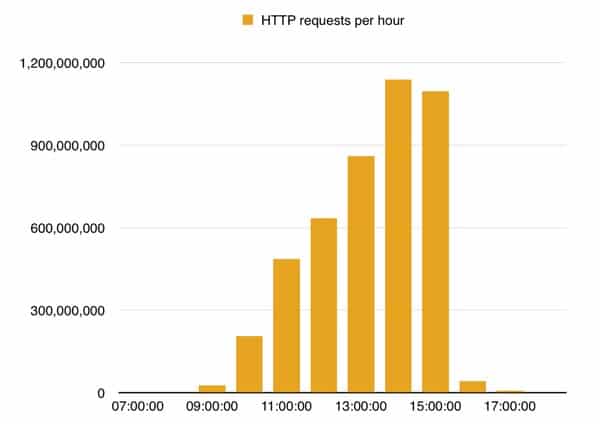
Cloudflare reported that the attack peaked at approximately 1400 UTC, and that during the day it received 4.5 billion requests against the targeted domain, issued by 650,000 unique IP addresses.
99.8% of the browsers attempting to visit the bombarded page originated inside China.
The attacks are suspected of taking advantage of online advertising networks that use real-time bidding deliver the malicious code, explains Cloudflare in its report:
To recap, we think this had happened:
- A user was casually browsing the Internet or opened an app on the smartphone.
- The user was served an iframe with an advertisement.
- The advertisement content was requested from an ad network.
- The ad network forwarded the request to the third-party that won the ad auction.
- Either the third-party website was the “attack page”, or it forwarded the user to an “attack page”.
- The user was served an attack page containing a malicious JavaScript which launched a flood of XHR requests against CloudFlare servers.
A similar JavaScript-based attack is being blamed for the recent DDoS that targeted 8chan.
 Since China’s Great Cannon was uncovered in the DDoS assault on GitHub this past March, I have been warning about mobile apps like browsers, file explorers, and security apps being used in attacks like this.
Since China’s Great Cannon was uncovered in the DDoS assault on GitHub this past March, I have been warning about mobile apps like browsers, file explorers, and security apps being used in attacks like this.
Using Baidu analytics, the attackers could learn which apps and users to target.
Furthermore, Citizenlabs, who did the first comprehensive analysis of China’s Great Cannon, said that unique individual IP addresses could be targeted.
This latest attack looks once again like the work of Great Cannon, and likely a successful test at that. Expect more, bigger attacks of the same nature in the near future.
Now, if you have any apps by Chinese developers, I recommend that you explore if it uses Baidu analytics, and/or contains banner ads that are serving ads of Chinese origin. Because you could be the next victim. Regardless of where in the world you live, you could be vulnerable.
Read the reports and studies, and get some protection, such as a no-root firewall, and a browser with strong ad-blocking capability
Lastly,try to do without those free apps that serve ads. If you can’t make yourself take that step, then there are apps to help you, but which usually require a subscription, such as Disconnect.