 Researchers at FireEye say that they have uncovered evidence that the recently-announced Microsoft zero-day vulnerability is not just being used in targeted attacks, but also has been used in wider finanically-motivated malware campaigns.
Researchers at FireEye say that they have uncovered evidence that the recently-announced Microsoft zero-day vulnerability is not just being used in targeted attacks, but also has been used in wider finanically-motivated malware campaigns.
Yesterday, Microsoft announced a critical security vulnerability that was being exploited in targeted attacks – mostly against “companies based in the Middle East and South Asia”.
FireEye says that it has connected the attack with the “Operation Hangover” attacks against India, Pakistan and other countries uncovered earlier this year.
But what’s perhaps most interesting to regular computer users is that the CVE-2013-3906 zero-day vulnerability that can exist in TIFF images was also being used in attacks that spread versions of the sophisticated Citadel banking Trojan horse.
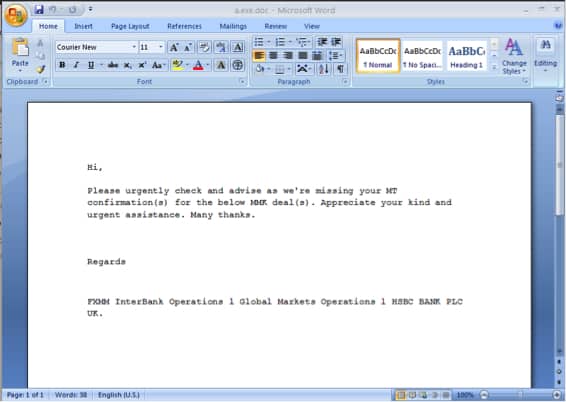
FireEye links these, more widespread, attacks to the Arx hacking group who typically spammed out malware-laden messages posing as “SWIFT Payment” emails.
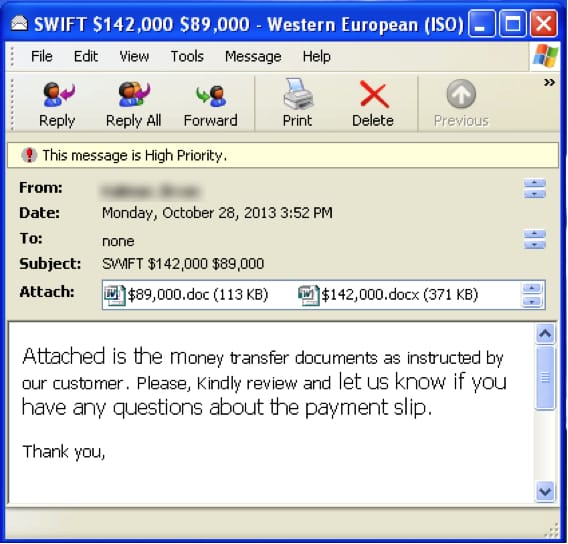
Opening the attached Word DOC files would cause your computer to install further malware, with the intention of spying upon your online banking and stealing your credentials.
This discovery underlines for all at-risk Microsoft users the importance of installing the temporary emergency fix-it tool. It’s not just big corporations and nation states who could be in risk of having their computers compromised by this security flaw.
Read more on the FireEye blog.


