 Patch Tuesday is upon us once again, meaning everyone with a computer running Microsoft software needs to sit up, listen and (if required) install essential patches to ensure the security of their systems.
Patch Tuesday is upon us once again, meaning everyone with a computer running Microsoft software needs to sit up, listen and (if required) install essential patches to ensure the security of their systems.
On this occasion Microsoft has released seven security bulletins, addressing over 30 vulnerabilities in Windows and other Microsoft software.
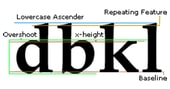
Some of the critical security holes addressed this time are to protect against how Windows, Internet Explorer and MS Office, handles TrueType font files. Potentially this vulnerability could be abused by malicious hackers who could embed boobytrapped fonts into files, and install a Trojan horse onto unprotected computers without the knowledge of users.
Another of the flaws patched by Microsoft involves a vulnerability discovered by Google security researcher Tavis Ormandy, and dubbed CVE-2013-3660. As I described earlier, Ormandy has been the subject of some controversy as – rather than wait until Microsoft had a fix ready – he published details of how the critical flaw could be exploited by hackers.

What makes matters worse is that Microsoft is saying that the CVE-2013-3660 zero day vulnerability detailed publicly by Ormandy is being exploited in the wild.
From their statement:
“This vulnerability has been publicly disclosed. Microsoft is aware of targeted attacks that attempt to exploit this vulnerability as an elevation of privilege vulnerability.”
Ormandy, for his part, has claimed that Microsoft “treats vulnerability researchers with great hostility” and that the company is “often very difficult to work with.”
You have to ask yourself if the public disclosure of this vulnerability before Microsoft was ready to protect against it was really to the benefit of internet users.
I’m not questioning Tavis Ormandy’s expertise at finding security holes, or his skills as a vulnerability researcher. There’s no doubt that he is extremely skilled in these departments. I just wish that Microsoft and Ormandy could find a way of working more reasonably with eachother so that vulnerabilities are only disclosed in a responsible fashion, once a patch is available.
Fortunately, Microsoft now *does* have a patch, but in my view Ormandy’s actions were irresponsible and put people at risk.
Whichever side of the fence you stand on, make sure to patch your Windows systems as soon as possible.
For a full breakdown of the security updates issued today, visit this page on Microsoft’s website. Microsoft security fixes are available from update.microsoft.com or available as downloads from Microsoft’s site.



Dude, taviso was working on that exploit /publicly/ for /months/ with no patch? #WTF
TavisO has a really bad attitude about this. It doesn't matter if he doesn't like the way Microsoft treats him, he's doing a disservice to the public by disclosing such vulnerabilities without even giving Microsoft some time to fix them. I can't have any respect for that.
Frankly, MS'es record is not so great WRT public interest…If you don't threaten them, they don't really care. So where's the trade-off between "responsible disclosure" and maldoing by disclosing ?
This month, the patch was out a month earlier than planned (and even the original date was set when MS had the "90 days to disclosure" at their minds.
It would be good for the community if some agreement was reached for these issue (when to disclose/how/to whom) and some "responsible party" that would decide when disclosure is ok. Such a body/organization, to be effective, has to include all the "big ones" (be it google, MS, cisco, oracle, and so on..).