British security intelligence service MI5 is so keen for internet companies to water down their encryption, that it has started the ball rolling with its very own website.
Let’s take a closer look at the padlock that shows up in your browser when you visit https://mi5.gov.uk.

Your connection to www.mi5.gov.uk is encrypted using an obsolete cipher suite.
The connection uses TLS 1.0.
The connection is encrypted using AES 256 CBC, with HMAC-SHA1 for message authentication and DHE RSA as the key exchange mechanism.
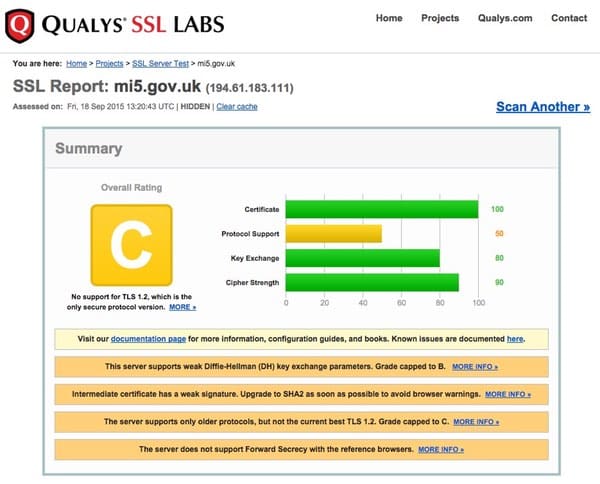
A quick check on the Qualys SSL test gives MI5’s site a disappointing C grade:
Perhaps not the most stellar result for MI5.
MI5’s C grade is brought about because they are only supporting the somewhat obsolete TLS 1.0 to encrypt communications between a user’s browser and the website. (TLS, you will remember, was the successor to SSL.)
TLS 1.0 isn’t held in high regard. For instance, earlier this year the PCI Security Standards Council recommended that firms securing payment card data should migrate from SSL 3.0 and TLS 1.0 as they are “no longer examples of strong cryptography or secure protocols” and switch to either TLS 1.1 (sadly, not all of its implementations are considered secure either) or TLS 1.2.
Of course, you’re not planning to enter your credit card details on the MI5 website. (Don’t they already have them? – Ed)
Chances are that MI5 supports TLS 1.0 to ensure that their website is accessible to as wide a number of internet users as possible. But, information security consultant Paul Moore told me, that’s no reason why MI5 could not also support TLS 1.1 and TLS 1.2 if it wanted to.
Taking that step would probably “fix” the MI5’s grade on the Qualys SSL test, and mean that British consumers and businesses wouldn’t have to listen to lessons on internet security from an organisation that only scraped a C grade.



I was thinking before the page opened, 'big surprise' but there was indeed a surprise: they are doing it deliberately. Scary. But at least they're not hypocritical here (I don't think that is a good thing, however in this case; but they shouldn't be encouraging weak encryption in the first place). That's the problem – weaker encryption is a really bad idea for everyone (including those they claim they are protecting). Reminds me of the NSA being hit by cipher weaknesses because of their encryption export restrictions. Yet these agencies like to refer to intelligence? What would they be like if they actually were intelligent?
"…and switch to either TLS 1.1 (sadly, not all of its implementations are considered secure either) or TLS 1.2."
The problem is that not all environments have TLS 1.2 in their repositories. You can manually compile, of course, but that that comes with making it harder to keep track of what is installed and what isn't (and other complications), as well as what is legit and what isn't (and where each component comes from) and verification is an important part of security! Of course, you might be using a compile-based distribution (for one example of others). This is unfortunate because TLSv1.2 is really the only sane choice (or perhaps that is: the currently sanest choice, given the history of SSL and TLS – implementations included).
"Of course, you're not planning to enter your credit card details on the MI5 website. (Don't they already have them? – Ed)"
Love that comment. Regardless of the truth to it, it is an amusing comment (and perhaps a stab at just how far spying agencies will go, in order to have as much power/control as possible).
Interesting that the MI5 website is hosted by QinetiQ (they boast their "secure" hosting https://www.qinetiq.com/services-products/cyber/Pages/secure-hosting.aspx), and their own certificate also uses the obsolete cipher.
There really is no excuse for purportedly "secure" sites to be using obsolete ciphers, or, even worse, out-of-date transportation layers. I have been watching a lot of DefCon stuff on youtube and the hacks they are coming up with really mean security needs to be beefed up to the maximum, wherever possible. I took 2 days to update my Apache and ciphers to the best. I now get an A rating at the Qualys SSL test page, and the latest Chrome reports me as "modern" with TLS 1.2. Mind you, even Qualys get it wrong, thanks to the use of Jive (a third party, granted) at https://community.qualys.com/message/31091
It's a shame MI5 isn't being a role model for excellence in security – it's not exactly difficult to get a good balance of secure and flexible – especially when there are excellent articles like these out there: –
Hardening Your Web Server’s SSL Ciphers (a truly excellent resource)
https://hynek.me/articles/hardening-your-web-servers-ssl-ciphers/
and to push your site from "A" to "A+"…
Enable HTTP Strict Transport Security in Apache & Nginx
http://opentodo.net/2012/10/enable-http-strict-transport-security-in-apache-nginx/
Worked for me https://www.ssllabs.com/ssltest/analyze.html?d=furrie.net ;)