
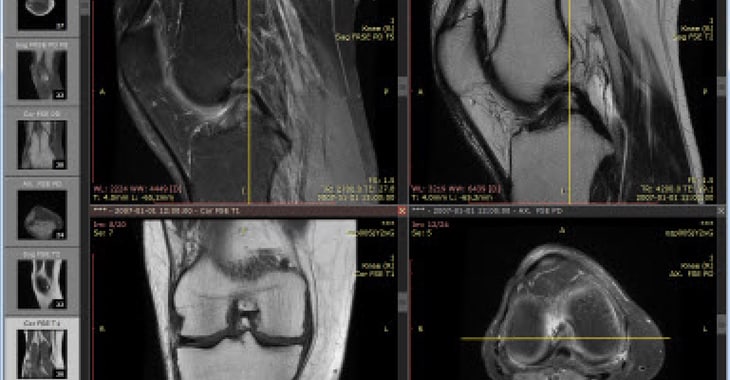
When we think about our data being leaked onto the internet, we often picture it as our financial records, our passwords, our names and addresses… but what about our private medical information?
Researchers at Greenbone Networks discovered that confidential images of X-rays, CT and MRI scans related to millions of patients has been left unprotected on hundreds of servers used by health providers worldwide.
Analysing 2,300 medical image archive systems around the world in the last two months, Greenbone’s team found 590 were freely accessible, containing records of 24.3 million patients in 52 different countries.
Exposed information included patients’ names, dates of birth, dates of examination, the attending physician, and some medical information about the purpose of the examination. In addition, 13.7 million of the compromised records included the social security numbers of American patients.
Attached to the exposed patient data were more than 737 million images, with approximately 400 million easily downloadable via the internet. In some cases the imaging servers even allowed the patient data to be downloaded via an unencrypted HTTP connection… D’oh!
Remember, Greenbone’s researchers did not have to exploit a software vulnerability or crack a password to access this treasure trove of medical data. All they had to do was visit publicly-accessible webpages, where no thought had seemingly been put into securing the details with even the simplest of passwords.
It’s clearly horrendous that names, dates of birth, and social security numbers have been spilled due to the sloppy lack of security in place at the imaging servers.
But the fact that the systems also exposed X-rays, CT and MRI scans, and other deeply personal health records, opens more opportunities for a criminal – including even to potentially blackmail individuals in the public eye who don’t want their medical issues shared with the world.


