Fifteen years ago, the (largely fictional) Weekly World News published a story about computer hackers.
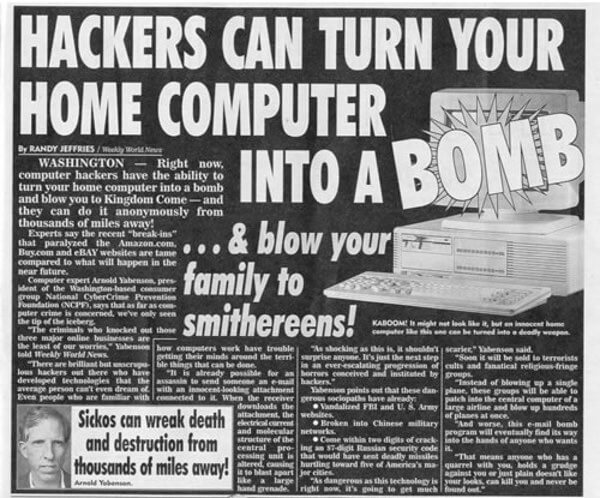
Hackers can turn your home computer into a bomb… and blow your family to smithereens!
Yes, quite.
Of course, no serious newspaper would ever resort to such ridiculous scaremongering.
In unrelated news, here is a report from today’s Daily Mail:

Are YOU at risk from Rombertik? Terrifying ‘suicide bomber’ malware can destroy your computer if it thinks you’ve detected it
My, how times have changed…
If you want to read something a little more thoughtful about the Rombertik malware threat, then check out the blog post from Cisco’s researchers, although it’s not perfect.
In that blog post you’ll find that Rombertik is hardly a “suicide bomber” and the chances of it activating its destructive payload on a regular user’s computer is minimal.
 The fact that it attempts to notice if it is being analysed by anti-virus researchers and their tools is not in itself unusual, but even then it doesn’t destroy your computer.
The fact that it attempts to notice if it is being analysed by anti-virus researchers and their tools is not in itself unusual, but even then it doesn’t destroy your computer.
What it does try to do, if it believes it is under analysis, is wipe out your hard drive’s partition sector (also known as the MBR or Master Boot Record) and force a restart. If it’s unable to do that it will attempt to encrypt the files in your home folder.
It’s unfortunate, I feel, that both Cisco researchers and the Daily Mail describe the malware’s behaviour as “destroying the computer”, when in fact we’re talking about data being wiped or overwritten on a hard drive.

Maybe some of the hype and hysteria would have been avoided if Cisco had been more careful with its words. And maybe it was unwise for the company to create an infographic which showed a hard drive catching fire.
Perhaps more people than I imagined have been reading back issues of the Weekly World News.
If you’re worried about the Rombertik malware threat, here’s my advice. It’s no different from the advice I would offer for reducing the chance of infection by virtually all malware:
Keep your anti-virus updated, make sure you are protected with the latest security patches, and be wary of opening unsolicited email attachments or clicking on unknown links. If you combine that with a layered defence you’re going a long way to reducing the threat.
There, if only real suicide bombing was as easy to prevent.



It's the Daily Mail – need we say more? Surprised they didn't claim it was Muslim immigrants too…
To be fair, for many (if not most) people, having their drive wiped or the data encrypted pretty much is having their computer destroyed.
Which system does it attack? Windows, OSX, Linux? It would be nice to know, because I am on Linux, and most of the times, I am not concerned.
If it was Linux or OS X it would be mentioned in the first paragraph else it's 'computer' malware …
BBC made me think it was Windows, which seems probable as it is the most widespread (hence most targeted platform). Of course, the BBC also suggests something that is factually incorrect: the MBR is not related to Windows or operating systems in general; the MBR is lower level than that[1]. Incidentally, while I don't know what method it uses, a lost MBR is not necessarily a lost disk as such. That is to say, depending on what it does, you can fairly easily recover. Of course, you probably could any way, if you're properly prepared[2]. That's another thing the BBC claims (and which makes me think it is Windows as the target): they say that to recover you have to reinstall Windows. Which to be strictly technical, isn't true (although all things considered, for most it would work this way). The main point here is this:
A lost partition table does not mean lost partitions, and therefore far less harmful. BUT even then, I'll point out that a lost partition (i.e deleted) does not mean you have necessarily lost the data! If you format it then you have more problems (depending on file system you might be able to recover some, and of course I'm not going to get in to encrypted volumes). Beyond most people's experience/knowledge, of course, and I do not know the mechanics of this malware, but wiping data isn't as as removing the partitions (or similar); that only 'hides' it.
[1] Which is why leaving a floppy disk in your computer before boot (or even before power goes off just long enough for computers without battery backup to go off and back on) could – assuming not bootable – write itself to your disks MBR, give you an error about there not being a bootable disk (or the disk selected not being bootable), and then when you DO boot up, the MBR/BS infecter is already resident (and consequently installed interrupt service routines etc., in order to manipulate I/O on disks.. as well as – if multipartite – files). Powering down won't help either because it would have written it to the hard drives already, to ensure it IS in control. Of course, MBR/BS viruses are far less prevalent these days but that's what happened (and of course there were other ways of infecting the MBR but this way was before the OS loads).
[2] Including backup. This really should be obvious but too many don't consider it. And yes, you can backup your partition table and the like. Of course you should be very careful when you do this, because a simple typo could cause you a lot of problems.
Rombertik runs on Windows.
I wonder if there's a parallel universe where the Daily Mail doesn't scaremonger it's readers…