Security researchers at Proofpoint have warned of the latest disguise being used to distribute the notorious Emotet malware.
Thousands of emails have been spammed out to organisations across the United States, using the subject line “Team Blue Take Action”.
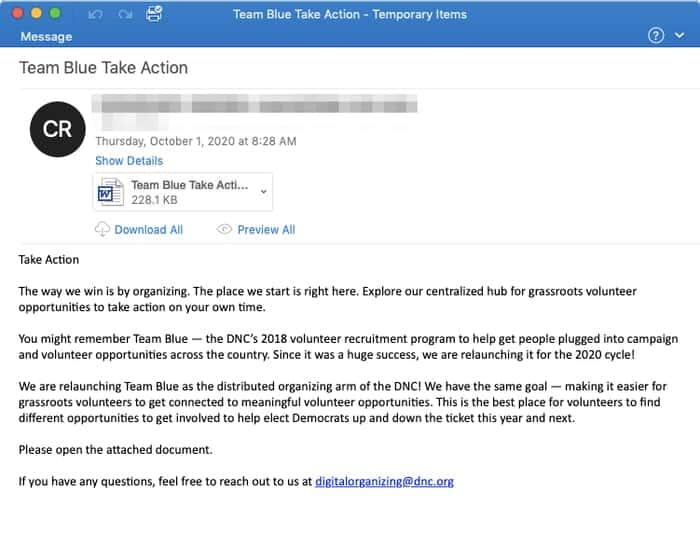
The message body of the email is harmless enough, in fact it’s lifted directly from a page on the Democratic National Committe’s own website:
Take Action
The way we win is by organizing. The place we start is right here. Explore our centralized hub for grassroots volunteer opportunities to take action on your own time.
You might remember Team Blue — the DNC’s 2018 volunteer recruitment program to help get people plugged into campaign and volunteer opportunities across the country. Since it was a huge success, we are relaunching it for the 2020 cycle!
We are relaunching Team Blue as the distributed organizing arm of the DNC! We have the same goal — making it easier for grassroots volunteers to get connected to meaningful volunteer opportunities. This is the best place for volunteers to find different opportunities to get involved to help elect Democrats up and down the ticket this year and next.
Please open the attached document.
The threat lies in the attached Word document. If the email’s recipient opens the Word document and enabled macros then malicious code within will download and install the Emotet malware, which goes on to download further malware onto infected PCs.
According to Proofpoint, additional subject lines seen in the email malware campaign include:
- Valanters 2020
- Detailed information
- List of works
- Volunteer
- Information
Filenames attached to the malicious emails include:
- Team Blue Take Action.doc
- List of works.doc
- Valanters 2020.doc
- Detailed information.doc
- Volunteer.doc
Keep your anti-virus software up-to-date and your PCs patched, always be wary of unsolicited email attachments, and never enable macros in a Word document unless you are absolutely convinced it is legitimate.
No doubt in the next few weeks we will see even more cybercriminals try to take advantage of the US Presidential election with different lures and tactics. Be on your guard.