
Researchers have uncovered malicious emails that are spoofing terror alerts from law enforcement agencies in order to trick users into downloading the Jsocket remote access trojan.
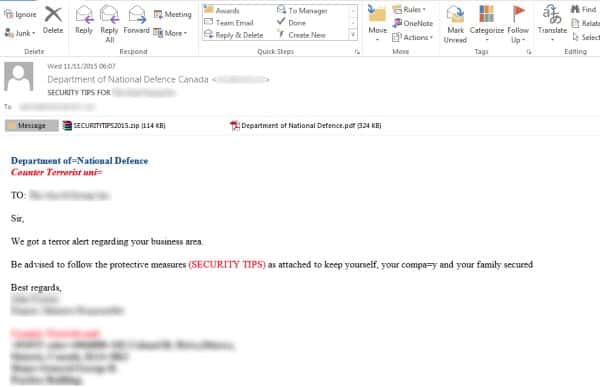
Lionel Payet, Threat Intelligence Officer at cyber security firm Symantec, recently published a blog post in which he explains how malicious emails spoofing the email addresses of United Arab Emirates (UAE) law enforcement agencies, particularly the Dubai Police Force, are deceiving users into executing malicious email attachments.
“The emails come with two attachments, one of which is a PDF file that is not actually malicious but acts as a decoy file,” writes Payet. “The malware resides in the other attachment, an archive .jar file. Further analysis of the malware confirms that the cybercriminals behind this campaign are using a multi-platform remote access Trojan (RAT) called Jsocket (detected as Backdoor.Sockrat).”
A new product from the creators of the AlienSpy RAT, which was discontinued earlier this year, Backdoor.Sockrat opens a backdoor that allows an attacker to download files onto infected computers.
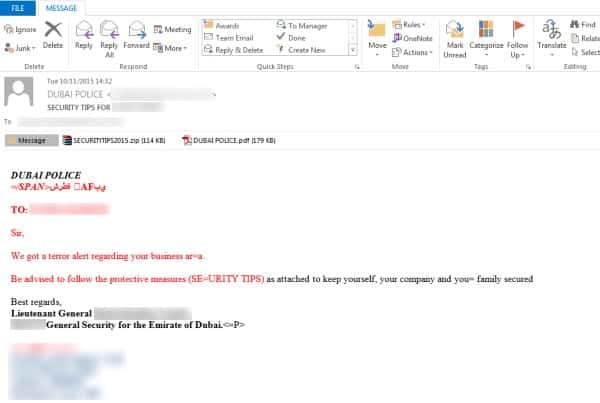
Part of the email reads as follows:
Sir,
We got a terror alert regarding your business area.
Be advised to follow the protective measures (SECURITY TIPS) as attached to keep yourself, your company and your family secured.
Attached to the emails is a PDF and another file called SECURITYTIPS2015.zip.
To enhance the legitimacy of their scams, as Infosecurity Magazine reports, the attackers sign the spoofed emails with the names of incumbent law enforcement officials. They also incorporate the name of an employee who works at the target company into the email’s subject line, indicating that they spend a fair amount of time researching their victims beforehand.
These spear-phishing campaigns are mainly based in the UAE. However, Symantec notes that it recently observed similar emails targeting companies in Bahrain, Turkey, and Canada. Those organizations have generally been based in the energy, defense, finance, government, marketing, and IT industry verticals.
When it comes down to it, spear-phishing emails are all about forcing a user to do something they otherwise would not do, which includes using fear and/or urgency to trick them into downloading a suspicious email attachment.
We all know this. As online users, it is our responsibility to expect these types of ploys and prepare for them. An updated security solution goes a long way towards protecting against Jsocket and other Trojans.
And when it comes to email security, suspicious attachments and links are better left untouched.
flickr photo shared by ell brown under a Creative Commons ( BY ) license



'The malware resides in the other attachment, an archive .jar file.'
There goes Java again …
As for attachments it is more like any attachment you don't expect and even then you should be careful because what if the sender (you requested the file from) doesn't realise it is malware ? Or what if some malware attaches another file and the recipient doesn't realise that it isn't related but is in fact malicious ? There are many scenarios but these alone should be enough to remind people that you should always be on your guard even when everything appears to be legit!
How original. malicious emails doing the rounds after a major event…
I envision that the likes of Gmail, Hotmail, etc… will one day reject all forms of attachments and only permit hyperlinks to files.
Sent you send an email, these links will be amended; to be interrogated by a service like Trustwave, validating that it's safe to retrieve.
This still doesn't mitigate against spammers using they own mail server to recipients of private domains…