170,000 users of a military dating website are believed to have had their account information exposed as the result of a hack by a group claiming to be the new incarnation of the notorious LulzSec gang.
170,000 users of a military dating website are believed to have had their account information exposed as the result of a hack by a group claiming to be the new incarnation of the notorious LulzSec gang.
The original LulzSec gang had its summer of hacktivism brought to a swift end last summer, after a number of its alleged members were arrested.
Of course, on the internet, anyone can claim to be whatever they want and so it’s not particularly surprising to see that it was a group calling itself LulzSec Reborn that posted a message on PasteBin announcing the hack of MilitarySingles.com.
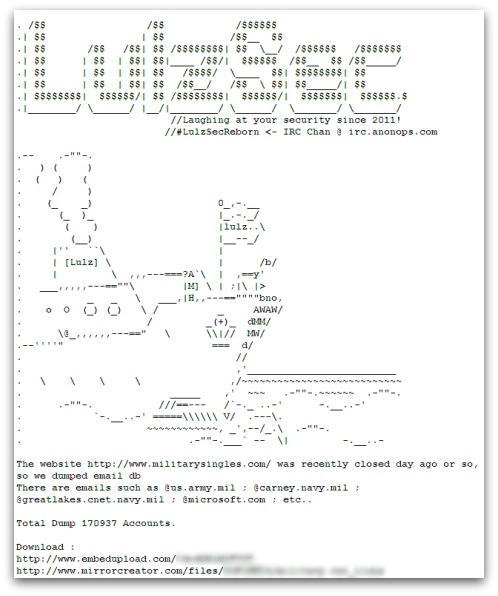
The website http://www.militarysingles.com/ was recently closed day ago or so, so we dumped email db
There are emails such as @us.army.mil ; @carney.navy.mil ; @greatlakes.cnet.navy.mil ; @microsoft.com ; etc..
Email addresses, usernames, real names and – in some cases – physical addresses belonging to romance-seeking members of the military were included in the haul of information posted on the internet.
If you know anyone who has ever used the Military Singles website, it would be a good idea to tell them to change their password as a precaution – and to ensure that they are not using the same password anywhere else.