Fans of Hollywood actress and doyen of the gossip columns, Lindsay Lohan, might have noticed that she’s been acting a little strangely recently. At least if they follow her antics on Twitter.
Last week, a topless photograph of the 22-year-old (with strategically positioned blonde hair extensions) was posted on the actress’s TwitPic account, and the link sent to her followers on Twitter. A message accompanying Lohan’s snapshot said that she was posting “OLD PHOTOS. [Because she was] THAT bored”.
Never quick to miss a publicity opportunity, the actress/singer/model made sure to tag celeb-watchers Ben Lyons and Perez Hilton in her post, to make sure that her picture caught their attention.
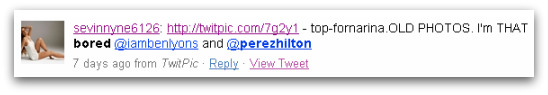
That picture is still posted on TwitPic so we can only assume that Lohan approved of its distribution – even though she later claimed that her younger sister published the semi-nude photograph as a joke.
Shortly afterwards, another photo was posted to Lohan’s Twitter stream, accompanied by the message “So dark- where’s JB cheater?”.
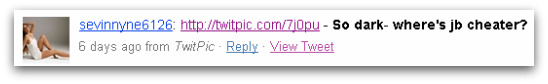
The picture allegedly demonstrated that singer Justin Timberlake was cheating on his girlfriend Jessica Biel by dancing with a mystery woman at a New York nightclub. Naturally the news that it was Lohan who was “outing” fellow A-list celebrity Timberlake as a philanderer had tabloid journalists frothing at the mouth.
Many will have assumed that as Lohan does regularly post photographs to her TwitPic account, which automatically get publicised to her Twitter followers, that this was just the latest example of her stirring up controversy online.
Lindsay Lohan, however, is adamant that she was not responsible for posting the photograph and that her Twitter account was hacked.
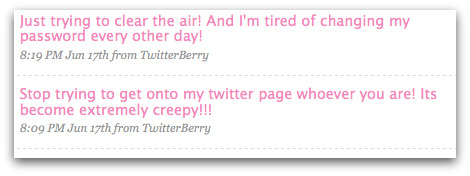
Although some may question exactly what would be the point of a hacker breaking into Lindsay Lohan’s account to cause trouble for Justin Timberlake (aren’t hackers more interested in spreading malware, or redirecting fans of popular celebrities like Lohan to spam websites?). the star of “Mean Girls”, “Freaky Friday” and “Herbie: Fully Loaded” is adamant that she did not post the photograph, and that her password must have been compromised.

“I would not discuss my personal life, let alone someone else’s, on the internet!”, the young actress told Life & Style magazine. “Clearly! Twitter needs to fix their s**t. I didn’t write ‘jb cheater!’ What does that even mean? It’s annoying.”
Without any evidence to the contrary I have to assume that Lindsay Lohan is telling the truth, and that her Twitter account was broken into. I’m going to take her at face value, and not surmise that maybe she invented the hacker excuse to cover-up a possibly embarrassing situation.
Clearly she would be sensible, however, to exercise more control over who posts to her fans online if she’s allowing others (such as her sister) to post photographs.
The more people who know your passwords, the more opportunity there is for your login data to leak out.
I’m also going to assume, though, that Justin Timberlake won’t be inviting Lohan to any parties anytime soon.
Oh, and one final thing. Lindsay Lohan is one of the high profile recipients of Twitter’s new “verified accounts” program. As I explained a couple of weeks ago on this blog, and has been proved by Lohan’s online troubles, such systems are not going to kill off Twitter fraudsters.