 The Anonymous attack on HBGary may have amused some who enjoyed the sight of a security firm left embarrassed and exposed, but it should send a shiver down the spine of any IT administrator responsible for securing their own company.
The Anonymous attack on HBGary may have amused some who enjoyed the sight of a security firm left embarrassed and exposed, but it should send a shiver down the spine of any IT administrator responsible for securing their own company.
Because can you honestly put your hand on your heart and say a hack like the one against HBGary couldn’t happen at your organisation too?
As Ars Technica explains, a weakness in a third-party CMS product used by HBGary’s website allowed Anonymous hackers to steal passwords that employees used to update the webpages.
Unfortunately they were passwords that weren’t encrypted strongly enough, and were possible to crack with a rainbow-table based attack. Amongst those exposed were CEO Aaron Barr and COO Ted Vera.
Worse still, it appears that Aaron Barr and Ted Vera were using the same passwords for their Twitter and LinkedIn accounts, and even for an account which administered the entire company’s email.
By exploiting software vulnerabilities, poor passwords and even some tried-and-trusted social engineering (see below) it was trivial for the hackers to steal the entire company’s email and deface its website.
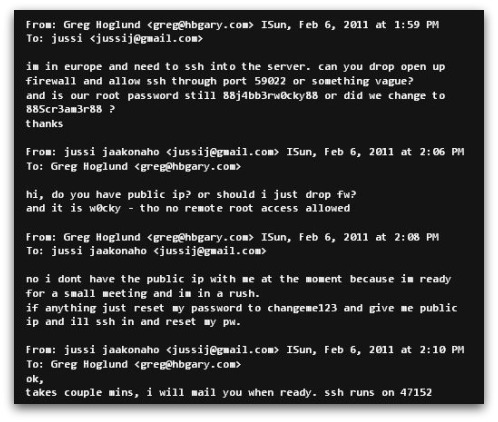
As Chet explained in an earlier article, an employee not seeking proper verification when a company executive apparently asks for help can result in a corporate disaster.
But more than that, it’s also essential that all staff learn about how to use passwords properly.
For instance, don’t use easy-to-crack or obvious passwords. If you do, you’re asking for trouble.
And it’s critical that different passwords are used for different accounts. That way if your password gets exposed in one place, there won’t be a domino effect as a series of other accounts are unlocked by criminals using the same credentials.
Unconvinced by the scale of the problem? Well, Sophos’s research has found that 33% of people use the same password on every single website.
In wake of the attack, HBGary withdrew from the RSA Conference taking place in San Francisco this week, and replaced their booth with a sign:

Read the in-depth piece by Ars Technica now, investigating how the HBGary hack occurred, and learn lessons which you can apply inside your own company. After all, you don’t want to be the next firm to have to put up a sign like that.
HBGary sign image credit: Colbinator on TwitPic.


