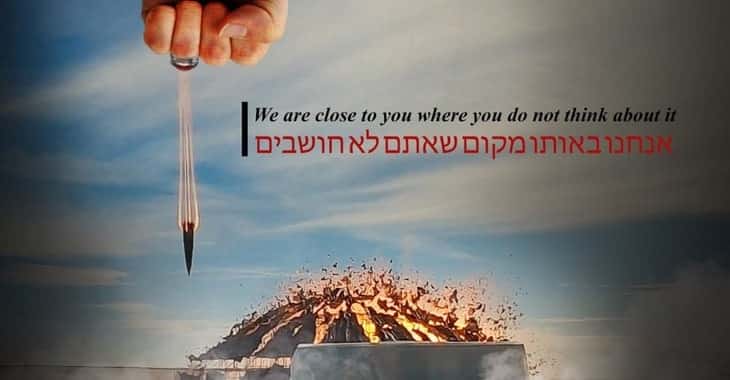
The Jerusalem Post says that its website was defaced yesterday, and pointed the blame at pro-Iranian hackers who they said posted an illustration depicting a ballistic missile being launched at an exploding nuclear facility in Dimona.
In the picture, a missile appears to be being fired from the clenched fist of a giant hand, wearing a ring.
A message in English and Hebrew accompanying the image said:
“We are close to you where you do not think about it”
The same image was at the same time posted on the compromised Twitter account of Maariv, one of Israel’s major Hebrew-language newspapers.

In the immediate aftermath of its defacement, the English-language Jerusalem Post invited readers to access its articles via its smartphone app instead.

Although no hacking group has claimed responsibility for the security breach, the newspaper noted it coincided with the second anniversary of the death of Iranian general Qassem Soleimani, killed by a US drone in Baghdad in January 2020.
According to reports, the ring worn by the first in the image bears a resemblance to a ring worn by Soleimani. Meanwhile, the picture of the exploding Dimona facility comes from a test missile strike by Iran against a model last week.
Of course, none of this represents proof that the hack originated in Iran, was endorsed by the powers-that-be in Iran, or was even undertaken by supportive hackers from outside Iran.
But it wouldn’t be a surprise if any of those possibilities were true.
Frustratingly, no information has been shared about how the hack might have taken place. Did the hackers hijack the website’s DNS settings and point visitors to a server under their own control? Did the hackers manage to use a compromised password to access the Jerusalem Post’s content management system?
Similarly, did Maariv have appropriate defences in place to defend its Twitter account?


