
The Intercept might have unwittingly helped unmask Reality Winner, a government contractor who allegedly leaked a NSA document about Russian hacking to the news outlet.
On 5 June, The Intercept published a “Top Secret” National Security Agency (NSA) document detailing Russian efforts to interfere in the 2016 U.S. presidential election.
“Provided anonymously to The Intercept and independently authenticated,” the report reveals that Russian military intelligence conducted a digital attack campaign against a U.S. voting software supplier and sent spear-phishing emails to 100 local election officials.
These actions appear to support the view that Russia meddled in the election beyond having hacked the Democratic National Committee, an incident which EVERYONE (We’re looking at you, Mr. President.) finally agrees involved Russian military activity.
Later that same day, the Justice Department published an “Affidavit in Support of Application for Arrest Warrant” against Reality Leigh Winner. A 25-year-old government contractor with Pluribus International Corporation, Winner was arrested by the FBI in early June on the suspicion that she “willfully retained and transmitted classified national defense information to a person not entitled to receive it in violation of 18 U.S.C. § 793(e).”
The affidavit doesn’t mention any names, but it’s clear it’s accusing Winner of having leaked the NSA report to The Intercept.
As FBI Special Agent Justin Garrick explains in the affidavit:
“On or about May 9, 2017, WINNER printed and improperly removed classified intelligence reporting, which contained classified national defense information and was dated on or about May 5, 2017 (the ‘intelligence reporting’) from an Intelligence Community Agency (the ‘U.S. Government Agency’) and unlawfully retained it. Approximately a few days later, WINNER then unlawfully transmitted the intelligence reporting to an online news outlet (the ‘News Outlet’).”
How did Winner get caught? Well, it looks like the “News Outlet” had something to do with it.
According to Garrick’s affidavit, The Intercept reached out to the NSA on 1 June 2017 about publishing the document in an upcoming story. As part of the correspondence that ensued, the news outlet sent the NSA the report. An analysis of the document revealed that some of the pages had been folded or creased, suggesting that someone had printed it and carried it out of a secure facility.
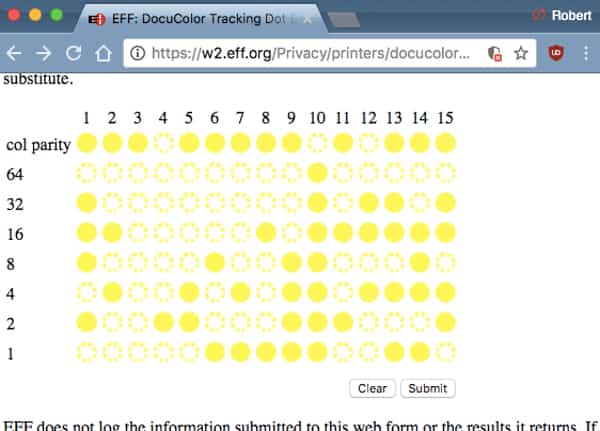
The NSA subsequently determined that six individuals had printed the document. How? The intelligence agency logs its print jobs. Most newer printers leave patterns of nearly invisible yellow dots on the documents they print, so it’s possible to trace something like a Top Secret report to a print job.
(For more information about how the NSA might have traced the leaked document, read security expert Robert Graham’s write-up here.)
An internal audit yielded evidence that Winner had communicated with The Intercept. Garrick subsequently spoke with Winner at her home on 3 June 2017 about the leak, at which point in the time the contractor admitted to having stolen the document knowing full well that “the contents of the reporting could be used to the injury of the United States and to the advantage of a foreign nation.”
It appears The Intercept did no one any favors in publishing the report and sending a copy of it to the NSA. On the one hand, it probably sought to protect Winner as its source. But the document did originate from the NSA, after all. It’s a bit short-sighted of the The Intercept’s staff (and Winner, of course!) to think the NSA doesn’t have means of tracking its Top Secret reports.
On the other hand, The Intercept might have thought it was serving the public interest by publishing the report. But government agencies like the NSA classify information for a reason (not always a good one, but a reason nonetheless). This fact doesn’t even include the myriad of investigations that are examining Russian interference in the 2016 presidential elections. A leak like this could very well have some bearing on the outcome of at least some of those investigations.
No one “won” from this leak. At a bare minimum, it caused lots of headaches in the intelligence community, and it may have changed the life of one young woman forever.
For more discussion on this case, check out this episode of the “Smashing Security” podcast:
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
It helps to secure businesses while making it simple for users to log into their favorite apps and services.
Iovation is offering Smashing Security listeners a free demo of its newest product, LaunchKey.
Visit demos.launchkey.com for your free demo, and thanks to Iovation for supporting the show.
Hello, Carole, how are you?
I think most people, if they knew how you spell Theriault, would be somewhat surprised.
And thank you for joining us, Iain. You're based in New York, is that right?
And I was interested in a story which I saw published on The Intercept.
And The Intercept, if you are aware, is a publication edited by, amongst others, Glenn Greenwald, who is Edward Snowden's buddy.
And they look like they'd got a real scoop on their hands because they had been leaked some documents from the NSA. Hmm, where we've heard that story before.
Although these documents were confirming that Russia had been doing some naughty hacking.
In fact, the information which was leaked from the NSA said that Russia had coordinated a cyberattack on at least one US voting software supplier in the days before last November's presidential elections, and also claimed that spear-phishing emails and booby-trapped Word documents had been sent to over 100 election officials.
Although—
You open the document and, exploiting a vulnerability or something.
If you use the right social engineering in the sort of frame of the email, as it were, you know, so the thing which encourages you to open it, either in terms of who has sent you the email or the words, you know, inviting you to open the attachment, you may well fall for it.
And this is a standard trick which we see criminals using all the time.
So the NSA think that Russia have been up to it and that the Russian state intelligence are behind these attacks.
Now, of course, this is pretty controversial stuff because there has been so much talk about Russia hacking.
And in fact, in the last week, Vladimir Putin has given an interview saying, it's not us in the Kremlin.
Instead, it is freelance patriotic hackers who have just taken it upon themselves to hack other countries.
So these documents have come out basically suggesting quite strongly, it's Russia who's been doing it. Okay, so that's the first half of the story.
And that's kind of interesting, you know, and obviously that's going to put a bee in someone's bonnet in the White House who doesn't want people to talk about Russia hacking, right?
They arrested a 25-year-old woman called—
Winner decided to call their child Reality.
She's been working at an NSA facility in Georgia since February.
And that apparently suggested it had been printed and then carried out of a secure place. Whoa, whoa, whoa.
If they had been emailed the actual document itself, they presumably would have printed out a new copy or done a nicer screen grab of it or something that.
But instead, they'd obviously got some sort of, at the very least, a PDF scan of a physical document.
And so the investigators, who are obviously jolly clever people, noticed that it's been folded and creased. And they said, well, why is it folded and creased?
So tut tut.
Furthermore, they looked at her PC and they found that she had been exchanging emails with The Intercept, with the website, which frankly is a bit of a goof, isn't it, to do that from your work computer.
But there's even more than that.
Security expert Robert Graham took a look at the pictures on The Intercept website of these documents, and he says that they contain clues which could have helped whoever was trying to stamp out the leaks.
So it's tiny little yellow dots on the white background. You can't see these really with the naked eye.
You wouldn't even notice it, but that contains little bits of metadata about where the document was printed, the serial number, when it was printed, and so forth, which is obviously sometimes very useful to law enforcement.
And in the case of the NSA, which is logging all the printing jobs sent to its printers, it can say, well, it was this printer. We can see the serial number. We can see the time.
We can work out who's actually printed this out.
It would complain if it was empty.
She has been on social media using hashtags hash NeverMyPresident and said rather rude things about that wall that he wants to build between the United States and Mexico.
But in this particular case, you can imagine, you know, there's a potential for the book to be thrown at her for a very long time. We've been joking about this.
And also, there's this serious question of why can't the NSA keep a secret.
I know it's a big step she took. I can't believe she was there for such a short time. It makes me think, and then she had access to such information. That's also very strange to me.
She's been there since February.
We'll come back to what a bucket is in a moment, containing data that appeared to be from some kind of private sector defense contractor. So a bucket is a great name.
So they'd forgotten to protect this data. So anyone who figured out what the bucket name was, presumably by guessing, although I don't know, could just download the files in it.
And there's some confusion about whether or not the files in this particular bucket were top secret or merely highly classified.
Anyway, the reason I like this story so much is that it's exactly the same sort of story as we were dealing with 20 years ago. Except 20 years ago, we didn't have the cloud.
We called it FTP servers. And people would upload things to FTP servers and then forget to protect the data.
And so any old random person on the internet could download things that you had left on your FTP server. Protecting that stuff then was pretty simple.
But right now, it's way more complicated with the cloud, because access control there is so much more complicated.
And because we're putting so much of our things in the cloud now, it's very easy for mistakes like this to get made.
Should it be that, you know, these places where these buckets are made in the cloud to shove all of your data, should they be forcing you to set passwords or at least have them enabled by default rather than, you know, having publicly accessible folders the default instead?
I mean—
And Amazon has one and Microsoft has one and Google has one, and all of these companies have these cloud storage services and they all have different ways to configure them and different defaults, and the access control can get very, very complicated.
So it's very easy for me to imagine that they made a mistake with one bucket or they made a mistake on one day with one person doing something silly.
And for data and for a story like this to explode into the headlines and to get lots of attention about, you know, sort of in this case, highly classified intelligence data being leaked out.
There's so much data in the cloud now and so many people are working for companies, all of whom have data in the cloud, that it's very difficult for these companies to kind of keep track of what's up there and who created it and whether the access controls are correct.
I was saying earlier, it's kind of if security was espresso, this is like the mochaccino jobbie with lots of froth. So we are going to talk about a celeb, sweary chef.
Who am I talking about? Gordon Ramsay, who today had reason to celebrate.
So, why would Ramsay jump with glee at the misfortune of a man who he once said about both of them that they were as alike as wings on a plane?
Well, to all tell me, I have to go back to 2008. So, turns out father-in-law is actually the CEO of Ramsay Holdings. And in 2008, they got into financial difficulty.
Of course, that was the time of the financial crisis, but also, there seemed to be quite a deep hole in the financial cash flow, and they were in trouble.
In fact, they were in such big trouble that Ramsay told the Sunday Times that he was forced to sell his Ferrari to help pay debts.
But they're fighting like cats and dogs, and eventually the father-in-law, his name is Chris Hutchinson, gets fired, and he doesn't go quietly, and it starts getting really ugly.
We're talking in the press, they're hiring detectives, they have IT specialists, they're suing each other, they're dragging their names through the dirt.
And there's a ton of accusations from Ramsay that the father-in-law is actually stealing money and hacking into his systems. So it turns out he did hack Ramsay's systems.
Publicist Phil Hall sold the private pics stolen from Ramsay's computer to the Daily Mail. Now these were private pics of Ramsay shark fishing. Do you remember this, Graham?
Just think, you're in the UK, you'd remember this. This was after he had publicly denounced the activity.
So he went around saying, and then there was pictures all with him, you know, shark fishing.
So basically Hutchinson, whose sons also worked in the firm, were today found guilty of unauthorized access to computer systems, and he got 6 months in the slammer. Sons each got 4.
And the details of how they hacked are all a bit vague, but apparently they were taking pictures and looking for financial information, all to use during all their suing and trying to get a case together to say, aha, here's some proof that he's done X or done Y.
They rifled through his emails on hundreds of occasions and were extracting information and photographs and giving them to the press and using them obviously to their advantage when they were in this dispute with Ramsay.
And I mean, you know, there is a bit of a thing about using spyware to steal the passwords, but you know, this is not a huge company and it could have just been that they tried to guess the password, or that Ramsay left his machine unlocked.
It could have been anything.
This guy was—he's been accused of using the ghost signing machine, you know, wherever I guess Ramsay ghost signs his books, to sign all kinds of legal documents without Ramsay's knowledge.
He's apparently transferred more than a €1 million to a French bank account, et cetera, et cetera, et cetera, et cetera, et cetera.
So yeah, this is very light on the security front, isn't it?
First of all, people should go away and listen to our podcast all about securing your webmail account and the various tips we gave you there about how to defend yourself.
But also, I think there's a fundamental thing here, which is it is not cool to hack into other people's webmail accounts, even if they are related to you.
Just because it might be easy to crack into someone else's email account and to have a snoop around, don't do it.
Because if they take a dislike to you or decide to proceed against you, you could end up in prison.
It's because he accessed the computer without authorization.
Doesn't have to be security related, could be some funny story, a book we've read.
I've been using it for a couple of years, and this is a tool which works alongside your file sharing Dropbox-like syncing service. So chances are—
But the one concern that I think all of us sometimes have, especially if we work in this industry, is we're shoving all of these files into the cloud effectively. And how well—
Okay, so we've got passwords and maybe we've got two-factor authentication in place as well, but are we preventing the services themselves from reading those documents?
And also, what would happen if someone did manage to get our credentials and log into those accounts and access potentially lots and lots of our files?
Well, Boxcryptor is a solution for exactly that, because what Boxcryptor does is it invisibly is running in the background, and every file which you put onto your local sharing folder, the thing which is being synced up with the web, all of those files are being encrypted.
And so you have end-to-end encryption.
And those files will then of course be synced in their encrypted form onto your other devices where you also have your Boxcryptor client, which is decoding them completely invisibly as well.
If you just want to use it with one sort of service, just if you only want to use it with Dropbox, if you want to use it with more, then you can pay a little bit of money and there's obviously sort of business versions of it as well.
But it's a great tool. There are other tools which do similar jobs out there.
I was traveling recently and whenever I travel I use a feature of Google Maps on my electric cellular telephone that it turns out many people don't seem to know exists, which is not surprising because until recently it was well hidden.
It's the fact that you can download maps, sections of the map, to be used offline.
And this is one of those tips that people who already know this are going, well, duh, obviously you can do that.
And then when you go to these countries where you may not have cellular telephone service, you can continue to use the maps just as if you did.
And I think modern versions of Google Maps apps, at least on Android, I don't know about iPhone, will automatically download your home area, so the area around where you— where it thinks you live.
I— it was late at night and I was trying to get home, and I was just— and there was no coverage, and that saved me.
So if you're going abroad for a while, you're going to want to make sure that your phone sees Wi-Fi every now and then so it can update the areas.
But it works very well, and I think it's great. And I don't know if Apple Maps has the same feature. I do not own one of those Apple telephones.
How big an area can you tell it to download offline?
But you can do that and it works and then it's just transparent.
Graham, didn't you once, because you used to, I have this vague memory of you dog walking around your place and there not being good coverage and downloading maps and loving that offline map experience.
No, that— and I've forgotten the name of the app which I was using, but basically, yes, it downloaded an entire map onto my phone, and I was able to get a GPS signal, but I wasn't able to get a data signal.
It's definitely worth mentioning that other programs also have the feature, like OpenStreetMap will, I think, let you do this as well.
And this is all about the challenges that translators have with how should I put this, you know, Trump's special turn of phrase, shall we put it.
So, Sue Ruta, professor of interpreting and translation studies at Tokyo University of Foreign Studies— God, that's a mouthful— was interviewed in the piece, and I just wanted to pull out a quote for this she said because it's so fascinating.
Because you have to think about it, how would you translate a lot of the things he says?
I tell my students that with simultaneous interpretation, the trick— because it's simultaneous, right?
Simultaneous interpretation— the trick is to anticipate the speaker's intention and tell a story, to be slightly ahead of the game.
But when the logic is not clear or a sentence is just left hanging in the air, we have a problem.
We try to grasp the concept and get to the core of the message, but in Trump's case, it's so incoherent. You're interpreting, and then suddenly the sentence stops making sense.
And we risk ending up sounding stupid.
So apparently they're now having to study instead of looking at dictionary words, they have to read all kinds of cultural idiomatic kind of probably Urban Dictionary to try and find the meaning of, you know, certain phrases that he uses.
I mean, I'm sure, you know, if he were here— unfortunately, I did contact him, he said he was a bit too busy to come on the show tonight— but I'm sure he would say he's simply smarter than these interpreters and they need to be a little bit brainier if they can't follow what he's saying.
I guess I know what you're saying, not many even people in English are understanding a lot of the arguments, but still, you know, it's a well, at least we have the—
But yes, you're right.
If he was going out and having discussions with, I don't know, the boss of Korea or something like that, or the Taiwanese president, or who knows what, the interpreter's job is really critical, isn't it?




Oh, please.
You think the American people would have EVER been told about the depth of Russian hacking (in collusion with the Trump team) without this leak?
What no one has the guts to acknowledge is that there will NEVER be impeachment articles drawn up, let alone even a DOJ indictment against anyone higher than Flynn (who will instantly be given a presidential pardon).
This is the tyranny of one-party rule – just like in Mother Russia. The US is well down the road of fascism, but just like the proverbial boiled frog, the complacent public won't realize until it is too late.
Gee, the unfounded accusations are still flying fast and furious. Can anyone offer one piece of evidence, just one, of "Collusion"? between the Trump campaign and Russia ??? No ?? That's because there is none. Only insinuations and speculation so far. No REAL proof. But the real fascist are the law breakers on the left, conveniently ignored by the MSM. Those who try and squelch free speech. And riot at the least cause to get attention, and destroy properties. Show where the right has ever, I mean ever, acted in such a fashion? You can't, but hypocrites be warned, you will get that police state if you keep it up. England will beat the US there, perhaps even before the EU.
"Trump is writing a new political play book (or perhaps revising an old one) that suggests it's better to lie large, often and unapologetically then ever admit you are wrong. One poll conducted earlier this year found that nearly two-thirds of Trump supporters believe Obama was born outside the United States" (Baltimore Sun, The (MD) 09/19/2016). It is disturbing that Trump's use of Hitler's play book of dishonesty, intolerance, hatred, and fear would work in the new millennium. Haven't we learned anything from history?
I really fell pity for this poor girl; she has been failed by everyone in her life who should have been, but were not, responsible adults. I blame her professors and deans in the colleges she attended who gave her "safe spaces" where she did not learn to hear and digest opposing ideas. I blame big media personalities like Reza Asslan and Kathy Giffin who taught her it's ok to use terms like Piece of S**t about, or symbolically decapitate those with whom you disagree. I blame Pluribus and the NSA for allowing someone to work at the NSA without even checking their social media output. I blame her mother who gave her child the name Reality but failed to instill in her enough sense of reality to realize that there are grave consequences for stealing top secret information from an intelligence agency of a global superpower. I pray the court shows her mercy. Though 25 years old, because of our failures, she's just a child who was handed a loaded gun.
If you want to play the blame game and beat yourself up about "our failures" be my guest, but don't include me. I failed no one. Reality sucks for Reality Winner, but she's not a victim. She's an adult who made choices and any trouble she's in is her own doing.
If you feel so strongly about it, then go to her trial and offer to take responsibility for her actions. If you're not willing to do that, then plaster a band-aid on your bleeding heart and move on……..
This woman was aware of the penalties for treason, she signed multiple documents over the course of her time in the Air Force, and upon taking the contracting job stating that she would protect the information she was being given access to. Instead she made a conscious decision to betray her country. I hope our legal system sends a strong message to this traitor.
Thankfully she was caught before she was able to cause serious damage to the national security. Someone as misguided and ignorant as she is, is highly susceptible to enemy influence and recruitment.
Nonsense. If anything, she worked to protect the country and expose Soviet meddling. If they arrest the whistleblower, democracy is at stake. The people like you who are trying to protect the fact that the Soviets meddled in our great country are either Soviet Bots or the treasonous traitors to America.