On 9 July, Iran’s railroad system came under attack from hackers.
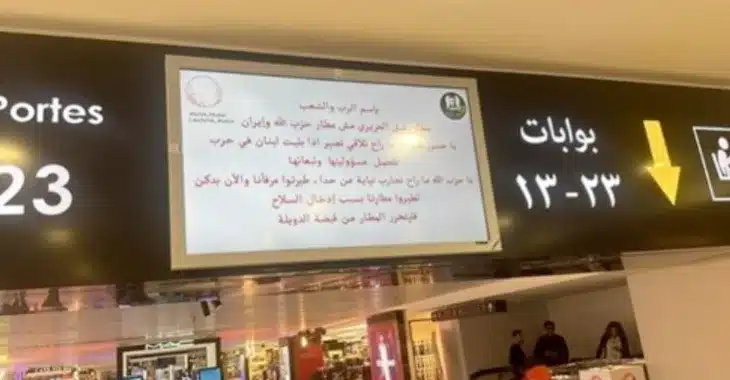
The attackers posted messages on station departure boards warning of “long delay[s] because of cyberattack”, and suggesting inconvenienced passengers call “64411” for more information.
64411 is reportedly the telephone number of the office of Ayatollah Ali Khamenei, Iran’s supreme leader.
A phone number–64411–was displayed on boards of train stations today in #Iran amid the reported cyberattack on the rail system. It directed commuters there to call for more information. It matched the number to #Iran's Supreme Leader's Office that is displayed on his website. pic.twitter.com/IQQ85I6QhJ
— Iran International English (@IranIntl_En) July 9, 2021
The following day, Iran’s transport ministry said that its computer systems and website had suffered “widespread disruption…probably due to a cyberattack.”

An analysis by experts at Sentinel One pointed the finger of blame towards MeteorExpress (also known as Meteor), a previously unseen type of wiper malware that wiped computer file systems and locked out users.
Inevitably, Iran wasn’t terribly pleased about having its systems attacked by the hackers, and there have been reports that a subsequent drone attack by Iran against an Israeli-operated oil tanker, which resulted in the death of two crew members, might have been launched in a tit-for-tat response to the cyber attack.
However, an investigation by security researchers at Check Point has concluded that the attack was the work of a hacking gang called Indra that works against the Tehran regime, rather than an attack sponsored by a nation state such as Israel.
Was it Israel? Was it Indra? Was it Indra working under the orders of Israel?
It’s hard to be certain.
But whoever was responsible for the attack on Iran’s train system which trolled the country’s supreme leader should probably consider that it’s no laughing matter, and that things could very quickly and seriously escalate.