More details have emerged regarding the cyber attack that has this week severely impacted operations at Norsk Hydro, one of the world’s largest producers of aluminium, and a major producer of hydroelectric power in Norway.
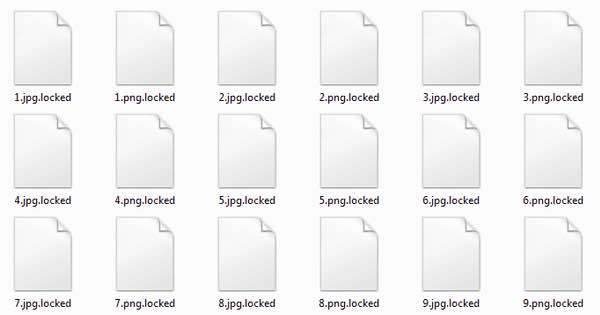
The company has confirmed that it was a victim of a ransomware attack, which saw computer files encrypted and their means of decryption withheld unless the extortionists receive payment in Bitcoin. Effectively, infected organisations are locked out of their data.
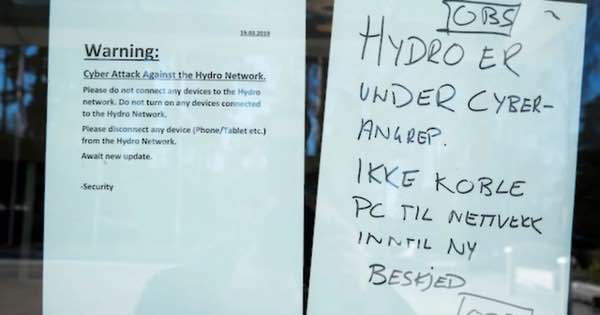
Hydro’s entire global network was taken down by the attack. The company’s US factories were amongst those affected, as well as smelting plants in Norway. However, other facilities – including the firm’s power plants – are functioning normally.
The Norwegian National Security Authority (NSM) has said that the relatively new LockerGoga ransomware was to blame for the incident. Norway’s National Cyber Security Center (NorCERT) is believed to have warned the country’s public agencies about the attack, in an attempt to prevent the further spread of the malware.
Unlike many other families of ransomware, LockerGoga appears to only be being used in a limited fashion, with specific organisations being targeted for attack. And for that reason it doesn’t have its own mechanism of spreading throughout an organisation.
That makes LockerGoga different from other hard-hitting ransomware such as Wannacry or NotPetya, which cared little about the organisations it infected. For LockerGoga to be successfully deployed inside a targeted organisation it needs to already have admin rights.
NorCERT has said that the ransomware attack was combined with an attack against the firm’s Active Directory, which may have been used to spread the LockerGoga ransomware throughout the organisation.
Security expert Kevin Beaumont has tweeted that the attack bears similarities to one which hit French engineering firm Altran Technologies earlier this year.
LockerGoga hit @Altran back in January. As an attacker – if you have domain admins, put the .exe in Netlogon folder, it automatically propagates to every Domain Controller, then make a GPO to run on each PC and server at top level. Most orgs firewall accept Active Directory.
— Kevin Beaumont (@GossiTheDog) March 19, 2019
You can’t help but get the feeling that this was a highly-organised extortion attempt against Hydro.
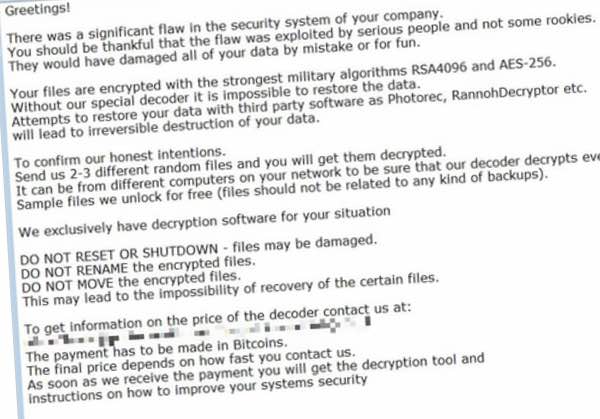
At a news conference, Hydro’s finance director Eivind Kallevik said that the company would not pay the extortionists:
“We have good back-up routines. Our main strategy is to reinstall data from the back-up systems.”
As we’ve discussed before, you don’t want to find yourself in the position of having to pay the criminals behind a ransomware attack.
Build your defences and segment your network to reduce the chances of an attack successfully entering your organisation, and ensure that you have a secure, working backups of your critical data so you can get back up and running as soon as possible if an incident does occur.
According to a Reuters report, Hydro is beginning to restart some of its operations today but says “it is still (too) early to estimate the exact operational and financial impact.”


