 British security researcher Scott Helme tried to book himself a night away from it all recently via HotelHippo.com – only to find an array of security issues that could have left him, and thousands of other customers, dangerously exposed.
British security researcher Scott Helme tried to book himself a night away from it all recently via HotelHippo.com – only to find an array of security issues that could have left him, and thousands of other customers, dangerously exposed.
The list of problems Scott found with the Hotel Hippo website are long and varied, and will likely leave you agog at the incompetence of a company which should be keeping customers’ sensitive information secured.
Here’s just one of the issues that Scott uncovered:
If you make a booking via the HotelHippo.com website, you are emailed a link to your booking confirmation.
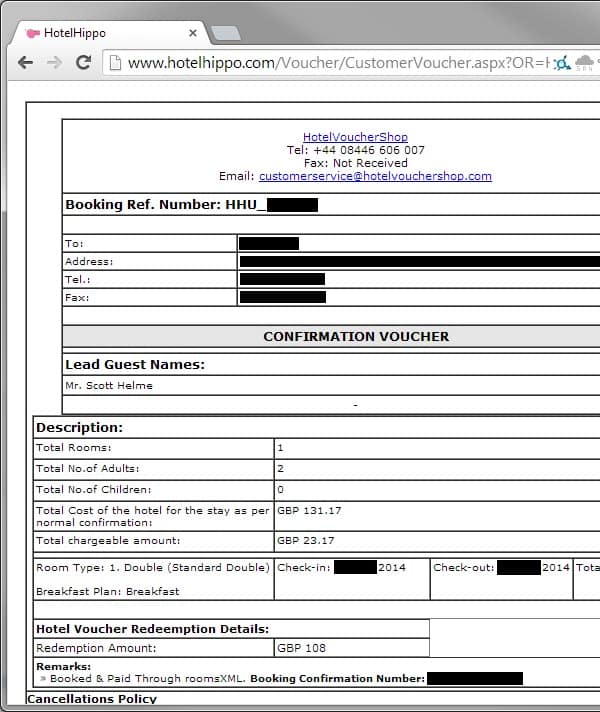
It includes lots of personal information, and dates and details of where you will be staying.
Unfortunately, what the page doesn’t do is authenticate that you are authorised to access the information.
Indeed, this part of the HotelHippo.com website is guilty of one of the easiest to exploit and most prevalent vulnerabilities found in website designs: insecure direct object references.
The vulnerability works like this.
A website gives you a URL to access your private information (such as your hotel booking).
The URL might take the form of something like this, where 123456 is your account number.
http://example.com/app/accountInfo?acct=123456
If the website does not properly authenticate if you are allowed to access that particular account (for instance, by asking for a password), then it’s child’s play for someone to simply change the account number in the URL.
For instance, here the account ID has been changed to access other users’ information:
http://example.com/app/accountInfo?acct=123457
http://example.com/app/accountInfo?acct=123458
Trust me, this isn’t rocket science.
Scott Helme found this elementary trick could be used against the Hotel Hippo website, and he could access the booking information of other customers – with possible alarming consequences:
with a little alteration of the number, we can start walking through the booking information of other customers too. At this point, an attacker has everything they could possibly need to launch a highly effective phishing attack against a user.
With name and address details it’s pretty easy to look up a phone number and place a very convincing phone call to the customer. You simply say you’re from Hotel Hippo, you know their name, address, post code, the hotel they’re staying at, when they’re staying there, whether they ordered breakfast or not, how many people are going and how many rooms they booked, numbers of adults, children etc… I mean, who else would know this information except somebody calling from the actual company?!
From here, they simply explain there was an issue with the card payment, they know the exact amount, and ask for card details over the phone to avoid having to cancel the booking.
Hey presto, you’ve bagged yourself some credit card data with minimal effort. What’s arguably even worse is that there’s also another risk that you’re exposed to.
And that’s just one of the problems that Helme found with the Hotel Hippo website.
Disappointingly, Hotel Hippo ignored Scott when he tried to inform them about the security issues with its website via email and telephone. It was only when BBC News picked up the story that the company realised any action was necessary, and they took the website offline earlier this week.
At the time of writing, Hotel Hippo’s website remains down.

The UK’s data privacy watchdog, the Information Commissioner’s Office (ICO), is said to have opened an investigation.
Who knows how much money the website downtime must be costing the company? Frankly, I couldn’t give a monkey’s about the financial losses inflicted to the business at the moment, as its website was treating its customers’ security with such disdain and recklessness.
And, if Hotel Hippo – who are owned by HotelStayUK – hired a third party to create the website for them I hope they are having a chat with their solicitors about how they might be able to claim some compensation for the shoddy work.
Hopefully whoever was responsible for the Hotel Hippo website is having a long, hard think about web security. Let’s hope that if the website ever comes back it will be properly engineered to protect users’ privacy and treat security as a high priority.

I can't understand the attitude of a company that refuses to take a call or investigate the claims of an insecure site. All of this could have been fixed without the BBC, and now you, telling the world about this. This is really a lesson in crisis and crisis communication and response. The company should be called hotelidiots.com or neverbookhere.com
There's another issue with the flaw you list (time/location of visit). It is similar to people on Facebook (I assume mostly kids but I don't know as I don't have a Facebook account although I've made fake facebook accounts in the past) who think everyone in the world cares what they do 24/7. That means a couple of things: 1) they are revealing when they are away from home so the home is now at risk (of whatever those abusing it decide); 2) they also show exactly where they will be when, should others want to harm them. Of course in this case it is worse: here they aren't willingly giving out that info. Scary? Yes. Surprising? You know the answer: absolutely not.
Couple comments:
Re: "Who knows how much money the website downtime must be costing the company?"
I don't know UK laws but I hope they are not able to file for bankruptcy protection because frankly it is theft (especially when bankrupt person/entity does it more than once, although that is another issue…). My view is the law is far too lenient in the US and it is really disgraceful (and really, avoiding debt by 'protection' is a serious issue).
Re:"Let’s hope that if the website ever comes back it will be properly engineered to protect users’ privacy and treat security as a high priority."
I'd rather word it:
Let's hope that the website never comes back and the winners of the ID10T award of x-2014 is held accountable (pun intended) for such disregard of their customers (and that may just include: no longer a company and being hit over the head with a certain silver hammer… OK, maybe not THAT far… but well, the idea is the same….).