
A really cool feature of Apple macOS, from the security point of view at least, is that all software distributed via the Mac App Store has to be checked by Apple for malicious content – a process known as “notarizing.”
It’s different from a regular “app review” of the software, and since February 2020 it has become a requirement for even Mac software distributed outside the Mac App Store to be notarized by Apple to allow it to run on macOS Catalina, the latest shipping version of the Mac operating system.
If an app isn’t notarized, you’re prevented from running it on macOS.

That’s all great in theory, but what if Apple accidentally approves a malicious app. Might users have a false sense of security – believing that if Apple’s vetting has given an app the all-clear and no message is displayed on running, that it must be safe to run?
Unfortunately, that seems to be exactly what has happened.
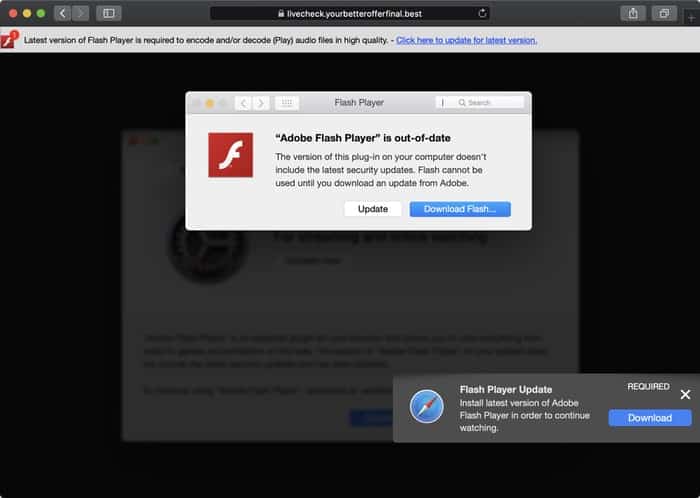
Security researchers Patrick Wardle and Peter Datini have uncovered an adware campaign hosted on a website that tricked users into downloading a bogus update to Adobe Flash Player.
Normally, a lack of notarization should mean that the app cannot be run on users’ Mac computers and laptops.
However, in this case, the malicious code had actually received Apple’s stamp of approval.
Wardle explains what this means:
- These malicious payloads were submitted to Apple, prior to distribution.
- Apple scanned and apparently detecting no malice, (inadvertently) notarized them.
- Now notarized, these malicious payloads are allowed to run …even on macOS Big Sur.
- Again, due to their notarization status, users will (quite likely), fully trust these malicious samples.
Oh dear oh dear oh dear.
And you know what’s worse? The malicious content contained within this fake Adobe Flash Player update is not some brand new breed of malware, but instead a version of Shlayer – a worryingly-common infection which has dominated the Mac malware charts since 2019.
When I first wrote about Shlayer in January 2019, it was posing successfully as a Flash Player update and it seems that the criminals behind the attacks haven’t felt any need to change that. But what they have done is make the disguise even more convincing by somehow duping Apple into approving their code as legitimate.
According to Wardle, once he notified Apple about the problem it was quick to revoke the certificates of the offending app – and thus remove the notarization status. But if cybercriminals managed to dupe Apple once into approving a bogus and malicious app, it would be a brave man who betted against it happening again…
Mac users, I know and you know that malware on your operating system of choice is nothing like as common as it is on Windows. But that doesn’t mean you are somehow magically immune from malicious attacks.
Anyone who cares about their Mac and the data they keep on it should ensure that they are running a Mac anti-virus product, and keeping it updated.


The fact that the hackers dared submit their software to Apple for approval and, on top of it all, the software got approved – i.e. passed a technical inspection process – means that the guys quite likely knew a lot about the vetting process steps. From where? How? I think this should actually be Apple's greatest concern.