 Hackers from the Syrian Electronic Army have once again claimed a high profile scalp, compromising the blogs at British broadcaster Channel 4.
Hackers from the Syrian Electronic Army have once again claimed a high profile scalp, compromising the blogs at British broadcaster Channel 4.
The hackers, who back the regime of President Bashar al-Assad, took over the blog of the station’s veteran news presenter Jon Snow and posted a story about a tactical nuclear strike against Syria.
Here’s a partial screenshot of what they posted, courtesy of Google’s cache of the webpage:

Claiming credit for the hack, the Syrian Electronic Army posted a screenshot of what appeared to be the WordPress admin panel for the Channel 4 blogs, something which should normally never be accessible to an unauthorised party.
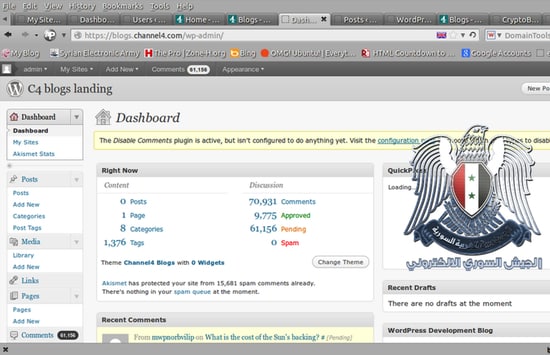
The suspicion has to be that Channel 4 was running an old version of WordPress, vulnerable to a security exploit that allowed the hackers to gain access, or that an administrator had his password phished. In the last few days, WordPress has released the latest version of its blogging platform – version 3.6.
At the time of writing, all of Channel 4’s blogs are inaccessible and have been replaced with a message saying “Something’s broken (or we’re making things better)” alongside a picture of character’s from the station’s comedy “The IT Crowd”:
Of course, the Syrian Electronic Army is no stranger to hacking media organisations, having successfully compromised the likes of the BBC, ITV, The Telegraph, The Financial Times, The Guardian, and Thomson Reuters.
Although clearly embarrassing for Channel 4, the good news is that this appears to have been merely defacement. Imagine how things would have been much worse if the hackers had used the opportunity of breaking into a popular blog to spread malware to unsuspecting readers.



When will people learn that wordpress should only be used to tell the world how many dogs or cats you have. Every day i encounter serious buinsesses using this swiss cheese of a platform, last week it was a large provider of secure ecommerce payment systems who now realise that 2 years down the line they have "perhaps made a mistake in using WP for their corporate website".
Give me strength….
From the screenshot of the admin panel, it looks as though the blog was up to date at the time the screenshot was taken. I think it is unlikely that the attackers would update WordPress after the compromise. I think it is more likely that the blog was compromised via a vulnerable plugin or theme.
Good detective work. Yes, that sounds plausible.
Of course, maybe the Channel 4 blog administrators were simply duped into handing over their password – or were unwisely using the same password in multiple places, or had chosen a password that was easy to guess.
Looking at the Google cached site it looks as though it was running version 3.1.2 at the time of caching (26 Jul 2013 10:57:29 GMT).
Version 3.1.2 suffers from Clickjacking, XSS and XML-RPC issues (SSRF) so this may have been the attack vector. Although a vulnerable plugin or theme maybe just as likely.
The account was hacked, I still question the content of the video. Any proof that is not real?