 Facebook may have refused to pay researcher Khalil Shreateh a bug bounty after he posted a message on Mark Zuckerberg’s Facebook page, but that doesn’t mean he’s going to go away empty-handed.
Facebook may have refused to pay researcher Khalil Shreateh a bug bounty after he posted a message on Mark Zuckerberg’s Facebook page, but that doesn’t mean he’s going to go away empty-handed.
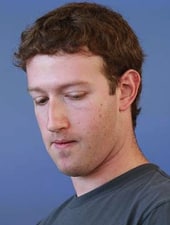
Shreateh posted the message on Zuckerberg’s Facebook page, exploiting the vulnerability he had discovered, after he become frustrated by the poor response from the social network’s security team. Irritated by their claim that he wasn’t reporting a bug, he effectively “went to the top” in order to get their undivided attention.
Shreateh lost the chance of receiving $500 or more from Facebook by breaking their guidelines for responsible investigation and disclosure of flaws on the site, much to the annoyance of many fellow security researchers and hackers online.
Well, if you were one of them, don’t despair. A fundraising campaign started by researcher Marc Maiffret has already raised over $12,000 for Shreateh.

Shreateh may have been unwise to have posted messages onto the Facebook pages of Zuckerberg and his college friend Sarah Goodin without permission, but it doesn’t look as though he’s going to miss out financially because of it.
If you are on Facebook, and want to be kept updated with news about security and privacy risks, and tips on how to protect yourself online, join the Graham Cluley Security News Facebook page.



A positive outcome, but I still think Emrakul (Facebook Security) should have all his cases reviewed.
Why didn't Zuckerberg gave Khalil the bounty? Because Khalil is Palestinian ?
(Born in the US) Probably yes, that is the reason. I would like to believe not but it's fairly obvious to most the world that there is that issue (more often than not). It is sad indeed but it seems so many Americans just do not know.
But I guess if nothing else it is once again shown that Mark only claims to take security seriously but unfortunately does not in reality take it so (how many times has this happened? This being his account being breached. More than once, any way). And while it might not change much for facebook users the truth is them ignoring the "non-bug" is a reason why exploits are written and that is good because it forces the vendor to fix it (instead of ignoring the information given originally) which will be discovered eventually and maybe by someone who wants to cause harm.