Twitter has patched an issue that allowed attackers to bypass protective measures for user accounts that have been locked.
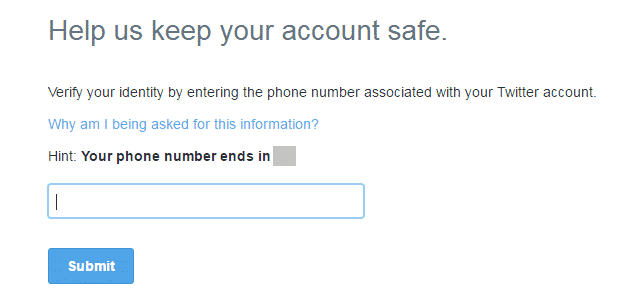
Like many web services, Twitter monitors user accounts for suspicious login activity. If it detects something that’s out of the norm, it restricts access and asks the user to enter in either the email address or phone number associated with the account. These enhanced security measures safeguard the Twitter account across every platform until the rightful owner verifies themselves.
At least… that’s what’s supposed to happen. But it wasn’t the case until recently.
Karan Saini first tried to bypass this verification procedure by logging in with his own credentials via mobile.twitter.com. When that didn’t work, he tried signing on at tweetdeck.twitter.com. Again, no luck.
It was then he remembered that he could add a Twitter account to an iPhone through the device settings. Kaboom. He logged on without a hitch.

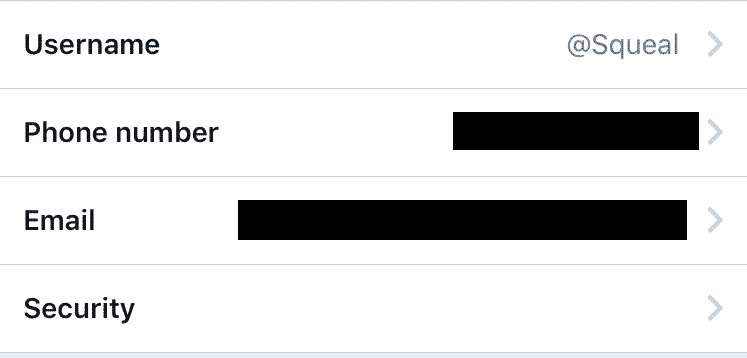
Saini had full reign of his Twitter account on his iPhone. But his account was still locked on his desktop. He needed to figure out a way he could obtain his phone number or email address and verify himself to complete the bypass. That’s when he had an idea.
As he explains in a blog post:
“I downloaded the Twitter app for iOS and found that my account was already logged in and ready to use. I navigated to account settings and found that the email address and phone number linked to my account were listed right there.”
Submitting this information into the desktop’s verification page allowed him to unlock his account.
Saini submitted a report about this issue back on 7 October 2016. Twitter triaged it the same day and marked it as “fixed” just four days later. A couple of days after that, it awarded Saini a bounty for practicing responsible disclosure.
For attackers to have successfully exploited this issue, they would have needed a user’s login credentials to first try to authenticate themselves. They could have stolen those details through a variety of means, including at least one truly deplorable scam.
Users can protect their Twitter accounts best by not clicking on suspicious links and email attachments
I would also recommend users enable two-step verification (2SV) on their accounts. Doing so will prevent attackers from accessing their accounts even if they obtain their login credentials.