Cybercriminals are spreading malware via torrent distribution networks, using an automated tool to disguise the downloads as trending audio, video and other digital content in an attempt to infect more unsuspecting victims.
Researchers at InfoArmor say they have uncovered a malicious torrent distribution network that relies on a tool called RAUM to infect computers with malware.
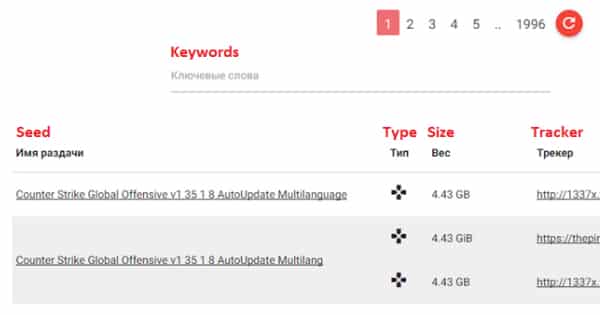
The network begins with a torrent parser, which collects information about some of the most popular torrent files circulating around the web.
Computer criminals then apply their RAUM tool to create a series of malicious files. Some are fake copies of those popular torrent files that in reality hide notorious malware such as CryptXXX, Cerber, or Dridex.
Others are weaponized torrent files, while others still are parsed torrent files that rely on a high download rating, a reputation which the attackers artificially inflate by abusing compromised users’ accounts to set up new seeds.
Like many attack campaigns in the underground web, the RAUM network operates according to an affiliate system.
InfoArmor explains:
“The so-called ‘RAUM’ tool has been actively used on uncovered underground affiliate networks based on a ‘Pay-Per-Install’ model (PPI). This model leverages paying cybercriminals to distribute malware through modified torrent files that are joined with malware.”
That type of framework allows the network’s administrators to carefully screen its members. In fact, no one is allowed to join without receiving an invitation from another pre-approved member.
Together, all of those malicious files provided by affiliates form the basis of the network’s seedbase, which admins manage using an easy-to-use dashboard.
Criminals monitor those files intently to see if anti-virus solutions have flagged any of them as suspicious. To protect against detection, some of the files are hosted on the Tor network.
All that remains is distribution. Initially, computer criminals relied on uTorrent, but now they’re using virtual servers comprised of hacked devices to get the job done.
This complex infrastructure has helped the computer criminals meet with quite a bit of success over the past few months, InfoArmor notes:
“According to expert statistics, malicious torrents infect over 12 million users a month, creating significant security risks for users on a myriad of platforms. In many instances, popular ransomware such as CryptXXX, CTB-Locker and Cerber, online-banking Trojan Dridex, password stealing spyware Pony, and others were associated with the identified RAUM instances. We have identified in excess of 1,639,000 records collected in the past few months from the infected victims with various credentials to online-services, gaming, social media, corporate resources and exfiltrated data from the uncovered network.”
To protect themselves against this campaign, users can reference the indicators of compromise included in InfoArmor’s blog post
It’s always a good idea to maintain an up-to-date anti-virus solution on computers and follow sensible precautions to avoid exposing their computers to malicious torrent files.


This has been going on by the entertainment industry and government for years.
What a bunch of crap the criminals are pulling on us.
What's the Punisher tie-in? Is it a sponsorship? Is Marvel paying you to show their logo? or did you pay them to use it?
Do you mean the skull image? That’s from the researcher’s infographic.
https://www.infoarmor.com/infoarmor-uncovers-malicious-torrent-distribution-network/