
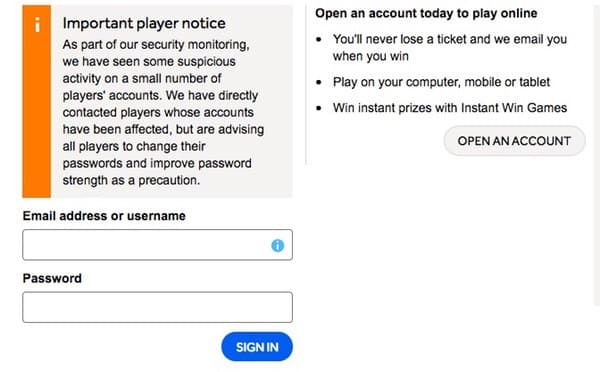
Camelot, operator of the UK’s National Lottery, has issued a warning that tens of thousands of players’ accounts have been accessed by hackers:
Of our 9.5 million registered online players, we believe that around 26,500 players’ accounts were accessed. A much smaller number – fewer than 50 – have had some activity take place within the account since it was accessed. This was limited to some of their personal details being changed – and some of these details may have been changed by the players themselves. However, we have taken the measure of suspending the accounts of these players and are in the process of contacting them to help them re-activate their accounts securely. In addition, we have instigated a compulsory password reset on the accounts of the 26,500 affected players. We are in the process of proactively contacting them to help them change their passwords, as well as giving them some more general online security advice.
Camelot is at pains to point out that its core systems and databases which could affect prize payment of National Lottery draws were *not* accessed. Instead, it seems likely that the hackers gained access to accounts because players were using the same usernames and passwords on other sites.
Camelot is forcing a password reset on accessed accounts, and I hope it will go further and encourage internet users to *always* use different passwords for different websites. Password re-use is a huge problem, and one that hackers are taking advantage of every day.
And it would be sensible for users who have had their National Lottery passwords reset to also make sure they are not using that same password anywhere else on the net.
Of course, remembering multiple different passwords is impossible for puny human brains. That’s why you should use a password manager which stores your passwords securely and remembers them for you. You then only have to remember one, complicated gobbledygook master password.
And it’s worth bearing in mind that if a hacker accessed your lottery account it’s possible that they also grabbed personal information that you might have stored in that account, and could be planning to exploit it with malicious intent.
I’m not a gambler myself, so I don’t play the National Lottery. However, I can’t find any evidence that Camelot offers a two-factor authentication (2FA) option for users who wish to have a higher level of protection over their lottery account. Of course, multi-factor authentication is no replacement for good password practices, but it does make life much harder for hackers.
Maybe all online lotteries should consider offering 2FA to their customers – after all, if it’s good enough account security for a bank…
It’s not the kind of thing you want to gamble about, after all.



I like 2SV but that's no substitute for a secure password. If every site uses 2SV it'll be a nightmare keeping track of the OTPs.
If a hacker breaches the password database, and it's securely hashed, then your password is safe. Change it once you receive notification of the breach just to be on the safe side.
If a hacker breaches the site then 2SV (or a secure password) won't make any difference because the system has been compromised.
2SV is mainly for users who choose weak, short or otherwise insecure passwords. If you've got a secure password (and use a password manager) then 2SV won't make much difference.
Some password managers even offer the choice of storing the OTP secret inside the database; this is like keeping all your eggs in one basket. If you choose to keep your OTP secret outside the database (e.g. via a dedicated 2SV authenticator app) then you're back to square one: keeping track of them and hoping you don't lose the device and causing yourself great inconvenience.
Having the option of 2SV is fine and dandy but for users who are already practising good password hygiene, the difference will be negligible. Save 2SV for high-security sites (e.g. banking) although these will normally have a 2FA option.
Unrelated to this article, but interesting to watch, is Graham's keynote speech – free to view on YouTube: https://www.youtube.com/watch?v=OOloRlq9CAs
This is such nonsense.
2FA is in addition to the password, and it does still help even if the database is compromised because it prevents the hacker logging in as the user and using the computer system's algorithms to carry out transactions. Carrying out transactions directly on a database is tricky, even assuming that the hacker is able to get update privileges on the database; update privileges are usually better protected than read-only privileges.
Most 2FA systems send an OTP to your phone so you don't need to remember them. Password managers do not provide the facility to store OTPs because they are only used once. The clue is in the name: One Time Password.
Don't use the fact that it isn't perfect as an excuse not to use it at all.
Techno, you clearly don't understand the technology let alone my point so please refrain from calling my comment nonsense until you can appreciate my logic.
> First of all there is a MASSIVE difference between 2SV and 2FA. Please read up on the difference:
https://paul.reviews/the-difference-between-two-factor-and-two-step-authentication/
> Secondly you have not read my comment correctly. I referred to the database being breached in my first comment. I then went on to say that in the second scenario [the site being breached] that: "2SV (or a secure password) won't make any difference because the system has been compromised." This is obvious, sound common sense.
> Thirdly 2FA systems don't use OTP – why? – because a user-entered OTP is NOT a second *factor*, it's a second *step*.
> Fourthly you don't understand how OTPs work. I'll explain it simply – there is a 'secret' which is responsible for generating the OTP. That secret can be stored in a password manager like 1Password (see instructions below) or a dedicated app like the Google Authenticator:
https://support.1password.com/one-time-passwords/
Again, and obviously, if your password manager gets compromised then so do your OTPs.
(Some systems rely on a code being sent to a mobile. That's another type of OTP which isn't used by many websites because of the cost. But that's still 2SV and not 2FA).
> I'm sorry Techno, your criticism makes no sense.
I'm not sure I entirely agree with you Bob.
2SV and 2FA does provide an additional safety net, even for users who are following sensible password practices. I don't believe they are only helpful for users who have chosen weak or easily-crackable passwords, or who have reused their passwords on different sites.
Take, for instance, the example of keylogging malware that steals passwords as they entered by users on login pages, or phishing attacks that grab users' passwords. These types of attacks are just as effective against strong, unique passwords as they are against weak ones.
2SV and 2FA provide an additional layer of protection for users who have had their passwords compromised in this way, and make it harder for the hackers to exploit their credentials.
I'm not saying that 2SV and 2FA is perfect by any means. But I would like to see more sites offer it.
Graham, my main point was that 2SV can be incredibly inconvenient for low-value accounts. If you lose your phone with the 'secret' stored on it then you have to contact technical support.
Depending upon the company this may take severa days as some offer email-only assistance. In the meantime an attacker may have gained access to your account and interfered with or even deleted your information. This has happened to Gmail customers before.
Or, if you go down the route of storing the 'secret' in a password manager then that becomes the central point of failure.
In terms of malware and trojans there's a great article written by Bruce Schneier. I'd actually not come across it before until now but it's worth a read and his points are still true today:
"An attacker using a man-in-the-middle attack is happy to have the user deal with the SMS portion of the log-in, since he can't do it himself. And a Trojan attacker doesn't care, because he's relying on the user to log in anyway."
"Two-factor authentication is not useless. It works for local login, and it works within some corporate networks. But it won't work for remote authentication over the Internet."
https://www.schneier.com/blog/archives/2005/03/the_failure_of.html
Another article written by Egor Homakov makes the following observation before providing examples:
"There’s no plausible attack scenario where simple password + 2FA is better than good complex password alone."
http://sakurity.com/blog/2015/07/18/2fa.html
I therefore stand by my original viewpoint that for users practising good password hygiene, there is a negligible increase in security.
I do use 2SV for email and banking in the vain hope it'll make it slightly more difficult for casual attackers. I realise it'll offer little (if any) protection if the whole system is compromised.
Yes, if your whole system is compromised then all bets are off. Especially if the attacker is specifically interested in what you're doing and getting into *your* accounts.
And yes a man-in-the-middle attack can in theory waltz past the additional layer of authentication. But how much malware is doing a MiTM attack on the National Lottery or MailChimp accounts, I wonder? Isn't that kind of effort more likely to be expended on high value accounts (such as banking)?
It's often the case that the attacker is actually interested in hacking as many folks as easily as possible. In which case, the presence of 2SV or 2FA may mean that the bad guys judges you "too difficult/not worth the effort" and moves on from you to an easier victim to exploit.
I think it's too easy for us in the security industry to get hung-up on the 100% technical fact of what is possible than the reality of what is happening.
Regarding the loss of a phone carrying an authentication app. Yes, that would be a nuisance I agree and it's something I have experienced.
For that reason I have my authentication app automatically sync an encrypted copy of its data with other devices under my control. Access to the authentication app is further protected by a PIN code/fingerprint scan.
Is it 100% foolproof? No. But I feel safer having 2SV enabled on my accounts which allow it than not.
I agree with your points particularly about getting too "hung-up on the 100% technical fact of what is possible than the reality of what is happening."
I 'feel' safer with 2SV because I know that, absent full system compromise, it should in theory by slightly more difficult if 2SV is enabled – excluding those who are being personally targeted. But I'm conscious of trojans and malware too; I have some protection against that: anti-virus, firewall and some other things going on in the background.
To a large extent it's convenience over security. Because I use a password manager I tend not to use 2SV for the majority of my accounts. I also change some of my high-value account passwords quarterly.
I know changing passwords is considered unnecessary by some but my take on it is this: because I don't need to memorise the password then it's better to change it in case the back-end database has been compromised without my knowledge (like Yahoo was) and is then subsequently fixed but the hackers have had time to work on the hashes. If they've not hashed it properly (or stored it insecurely) then eventually a hacker would have access to my online account. Ironically 2SV helps here assuming that the password database is the only thing compromised and, because we're talking about high value accounts, I'd be using 2SV in this scenario.
Changing passwords frequently when you've committed them to memory (i.e. not stores in a password manager) is not a good idea for the reasons you've given in previous blog posts – it encourages bad passwords, writing them down and insufficient entropy.
I've also encountered companies who'll switch off 2SV if you phone up Customer Services and say you know your password but don't have access to the app. That's a problem with the company.
My 2SV 'secrets' are backed up securely offline as it can be a massive inconvenience if they're not.
Their site is the worst for password security. No 2FA and the password text change still states "numbers and letters". Doesn't mention you now can use special characters (you never used to be able to) and doesn't mention upper case characters. It really is poor.
The National Lottery website does allow complex passwords, for example a 20 character password that contains both upper and lower case letters, numbers and special characters is accepted. However, they still do not offer 2FA, which for a website that deals with money, this is unforgiveable.