
A hacker defaced a presidential campaign fundraising website for Donald Trump with a little help from a DNS misconfiguration issue.
On 19 February, an actor known as “Pro_Mast3r” defaced the site secure2.donaldjtrump.com.
The site’s server, which is down as of this writing, was not linked from the Trump Pence campaign website. However, its certificate was legitimate. That suggests in all likelihood that Donald Trump, who took until early January 2017 to agree that Russia had hacked the DNC back in June 2016, actually used the server to fund his presidential campaign.
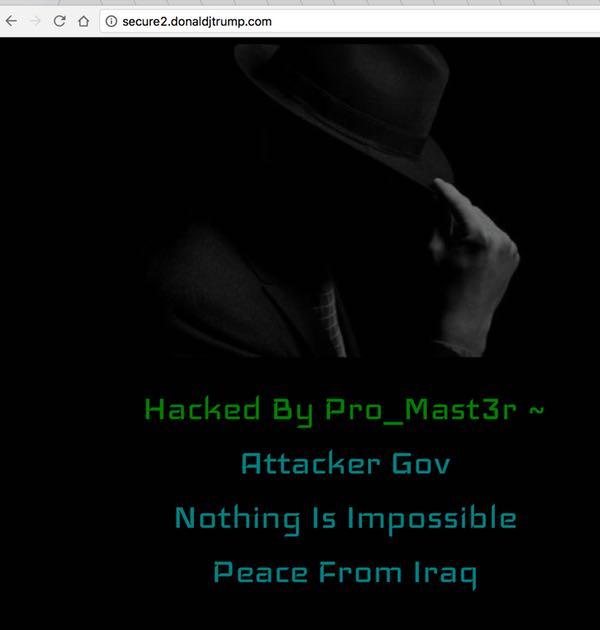
The hacker replaced secure2.donaldjtrump.com with an image of a man wearing a fedora. The attacker also left a message.
“Hacked By Pro_Mast3r ~
Attacker Gov
Nothing Is Impossible
Peace From Iraq.”
Not much is known about Pro_Mast3r other than the fact that his source code linked to JavaScript hosted on a now-disabled Google Code account under the name “masterendi.”
However, we do know that the actor apparently reached out to security blogger Brian Krebs and told him about how he pulled off the hack.
the Iraqi hacker who took credit for the Trump site "defacement" told me he used this https://t.co/E1vz93It4n from Oct. 2014..
— briankrebs (@briankrebs) February 20, 2017
It appears the hacker exploited a DNS misconfiguration to assume control of the donaldjtrump subdomain.
The attack vector works when an attacker signs up with a service to which a subdomain operated by the domain owner points. In most cases, the owner originally created this link some time ago but forgot to remove the DNS entry when they stopped using the service.
All an actor needs to do is sign up with one of 17 vulnerable service providers such as GitHub, Shopify, or Tumblr and claim the unused subdomain as their own. In many cases, the DNS-entry configurations allow the actor to assume control of the subdomain without notifying the domain owner. With that access, the nefarious individual can then get up to all sorts of trouble.
As explained by Detectify Labs in a blog post:
“Attacker can now build a complete clone of the real site, add a login form, redirect the user, steal credentials (e.g. admin accounts), cookies and/or completely destroy business credibility for your company.”
Detectify has detected more than 100 ways by which a domain owner could suffer a subdomain takeover.
For that reason, Donald Trump’s IT people need to do a better of job of checking the DNS configurations for subdomains that are currently not in use. They might also want to consider using a solution that scans for subdomain takeover attacks.


Dear Mr. Bisson:
These PP heads don't understand the first thing about getting fed. If you didn't have businessmen starting businesses, there wouldn't be jobs for those whose testicular fortitudes are not big enough to start businesses. People who take chances of various types have fortitudes which are large, made of brass and clank when they walk. The detractors "fortitudes" are made of pablum mush.