
Researchers have spotted a new mobile malware family called “Godless” that is capable of rooting 90% of all Android devices.
Veo Zhang, a mobile threats analyst for security firm Trend Micro, doesn’t waste any time putting the threat into perspective in a blog post:
“We came across a family of mobile malware called Godless (detected as ANDROIDOS_GODLESS.HRX) that has a set of rooting exploits in its pockets. By having multiple exploits to use, Godless can target virtually any Android device running on Android 5.1 (Lollipop) or earlier. As of this writing, almost 90% of Android devices run on affected versions.”
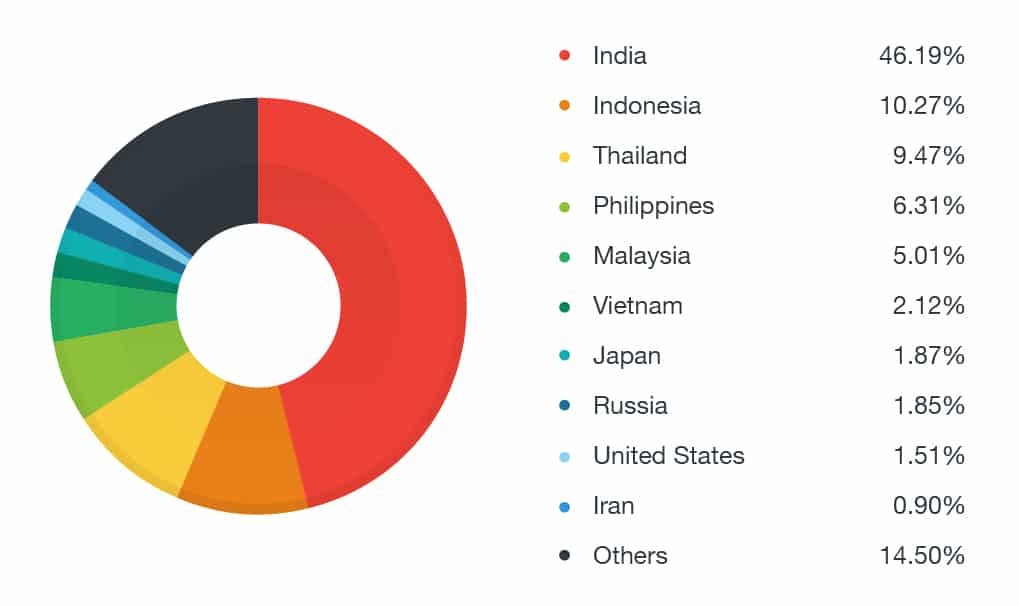
Godless is believed to have affected 850,000 devices so far, with nearly half (46.19%) of its infections occurring in India.
The mobile malware relies on android-rooting-tools, a rooting framework that scans an infected Android device for vulnerabilities. In particular, Godless keeps an eye out for two vulnerabilities: CVE-2015-3636 (used by the PingPongRoot exploit) and CVE-2014-3153 (used by the Towelroot exploit).
Early variants of the malware family relied on a local exploit binary called libgodlikelib.so to do their dirty work. Once a user installed a malicious app that came pre-packaged with this binary, attackers would remotely turn the device screen off, run the rooting routine, and drop a hard-to-remove system payload onto the device.

It would appear, however, that later version of Godless have evolved. The Trend Micro security analyst explains:
“Recently, we came across a new Godless variant that is made to only fetch the exploit and the payload from a remote command and control (C&C) server, hxxp://market[.]moboplay[.]com/softs[.]ashx. We believe that this routine is done so that the malware can bypass security checks done by app stores, such as Google Play.”
The mobile malware masquerades as harmless-looking mobile apps, including this Summer Flashlight app:
Several clean apps on Google Play also share the same developer certificate with malicious versions containing the Godless code. This means there is the potential for a user to be upgraded to a malicious version of an app without their knowledge.
If and when that infection occurs, Godless won’t lock their screen and demand hundreds of dollars in ransom. Neither will it place calls to mysterious Chinese phone numbers. Instead it will have the ability to download any app it chooses, including those that spam users with ads and/or install backdoors onto an infected device.
Android users don’t want to come across Godless, which is why Veo Zhang offers the following advice:
“When downloading apps, regardless if it’s a utility tool or a popular game, users should always review the developer. Unknown developers with very little or no background information may be the source of these malicious apps. And as a general rule, it is always best to download apps from trusted stores such as Google Play and Amazon.”
Users should also consider installing an up-to-date anti-virus solution on their devices.



How is an anti-virus app going to protect against THIS malware?