Today saw the publication of a fascinating research paper by the Information Warfare Monitor project.
The paper, entitled “Tracking GhostNet: Investigating a Cyber Espionage Network”, investigates claims of alleged Chinese spying against Tibetan organisations including the Tibetan government-in-exile and the private office of the Dalai Lama.
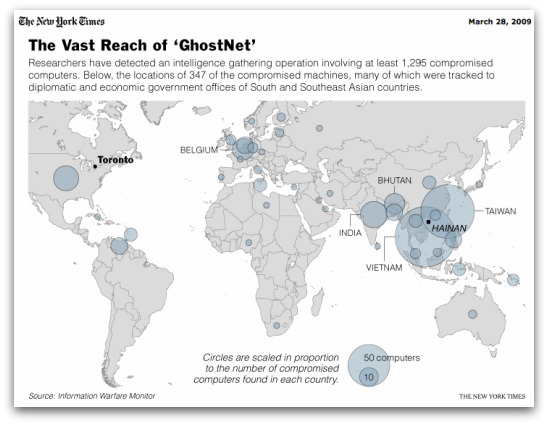
However the investigation also uncovered evidence of a more widespread cyber espionage network, which the paper’s authors dubbed GhostNet.
According to the paper, GhostNet consisted of at least 1,295 compromised computers in 103 different countries. Many of the affected computers are said to belong to foreign ministries and embassies, as well as the offices of the Dalai Lama and the Tibetan goverment-in-exile.
Although the research paper examining GhostNet makes interesting reading, there’s one thing missing. There’s no smoking gun.
At no point does it gather enough evidence to prove, conclusively, that the Chinese government or the People’s Liberation Army are behind the attacks. Just because Chinese computers are used in the scheme, does not mean that the Chinese authorities are behind the operation.
Let me give you an illustration which helps explain this point.
If you were to investigate the IP address of the computer which sent spam into your mailbox today you’d probably find a good proportion of it came from a PC based in China. Going by the latest stats that we produced, 9.9% of spam is coming from that part of the world.
But you probably aren’t finding that 9.9% of your spam is in Chinese, or selling Chinese goods. You’ll probably find that a lot of it is promoting pharmaceuticals coming out of North America, Russian brides, or a cheap college diploma.
In other words, cybercriminals around the world are taking advantage of poorly-protected computers in China (and elsewhere) to launch their attacks. Just because a Chinese computer is implicated, it doesn’t mean that China itself is behind the attack.
At the same time, lets not fall into the trap of naivety. We would be fools to believe that countries would consider the internet and spyware “off-limits” as a tool for espionage. Countries are spying on each other all across the world for political, commercial and military advantage – and they would be nuts not to try and exploit the power of the internet to increase their chances of success.
I’m sure China is using the net to spy on governments and businesses overseas for commercial, diplomatic and possibly military advantage. But then I’m sure that the United States, Israel, the United Kingdom and others are doing it too.
But lets not make the mistake of thinking that an investigation like this necessarily proves a country’s involvement.
What can be learnt from this paper, however, is the importance of properly protecting your organisation with a layered defence, including proactive and reactive anti-virus technology, firewalls, security patches, network access control, encryption and so forth.
If you want to find out more about GhostNet, I would recommend you read this article by the New York Times and the Associated Press.
Some further reading from the archives:
- Critical infrastructure organisations targeted by hackers
- Businesses warned by MI5 of Chinese espionage threat
- Fingers pointed at Chinese military after hacking reports